Table of Contents
ToggleExplore:
← Previous Post Title
Next Post Title →
[ Home ]
[ Deep Dive: ]
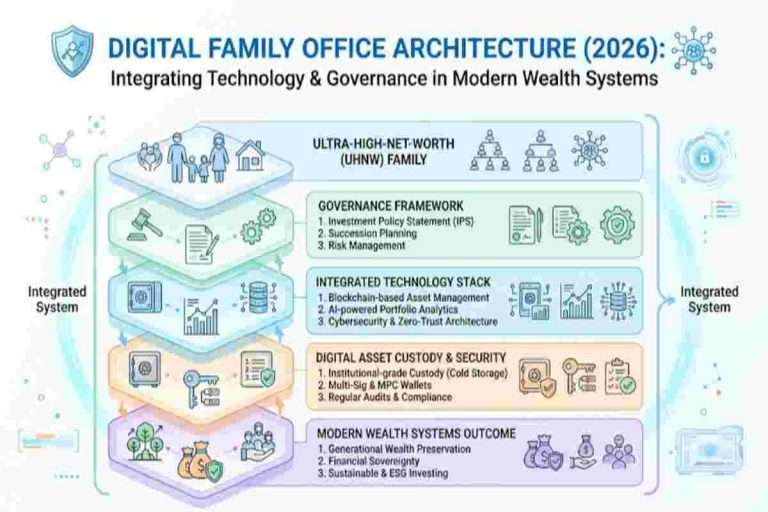
Institutional crypto custody is shifting from static wallet security toward programmable operational infrastructure. Hedge funds, ETFs, exchanges, RIAs, and enterprise treasury teams increasingly require governance automation, transaction orchestration, policy-based approvals, and scalable operational security.
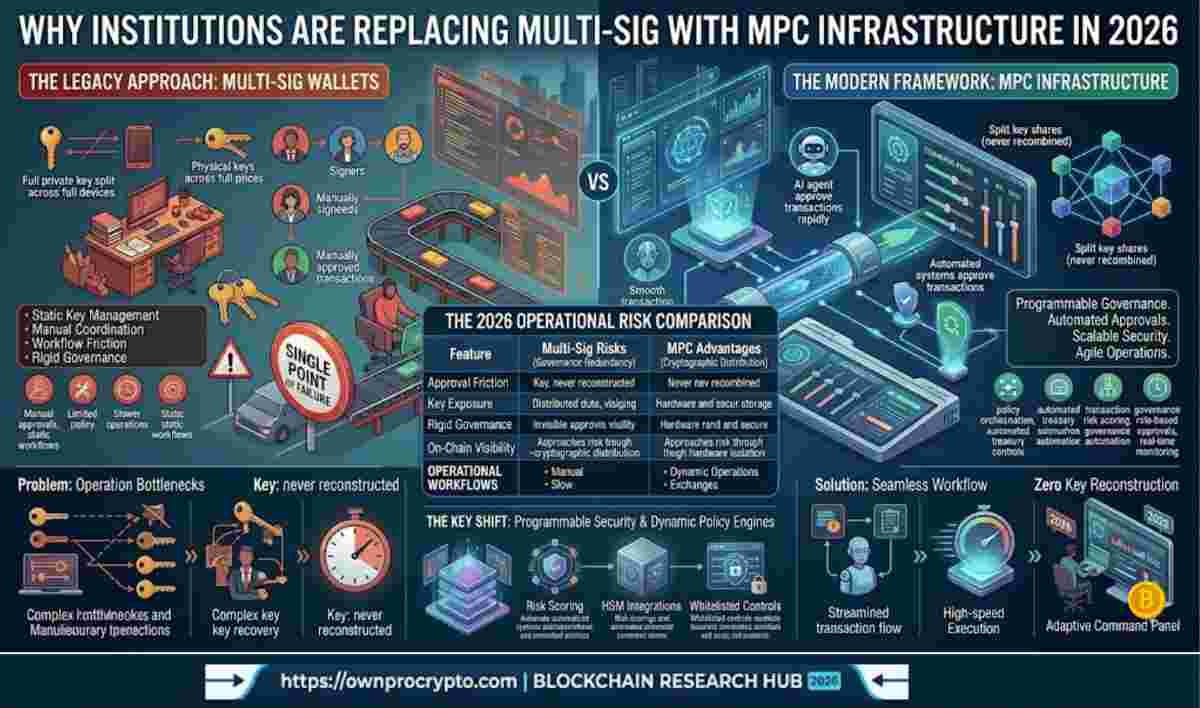
Multi-signature wallets solved early crypto custody risks, but institutional treasury operations in 2026 involve far more complexity. Modern firms now manage staking, OTC settlement, ETF liquidity, cross-border treasury transfers, and automated transaction workflows that traditional multi-sig systems were never designed to handle.
(Problem)
Traditional multi-sig architecture creates operational bottlenecks for institutional treasury workflows.
(Solution)
MPC infrastructure enables programmable governance, automated approvals, and scalable transaction security for enterprise crypto operations.
