
Institutional asset security is no longer defined by custody alone.
After more than a decade of evolution—from Web2 financial systems to Web3 infrastructure—the industry has learned a critical lesson:
Security failures don’t begin with lost keys — they begin with broken architecture.
Modern institutional security is built on three pillars:
With over a decade of experience across blockchain and financial systems, the shift is clear:
custody has evolved from simple key management into full-scale security architecture engineering.
Protecting digital assets today is no longer just about safeguarding private keys. It’s about coordinating:
All within a unified institutional framework.
Institutional asset security in 2026 is the coordination of ownership, control, and execution over digital assets.
It ensures that governance policies, compliance requirements, and risk management systems work together to prevent loss from:
For example, a family office may split custody between:
This approach balances security, auditability, and operational speed.
Institutional-grade security is no longer about hiding keys.
It is about designing systems that enforce:
Most modern security failures are no longer cryptographic.
They are organizational.
| Dimension | Early Crypto Era (2015–2020) | Institutional Reality in 2026 |
|---|---|---|
| Primary Risk | External hacks | Internal governance & operational failure |
| Attack Vector | Private key theft | Misconfigured permissions, signer misuse |
| Failure Speed | Instant | Slow, compounding over time |
| Accountability | Minimal | Legal, regulatory, fiduciary |
| Recovery Focus | Key backups | Governance continuity & disaster recovery |
This shift explains why MPC vs Multi-Sig custody is now a critical institutional decision—not just a technical preference.
Early crypto security focused almost entirely on protecting private keys from hackers.
In 2026, the threat landscape is very different.
Institutions must now defend against:
This is why layered custody models and hybrid architectures are becoming the standard.
For example, a trading firm may:
The objective is simple:
eliminate single points of failure without slowing operations

The rapid rise of cross-chain assets, tokenized finance, and stricter regulations has forced institutions to rethink how custody actually works.
Legacy single-key security is no longer viable.
Modern institutional crypto custody security now depends on:
As a result, institutions are shifting toward Multi-Sig, MPC, and hybrid custody architectures that balance security with operational speed.
External hacks are no longer the dominant risk.
Today, most institutional losses come from inside the system, not outside it.
Common failure points include:
This fundamentally changes how institutional crypto custody security must be designed.
The goal is no longer just blocking attackers—
it’s preventing authorized users from breaking the system. ↑ Back to FAQs Menu
As institutions scale, governance itself becomes exploitable.
Risks now include:
To mitigate this, institutions implement:
A secure system in 2026 is one that can survive decision-level failures, not just technical ones.
Cyberattacks are no longer the top concern; internal mismanagement dominates institutional losses. Missed approvals, delayed revocations, or poor signer distribution often outweigh external hacking risks. Firms increasingly invest in operational resilience, automated policy engines, and audit-ready processes to mitigate these vulnerabilities.
Most institutional losses today originate from:
Institutional Asset Security 2026 must therefore defend against authorized misuse, not just unauthorized access. The challenge is no longer keeping attackers out—it is preventing legitimate participants from unintentionally or maliciously breaking the system. ↑ Back to FAQs Menu
Multi-Sig wallets use an M-of-N approval model. Transactions require a predetermined number of signers to approve, ensuring no single actor can move funds. On-chain execution provides full transparency.
Example: A DAO requires 4-of-6 signers to approve any transaction over $50k, creating a permanent blockchain audit trail.
In institutional asset security, a Qualified Custodian (QC) is a regulated financial entity that has been granted legal authority to hold and safeguard assets on behalf of investors (like hedge funds, pension funds, or family offices).
While a “custodian” is just anyone holding your keys, a “Qualified” custodian meets the rigorous standards of the SEC (Securities and Exchange Commission) and other global regulators. In 2026, this designation is the “Gold Standard” for Institutional Crypto Custody.
| Problem | Objectives | Analysis / Situation | Implementation | Challenges | Results / Outcomes |
| An institutional fund used a standard “Exchange Wallet” for 500 BTC. | Meet the SEC 2026 Safeguarding Rule. | The exchange was not a “Bank” and commingled client funds. | Moved assets to a Qualified Custodian (State Trust Co). | Transferring large volume without market slippage. | Success: Fund passed its institutional audit and attracted $50M in new capital. |
Compliance is architectural. SOC 2 / ISO 27001 alignment, fiduciary responsibility, and deterministic audit trails are critical. Multi-Sig aligns naturally with on-chain compliance, while MPC relies on off-chain attestations. Both models can meet regulatory demands, but with different transparency levels.
| Compliance Requirement | Multi-Sig | MPC |
|---|---|---|
| Deterministic Audit Trail | Strong | Moderate |
| On-Chain Evidence | Native | Limited |
| SOC 2 / ISO Alignment | Easier | Requires documentation |
| Fiduciary Clarity | High | Depends on contracts |
| Jurisdictional Reporting | Transparent | Attestation-based |
Multi-Signature custody uses an M-of-N approval model.
