
Table of Contents
ToggleAs digital assets scale into institutional portfolios, the debate around mpc-vs-multi-sig-vs-hsm-custody has become a core infrastructure question rather than a niche technical discussion. Institutions are no longer evaluating custody as simple storage—they are evaluating MPC crypto custody architectures that define how trust, risk, and control are distributed across systems.
In 2026, institutional security frameworks are primarily built on three models: MPC crypto custody, HSM crypto custody, and multi-sig wallet security. Each represents a fundamentally different approach to key management, governance design, and operational resilience.
Understanding the MPC vs multi-sig vs HSM comparison is now essential for any institution designing secure digital asset infrastructure at scale.
Which digital asset infrastructure providers deliver institutional-grade custody with proven resilience?
Today’s custody landscape is defined by three dominant security models:
Each model solves custody risk differently, from distributed computation to hardware isolation and governance-based signing.
The future of digital asset protection will not be defined by individual tools—but by how institutions architect layered custody systems that combine security, compliance, and operational efficiency. For deep Review Fireblocks for institutional security benchmarks.
Providers:
Why institutions use MPC:
Resilience model: Distributed signing removes single points of compromise.
Providers:
Why institutions use HSMs:
Resilience model: Certified tamper-resistant hardware protection.
Providers:
Why institutions use Multi-sig:
Resilience model: Distributed human approval reduces unilateral risk.
| Feature | MPC | Multi-Sig | HSM |
|---|---|---|---|
| Key Structure | Split cryptographic shares | Multiple full keys | Stored in secure hardware |
| Key Exposure | Never reconstructed | Exists in multiple locations | Never leaves device |
| Signing Model | Distributed computation | Multi-approval signing | Hardware-bound signing |
| On-Chain Visibility | Invisible | Visible | Invisible |
| Security Model | Cryptographic distribution | Governance redundancy | Hardware isolation |
| Failure Risk | No single key point | Reduced key risk | Device dependency |
| Best Use Case | Institutions, exchanges | DAOs, treasuries | Banks, regulated custody |
Institutional-grade custody isn’t defined by a single storage model. It’s measured by how well a system performs under stress—during market volatility, operational failures, and adversarial conditions. In modern institutional crypto asset security, resilience matters more than architecture alone.
Rather than asking whether MPC, multi-signature, or HSM is “best,” institutions evaluate how these models are implemented, governed, and tested in real-world scenarios.
Key evaluation criteria include:
The takeaway is simple: institutional custody is not about choosing a single technology—it’s about building a system that maintains integrity, control, and availability under all conditions.
There is no universal winner.
Each model optimizes for a different dimension:
In real institutional deployments, these are rarely used in isolation.
Modern institutional custody is no longer built on a single model. Instead, leading organizations combine MPC, HSMs, and multi-signature systems into a unified architecture—each addressing a different layer of risk within the custody stack.
Together, these components form a layered, defense-in-depth approach that is now standard in institutional crypto custody architecture. Rather than relying on one mechanism, institutions distribute trust across systems—minimizing failure points and improving operational resilience.
The result is not just stronger security, but a more adaptable custody framework that can handle evolving threats, regulatory demands, and complex transaction workflows.
Providers delivering institutional-grade custody in 2026 include:
These platforms achieve resilience by combining:
The most resilient custody architectures are hybrid systems, not single-model solutions.
CORI Institutional is a simulated enterprise custody control plane designed to model how institutional crypto systems manage high-value transactions. It combines risk scoring, policy enforcement, smart routing, approval workflows, and audit persistence into a single orchestration layer.
The system demonstrates how modern custody infrastructure evaluates transactions before execution using layered intelligence and governance controls.
Every transaction passes through a deterministic risk and policy engine before execution. Requests are evaluated against predefined rules, risk scores, and governance controls. Transactions that exceed thresholds or violate policy are either blocked or escalated through additional approval layers. Execution is permitted only after clearing all enforcement gates.
This behavior reflects how modern institutional crypto custody architecture operates in regulated environments, where governance, compliance, and execution safety are tightly controlled across every transaction flow.
It’s important to note that this system is a simulation. It is designed to demonstrate how secure crypto storage for institutions is achieved through risk-aware orchestration—combining policy enforcement, real-time evaluation, and auditability at every stage of the transaction lifecycle.
