
Table of Contents
ToggleSecuring crypto assets is one of the biggest challenges in Web3. From private key management to wallet security and inheritance planning, most users understand the risks—but lack a clear system to manage them.
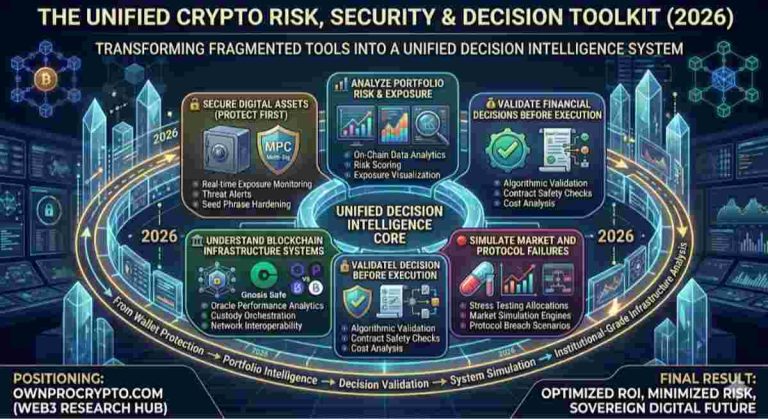
This Crypto Security Checklist tool helps you audit your current setup, identify vulnerabilities, and build a secure self-custody framework. Instead of relying on guesswork, you can evaluate your security posture and design a structure that protects your assets long-term.
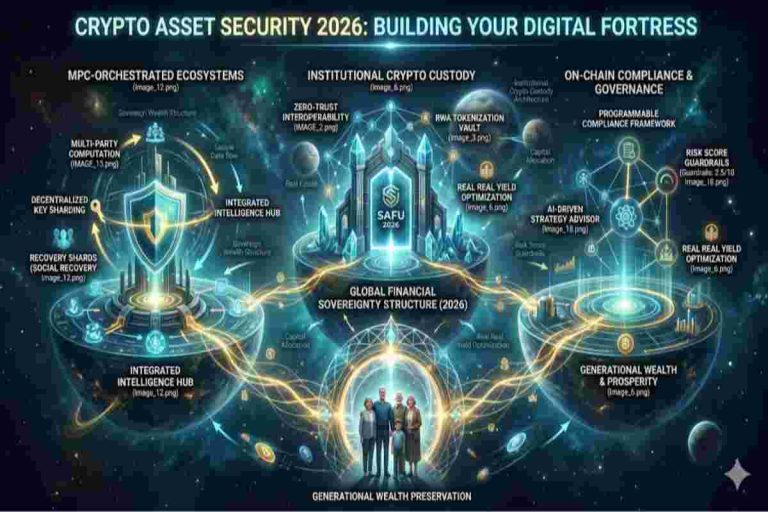
These protocols provide the institutional-grade safety required for the assets managed in our Asset Security 2026 framework. Check the NIST Cybersecurity Framework for global security benchmarks.
This dashboard combines a security audit with a customizable setup builder to help you strengthen your crypto protection:
This system belongs to the Asset Security layer of the Web3 Decision Lab.
You may also explore:
– Digital Crypto Asset Risk Analysis Tool (DSARAE)
True ownership in Web3 is not defined by what you hold—it’s defined by what you control.
By auditing your current setup and building a structured security stack, you move from passive exposure to intentional protection. This tool helps transform uncertainty into clarity, giving you a system to secure, manage, and preserve your digital assets with confidence.