Example:
Key advantages:
Tradeoffs:
| Feature | Multi-Sig |
|---|---|
| Approval Model | M-of-N |
| Execution Speed | Medium |
| On-Chain Visibility | High |
| Signer Flexibility | Low ↑ Back to FAQs Menu |
A strategic breakdown for institutional treasury design:
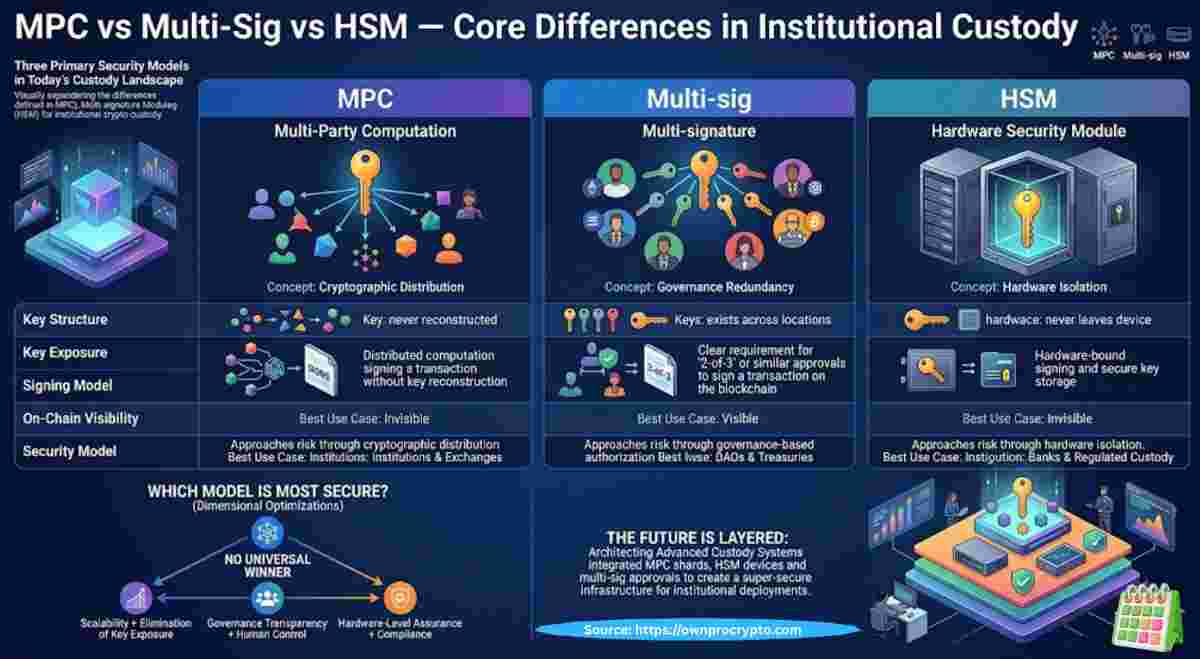
MPC introduces a fundamentally different approach to security.
Instead of multiple keys, MPC uses distributed cryptographic computation.
Private keys are never fully created or exposed.
Ownership means nothing without controlled execution.
Multi-Sig minimizes unilateral authority
MPC minimizes key exposure
Multi-sig ensures no single actor can act alone.
MPC ensures no single actor ever holds the key.
Neither is superior.
They defend against different failure modes. ↑ Back to FAQs Menu
MPC prioritizes speed, flexibility, and abstraction, while Multi-Sig prioritizes transparency and governance control
Multi-Sig emphasizes on-chain governance; MPC emphasizes off-chain execution velocity. Multi-Sig is auditable and transparent but slower; MPC is fast and flexible but opaque. Hybrid models merge both, creating layered security that separates speed from sovereignty.