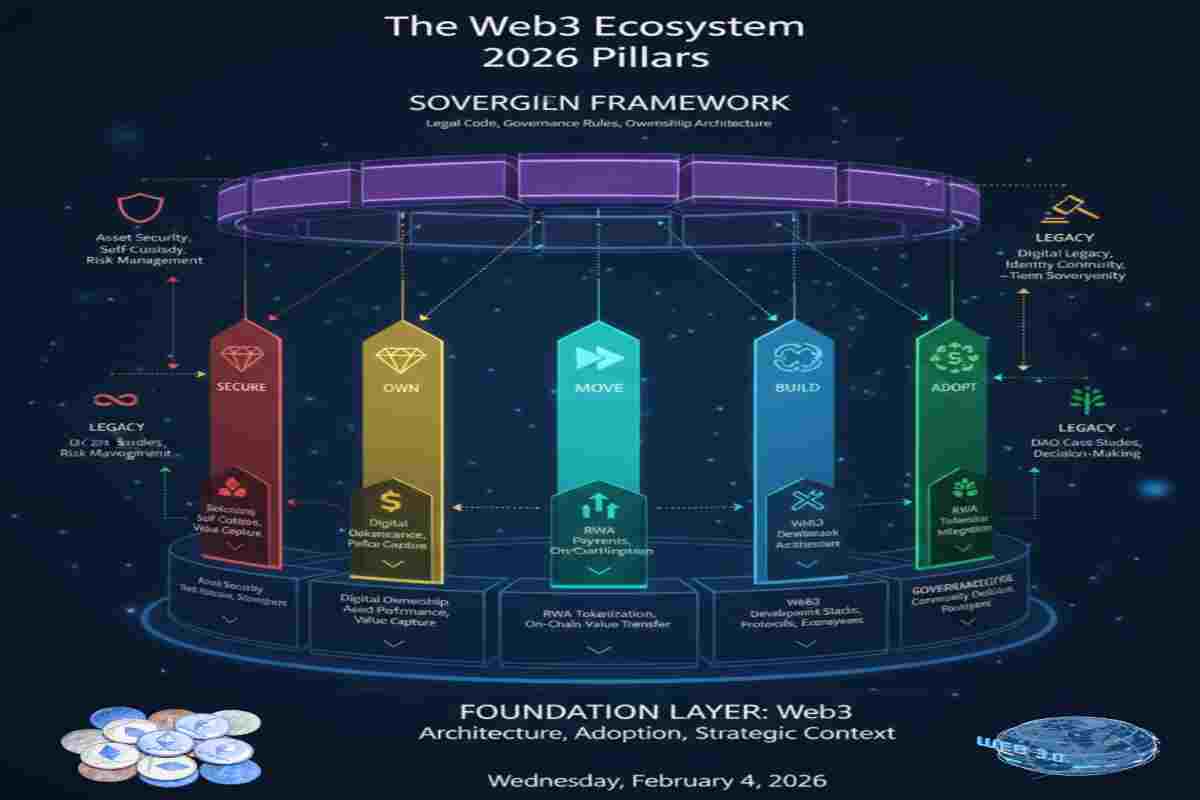
As part of the SECURE pillar Institutional Trust & Governance (The Control Layer), this guide focuses on digital asset protection, custody architecture, and institutional-grade risk management in Web3.
Explore related articles:
– Web3 Governance Framework 2026: Crypto Market Compliance
– Crypto Scam Checker 2026: How to Detect Fake Websites
– Crypto Asset Security 2026: Building Your Digital Fortress
– Legacy & Sovereignty: Securing Your Digital Life Beyond You
– Asset Security 2026: Digital Fortress with Account Abstraction
– 7 Crypto Security Standards: From Retail to Family Office
– Crypto Self Custody Security Toolkit 2026
– Digital Asset Risk Management Framework: DSARAE Model
– Smart Legal Contract Modules: Automated Compliance in 2026
– Smart Contract Wills 2026: Securing Your Digital Legacy
Web3 Decision Lab Structure (4-Layer Mapping)
Here you can Access System Tools Directly by Taping below link
– Digital Crypto Asset Risk Analysis Tool (DSARAE)
– Crypto Security Checklist (Wallet & Self-Custody)
– MPC vs Multi-Sig Wallets (Custody Architecture)
– Crypto Trading System: CDIS-2026
– Asset Risk Assessment System: Audit & Protect Portfolio
– Crypto Bridge Risk Tool (Cross-Chain Systems)
Each article functions independently while forming a complete sovereign Web3 lifecycle model.