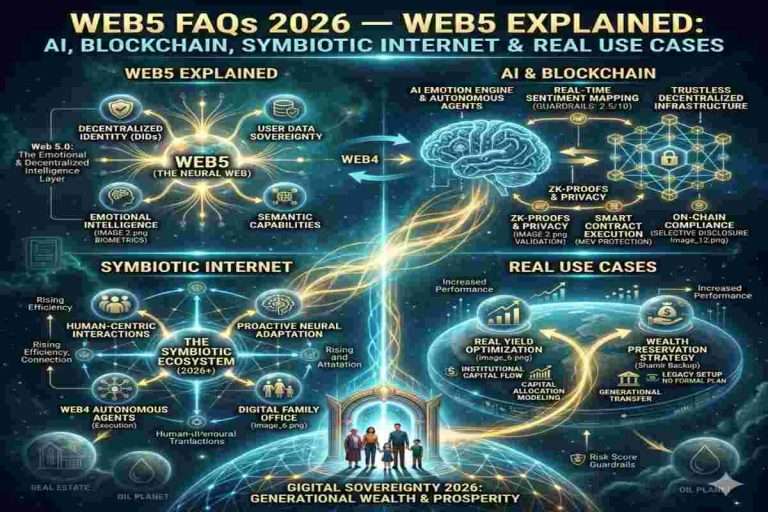
To truly master the Institutional Crypto Custody Architecture of 2026, one must look beyond market volatility and toward the structural evolution of global finance. As the Web3 Ecosystem matures, the integration of RWA Tokenization and On-Chain Compliance is becoming a standard requirement for Tier-1 asset managers. Understanding how international bodies are framing these digital sovereign assets is critical for any firm prioritizing Capital Efficiency and long-term risk management.
Global Strategy Reference:
For official guidance on digital asset risks, compliance, and investor protection, refer to global regulatory frameworks and public advisories.
this doesn’t match the headlines → U.S. SEC Cybersecurity & Digital Asset Guidance
Securing a crypto wallet starts with controlling your private keys. Use hardware wallets where possible, enable strong authentication methods, avoid storing sensitive data digitally, and regularly review permissions connected to your wallet.
Self-custody means you fully control your private keys without relying on exchanges or third parties. This gives you complete ownership of your assets but also makes you responsible for security and recovery.
A crypto security checklist is a structured way to evaluate how safely your assets are stored. It typically includes key management, authentication, custody methods, and backup or recovery planning.
Keeping crypto on exchanges is convenient but introduces counterparty risk. If the platform is compromised or restricts access, your assets may be at risk. Many users move long-term holdings to self-custody solutions.
This phrase means that if you don’t control the private keys to your crypto, you don’t truly own it. Ownership depends on access to keys, not just account balances on a platform.
The safest approach typically involves hardware wallets, offline backups of recovery phrases, and multi-layered authentication. Advanced users may also use multi-signature setups or social recovery mechanisms.
Yes. If you lose access to your private keys or recovery phrase without a backup, your crypto may be permanently inaccessible. This is why secure backup and recovery planning are critical.
Crypto inheritance planning ensures that your digital assets can be accessed by trusted individuals if something happens to you. This may involve secure documentation, legal structures, or recovery protocols.
A crypto security audit evaluates how your assets are stored and protected. It identifies vulnerabilities in key management, access controls, and overall security setup.
Welcome to OwnProCrypto (Own & Pro Crypto) — a next-generation Bitcoin and blockchain education platform where the science of finance meets the power of AI-driven automation.
Our mission is simple: to equip you with the knowledge, frameworks, and tools needed to make smarter financial and business decisions in the Web3 economy.
Beyond analysis, OwnProCrypto focuses on transparency, verifiable data, and practical frameworks that investors and builders can actually use. Our goal is not hype — but clear thinking, disciplined analysis, and long-term value creation in the decentralized economy.
Our Background: Salim (Sam) is the founder and lead researcher behind OwnProCrypto, a Web3 intelligence platform focused on crypto security, digital ownership, stablecoin systems, interoperability, and institutional blockchain infrastructure.
Crypto Tools & Analysis:
Crypto Fundamental Analysis Tool | Protocol Evaluation System | DeFi Risk Analysis Tools | Crypto Portfolio Dashboard | Token Risk vs Reward Tool
Guides:
Crypto Fundamental Analysis | Blockchain Project Evaluation | Tokenomics Analysis | DeFi Protocol Analysis | Capital Efficiency
© 2026 OwnProCrypto — Built for smarter crypto decisions