Example Table:
| Feature | Multi-Sig | MPC | Hybrid |
|---|---|---|---|
| On-chain visibility | High | Low | Medium |
| Transaction speed | Moderate | High | High for hot wallets |
| Governance enforcement | Strong | Moderate | Strong via Multi-Sig layer |
| Signer flexibility | Low | High | High in MPC layer |
| Regulatory audit alignment | Excellent | Moderate | Excellent via Multi-Sig |
Choose Multi-Sig when governance outweighs speed. It excels for DAO treasuries, protocol-owned liquidity, or public foundations where auditability and distributed authority are critical. ↑ Back to FAQs Menu
| If Your Priority Is… | Choose This Model |
|---|---|
| Maximum transparency | Multi-Sig |
| High transaction velocity | MPC |
| Regulatory defensibility | Multi-Sig |
| Cross-chain scalability | MPC |
| Balanced institutional control | Hybrid |
A single point of failure exists when one entity can control or disrupt asset movement.
Example:
A family office moving from a single-key wallet to a 3-of-5 Multi-Sig setup eliminates unilateral control risk, while adding MPC for operational wallets improves speed and flexibility.
This combination creates resilient, failure-tolerant systems.
Humans dominate loss events. Missed approvals, poor signer distribution, and emergency delays account for the majority of failures. MPC reduces friction but increases infrastructure dependency; Multi-Sig improves auditability but slows operations
| Risk Category | Multi-Sig Impact | MPC Impact |
|---|---|---|
| Missed Approvals | High risk | Low risk |
| Signer Availability | Critical dependency | Abstracted |
| Vendor Dependency | Low | High |
| Emergency Response | Slow but deliberate | Fast but opaque |
| Human Error Surface | Distributed | Concentrated in provider |
A single point of failure exists when one person or system can execute or disrupt asset flows. Multi-Sig disperses authority among several signers, while MPC eliminates single-key exposure entirely. Hybrid models combine both, ensuring operational agility without compromising control.
Example: A family office previously used one private key for all assets. Moving to 3-of-5 Multi-Sig removed the single point of failure.↑ Back to FAQs Menu
Recovery planning is essential. Institutions must prepare for signer loss, vendor shutdown, chain halts, or legal seizures. Hybrid models combined with geo-redundant “break-glass” keys offer the most resilient framework.
MPC is best suited for environments where speed, flexibility, and cross-chain execution are critical.
Typical use cases include:
Because MPC operates off-chain and supports dynamic signer rotation, it significantly reduces coordination delays.
This makes it the preferred model for execution-heavy institutional workflows
| Criteria | Multi-Sig Custody | MPC Custody |
|---|---|---|
| Key Exposure | Full keys exist | Keys never reconstructed |
| Audit Transparency | Fully on-chain | Off-chain attestations |
| Execution Speed | Slower (coordination required) | Near-instant |
| Signer Rotation | On-chain change required | Off-chain, seamless |
| Chain Support | Chain-specific | Blockchain-agnostic |
| Governance Strength | Very high | Moderate |