What is institutional crypto custody? Institutional crypto custody refers to secure infrastructure used by organizations to store and manage digital assets using advanced security models like MPC crypto custody, HSM, and multi-signature wallets.
Is MPC better than multi-sig wallets? In an MPC vs multi-sig vs HSM comparison, MPC is often seen as more scalable because it eliminates full key exposure by splitting shares, while multi-sig provides transparent, on-chain approvals that are easily auditable.
What is MPC in crypto custody? MPC crypto custody (Multi-Party Computation) splits private keys into multiple “shards” or shares, allowing a transaction to be signed mathematically without the full private key ever being reconstructed in a single location.
What is an HSM in crypto custody? HSM crypto custody involves using a Hardware Security Module, which is a specialized, tamper-resistant physical device designed to securely generate, store, and protect cryptographic keys from external digital attacks.
What is the difference between MPC, HSM, and multi-sig? When evaluating mpc-vs-multi-sig-vs-hsm-custody, the distinction lies in the architecture: MPC uses distributed cryptography, HSM relies on physical hardware protection, and multi-sig requires multiple independent full signatures to authorize a transaction.
Which are the best crypto custody providers in 2026? Top crypto custody providers include Fireblocks, Copper, BitGo, and enterprise HSM providers like Thales and IBM, known for institutional-grade security and reliability.
What is the safest crypto custody solution for institutions? The safest approach is a hybrid custody architecture combining MPC, HSM, and multi-sig, reducing single points of failure and improving overall security.
How do institutions store crypto securely? Institutions use distributed key management (MPC), hardware security modules (HSMs), and multi-layer approval systems to secure digital assets.
Are multi-sig wallets safe for institutional use? Yes, multi-sig wallet security is robust and widely used for treasury management and DAO governance, though it requires managing multiple independent private keys across different stakeholders.
What is institutional-grade crypto security? It includes advanced key management, policy controls, compliance frameworks, and resilience against operational and security failures.
Why is crypto custody important for institutions? Custody protects large digital asset holdings from theft, loss, and operational risks while ensuring compliance and governance.
What are regulated crypto custody solutions? These are custody providers that meet regulatory standards, including compliance certifications like SOC 2 and ISO 27001.
How do crypto custody providers manage risk? They use risk engines, transaction policies, approval workflows, and monitoring systems to prevent unauthorized or high-risk transactions.
What is crypto custody infrastructure? It refers to the underlying systems, tools, and technologies used to secure, manage, and process digital asset transactions.
Can institutions use multiple custody models together? Yes, most institutions use hybrid custody systems combining MPC, HSM, and multi-sig for maximum security and flexibility.
Institutional crypto custody in 2026 is no longer about choosing a single security model, but about designing resilient hybrid systems that combine the strengths of all three approaches within the mpc-vs-multi-sig-vs-hsm-custody framework.
Modern institutions increasingly rely on MPC crypto custody to eliminate single points of key exposure, HSM crypto custody to enforce hardware-level security boundaries, and multi-sig wallet security to introduce governance-based authorization layers. Together, these systems create a multi-layered defense model that significantly improves operational resilience.
A clear MPC vs multi-sig vs HSM comparison shows that no single architecture is universally superior. Instead, the strongest institutions integrate all three models to balance scalability, compliance, and control.
Core architecture principles:
Together, they form the foundation of institutional-grade digital asset custody—where security is not a feature, but a layered system of design decisions.
Welcome to OwnProCrypto (Own & Pro Crypto) — a next-generation Bitcoin and blockchain education platform where the science of finance meets the power of AI-driven automation.
Our mission is simple: to equip you with the knowledge, frameworks, and tools needed to make smarter financial and business decisions in the Web3 economy.
Beyond analysis, OwnProCrypto focuses on transparency, verifiable data, and practical frameworks that investors and builders can actually use. Our goal is not hype — but clear thinking, disciplined analysis, and long-term value creation in the decentralized economy.
Our Background
Crypto Tools & Analysis:
Crypto Fundamental Analysis Tools | Protocol Evaluation System | DeFi Risk Analysis Tools | Crypto Portfolio Dashboard | Token Risk vs Reward Tool
Guides:
Crypto Fundamental Analysis | Blockchain Project Evaluation | Tokenomics Analysis | DeFi Protocol Analysis
© 2026 OwnProCrypto — Built for smarter crypto decisions