| Operational Flexibility | Limited | High |
This table directly supports “MPC vs Multi-Sig custody” search intent and improves snippet eligibility.
No custody model completely removes risk.
Instead:
The objective is not eliminating risk—but controlling where risk exists.
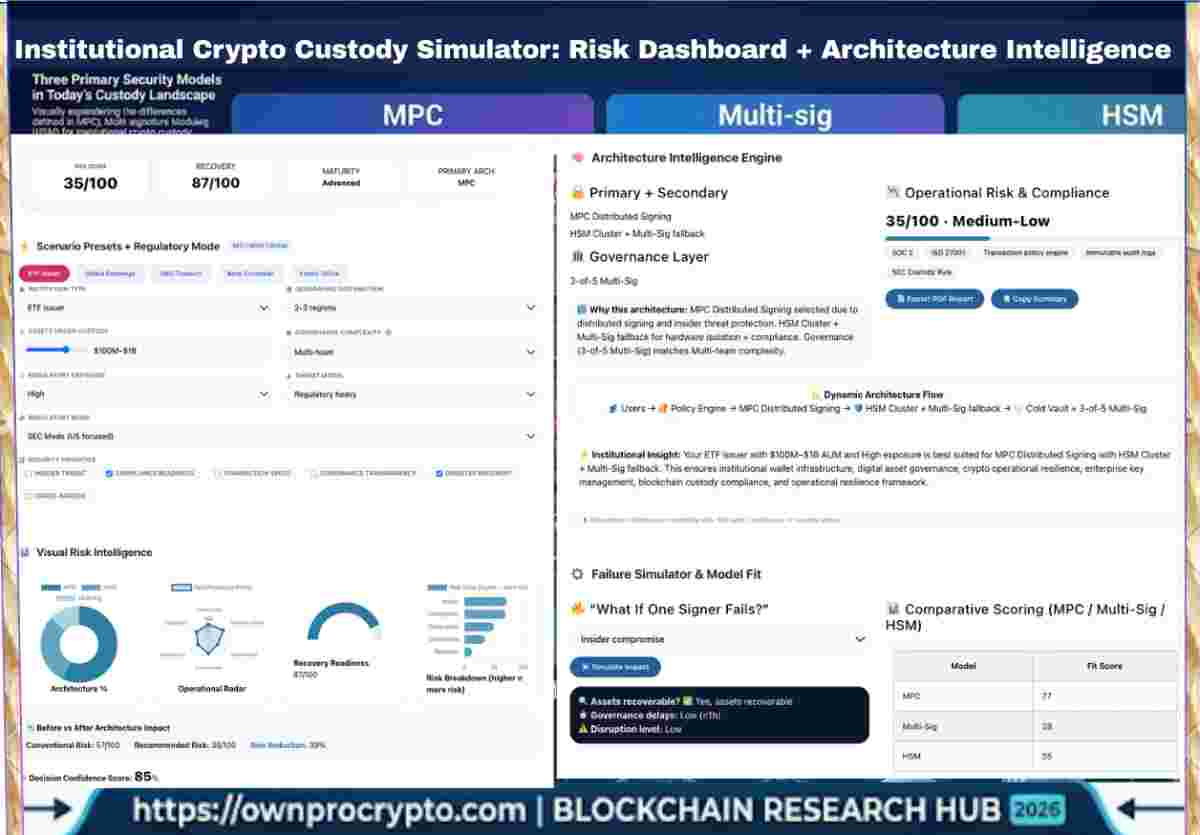
Hybrid custody has emerged as the default institutional architecture.
It separates:
Modern systems also integrate:
This aligns directly with crypto custody security models and strengthens topical authority.↑ Back to FAQs Menu
| Institution Type | Dominant Model in 2026 | Reason |
|---|---|---|
| DAO Treasuries | Multi-Sig | Public accountability & consensus |
| Trading Firms | MPC | Speed & cross-chain execution |
| Family Offices | Hybrid | Governance + flexibility |
| Asset Managers | Hybrid | Compliance + operational scale |
| Market Makers | MPC | Latency-sensitive operations |
Leading institutions now combine both models.
Example:
This creates:
This is considered the gold standard institutional custody architecture in 2026
Secure custody starts with key management design.
Modern approaches:
Both MPC and Multi-Sig improve resilience—but in different ways
Single-key custody concentrates risk into one point of failure.
If that key is lost or compromised:
the entire portfolio is at risk.
Modern institutions managing large digital asset portfolios no longer rely on single-key systems.
Instead, they distribute control across multiple parties and systems.
The right choice depends on:
regulatory requirements vs operational needs
DAOs rely on Multi-Sig to enforce distributed authority and visible accountability. Proper signer distribution and governance rules prevent capture and misuse while maintaining protocol compliance. ↑ Back to FAQs Menu
Whether on-chain transparency is “better” depends entirely on your On-Chain Compliance requirements. Multi-Sig is superior for public accountability because every signature and signer change is recorded directly on the blockchain, making it easy for external auditors to verify “who moved what” in real-time. Conversely, MPC is often preferred for privacy-conscious enterprises because the “signing” happens off-chain (between shards), meaning only the final transaction is visible on the ledger. While MPC offers better “Digital Survivability” against targeted attacks, it requires specialized cryptographic audit logs to prove internal authorization to regulators.
MPC (Multi-Party Computation) is chain-agnostic because it signs transactions at the protocol level before they ever hit the blockchain. This means one MPC setup can support almost any asset (Bitcoin, Ethereum, Solana, etc.) seamlessly. In contrast, Multi-Sig is “on-chain” logic; it must be custom-built for every specific blockchain (e.g., a Safe wallet on Ethereum won’t work for Bitcoin), making it less efficient for diverse Web3 Ecosystem portfolios.
Case Study Success: A 2025 fund moved their On-Chain Asset Management to an MPC provider. They were able to secure 12 different blockchains under one security policy, achieving 100% Capital Efficiency without managing 12 different multi-sig smart contracts.
Security is evolving from “who holds the key?” to “who can do what, when, and why?” Programmable custody, AI-assisted risk monitoring, and conditional execution are the next frontiers. Institutions must adopt modular, adaptable security infrastructure to remain sovereign. ↑ Back to FAQs Menu
In a Multi-Sig setup (e.g., 2-of-3), losing one key is manageable as long as you maintain the threshold; however, if you fall below that number (losing 2 of 3), the funds are permanently locked on-chain. In contrast, MPC (Multi-Party Computation) offers a “seedless” recovery. Because the private key is never fully assembled, if a device or “share” is lost, the system can cryptographically rotate or regenerate a new share to a new device without changing the wallet address or requiring a clunky on-chain contract update. This makes MPC significantly more resilient for evolving teams where hardware loss or personnel changes are a reality
Table: How the Institutional Threat Model Changed (Early Crypto → 2026)
| Dimension | Early Crypto Era (2015–2020) | Institutional Reality in 2026 |
|---|---|---|
| Primary Risk | External hacks | Internal governance & operational failure |
| Attack Vector | Private key theft | Misconfigured permissions, signer misuse |
| Failure Speed | Instantaneous | Slow, compounding over time |
| Accountability | Minimal | Legal, fiduciary, regulatory |
| Recovery Focus | Key backup | Governance continuity & disaster recovery |
Why this works:
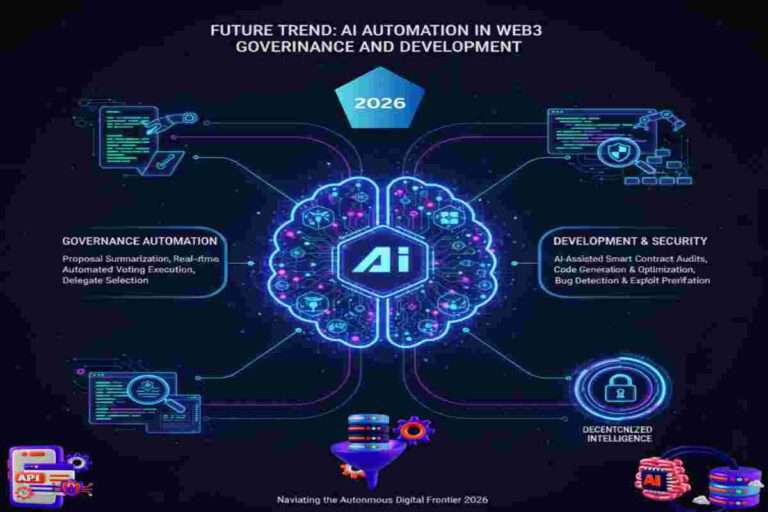
In 2026, AI is not a decision-maker in institutional custody.
It is an execution layer.
Institutions retain full control over:
AI automation exists to enforce those rules consistently across time, teams, and blockchains.
In practice, AI automation:
Examples include:
The key principle:
Decision-making remains human — execution becomes automated. ↑ Back to FAQs Menu
| Layer | Human Role | AI Role | Control Impact |
|---|---|---|---|
| Strategy | Define risk & governance | None | Fully human |
| Policy | Define custody rules | Validate consistency | Human-controlled |
| Execution | Approve systems | Execute automatically | Delegated |
| Monitoring | Define risk signals | Detect anomalies | Prevents silent failure |
| Recovery | Authorize overrides | Trigger safeguards | Human override |
As custody systems scale, the biggest risk is no longer cryptographic failure—
it’s inconsistent execution of rules
AI solves this by ensuring:
From a compliance perspective:
This preserves:
AI does not replace custody models—it strengthens them.
Together, they form a layered institutional custody architecture
Audit-First Treasurer
High-Velocity Trading Firm
DAO Treasury Manager
| Case | Model Used | Outcome |
|---|---|---|
| Pension Fund Treasury | Multi-Sig | 90% faster audit prep |
| Cross-Chain Trading Firm | MPC | 35% efficiency gain |
| DAO Treasury | Multi-Sig | Zero unilateral control |
| Exchange Recovery Setup | MPC + HSM | Eliminated spoofing risk |
A pension fund required full audit visibility for regulatory reporting.
Solution:
Result:
A trading firm needed secure, high-speed execution across multiple chains.
Solution:
Result:
Ensure your custody system can evolve:
Security is not just keys—it’s rules.
Implement:
Even advanced systems fail due to human error.
Best practices:
Always maintain:
Best practice in 2026:
This balances speed + control
Institutional security is evolving beyond custody.
From:
“Who holds the key?”
To:
“Who can act, when, and under what conditions?”
| Trend | Impact |
|---|---|
| Programmable Custody | Rules embedded into assets |
| AI Risk Monitoring | Early detection of anomalies |
| Post-Quantum Readiness | Future-proof key systems |
| Custody → Control | Security becomes execution logic |
Institutional asset security is not a standalone function.
It is the control layer of the entire Web3 ecosystem, connecting:
Without it:
no system can operate securely at scale
In institutional asset security, a Qualified Custodian (QC) is a regulated financial entity that has been granted legal authority to hold and safeguard assets on behalf of investors (like hedge funds, pension funds, or family offices).
While a “custodian” is just anyone holding your keys, a “Qualified” custodian meets the rigorous standards of the SEC (Securities and Exchange Commission) and other global regulators. In 2026, this designation is the “Gold Standard” for Institutional Crypto Custody.
| Problem | Objectives | Analysis / Situation | Implementation | Challenges | Results / Outcomes |
| An institutional fund used a standard “Exchange Wallet” for 500 BTC. | Meet the SEC 2026 Safeguarding Rule. | The exchange was not a “Bank” and commingled client funds. | Moved assets to a Qualified Custodian (State Trust Co). | Transferring large volume without market slippage. | Success: Fund passed its institutional audit and attracted $50M in new capital. |
To help you navigate the complexities of decentralized decision-making in 2026, we have organized the most critical inquiries into thematic groups. This ensures you can quickly access expert insights rooted in real-world successes and historical failures. Real Questions from Community, Answer by Expert, just click any question to reveal the insight.
As we move further into 2026, the necessity for robust Corporate Asset Safeguarding has never been higher. Protecting Institutional Property Protection is no longer a peripheral IT concern but a core boardroom priority that requires a proactive approach to Asset Risk Management. By integrating advanced Enterprise Security Management with specialized Asset Protection Services, firms can ensure that their digital footprint remains resilient against both internal and external threats. Achieving true Corporate Risk and Asset Protection requires constant vigilance and an unwavering commitment to Asset Integrity Management. Ultimately, organizations that master Enterprise Asset Risk Control today will be the ones that define the standards of trust and safety in the decentralized global economy of tomorrow.
Crypto Investors & Institutions Welcome!
Join our community:
https://www.facebook.com/groups/2430833834044955
https://www.linkedin.com/in/salim-sultanali-a3599833b/
If you’re a crypto enthusiast, investor, or part of an institution, this group is built for you. We provide prompt replies and aim to give reliable solutions for all your crypto-related queries.
We have also built 200+ Crypto resources to help members learn, research, and grow in the crypto space.
Come join us and grow together! 📈
The Markets in Crypto-Assets (MiCA) regulation, which went into full effect in 2024, has established the European Union as the first major jurisdiction with a comprehensive legal framework for digital assets. For institutional stability, MiCA mandates strict oversight for Asset-Referenced Tokens (ARTs) and E-Money Tokens, requiring issuers to maintain high-quality liquid assets (HQLA) and provide 1:1 redemption rights at par. According to the U.S. Treasury (TBAC Q4 2024 report), such regulatory guardrails are essential to prevent the “fire-sale” risks associated with unbacked private currencies, effectively forcing stablecoins to behave more like regulated money market funds or narrow banks to ensure global financial stability. ↑ Back to FAQs Menu
Welcome to OwnProCrypto (Own & Pro Crypto) — a next-generation Bitcoin and blockchain education platform where the science of finance meets the power of AI-driven automation.
Our mission is simple: to equip you with the knowledge, frameworks, and tools needed to make smarter financial and business decisions in the Web3 economy.
Beyond analysis, OwnProCrypto focuses on transparency, verifiable data, and practical frameworks that investors and builders can actually use. Our goal is not hype — but clear thinking, disciplined analysis, and long-term value creation in the decentralized economy.
Our Background: Salim (Sam) is the founder and lead researcher behind OwnProCrypto, a Web3 intelligence platform focused on crypto security, digital ownership, stablecoin systems, interoperability, and institutional blockchain infrastructure.
Crypto Tools & Analysis:
Crypto Fundamental Analysis Tool | Protocol Evaluation System | DeFi Risk Analysis Tools | Crypto Portfolio Dashboard | Token Risk vs Reward Tool
Guides:
Crypto Fundamental Analysis | Blockchain Project Evaluation | Tokenomics Analysis | DeFi Protocol Analysis | Capital Efficiency
© 2026 OwnProCrypto — Built for smarter crypto decisions