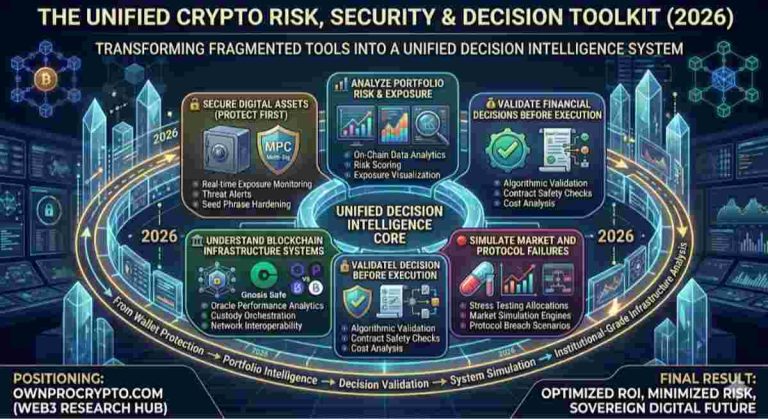
Institutional crypto treasury security evolved rapidly after ETFs, regulated staking products, and enterprise digital asset adoption accelerated. Early multi-sig wallets focused primarily on reducing single-key risk, but institutional operations now require much more than static signing coordination.
Modern institutions increasingly prioritize:
This shift transformed custody from wallet protection into operational infrastructure.
(Problem)
Static signing systems cannot efficiently support modern institutional transaction operations.
(Solution)
MPC infrastructure introduces programmable governance layers that automate treasury security workflows.

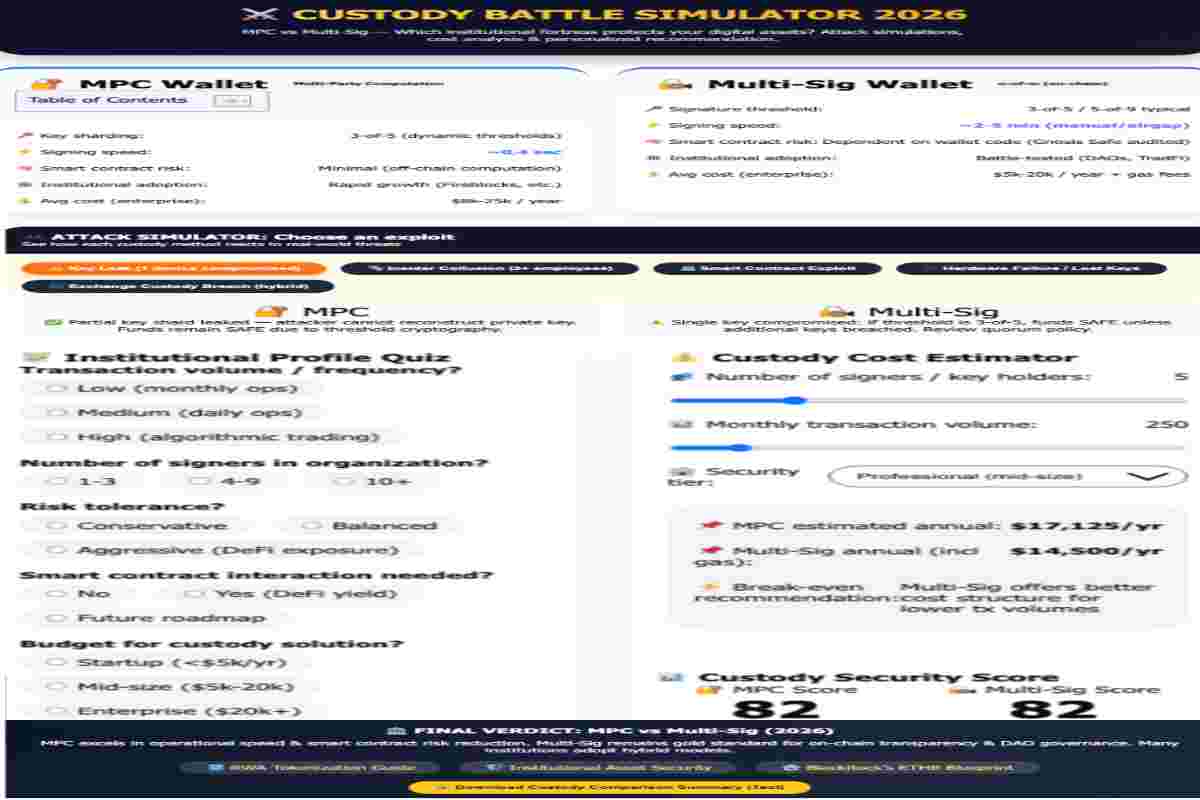
The biggest driver behind MPC adoption is operational scalability. Multi-sig wallets rely on multiple complete keys distributed across devices, employees, or locations. While safer than single-key custody, they introduce approval friction, recovery complexity, and governance inefficiencies.
MPC infrastructure works differently. Instead of storing full keys, MPC distributes encrypted cryptographic shares across participants and systems. Transactions are signed collaboratively without reconstructing the private key itself.
| Criteria | Multi-Sig Wallets | MPC Infrastructure |
|---|---|---|
| Key Exposure | Static full keys | Distributed cryptographic shares |
| Transaction Speed | Manual approvals | Automated policy execution |
| Governance | Human coordination | Programmable policy engine |
| Treasury Automation | Limited | Enterprise-grade |
| Recovery Architecture | Complex | Flexible |
| Operational Scaling | Slower | Highly scalable |
| HSM Integration | Partial | Native support |
| Policy Enforcement | External | Integrated |
Institutions increasingly view operational risk as more dangerous than direct key compromise.
(Problem)
Institutional teams struggle with fragmented governance and slow treasury approvals using traditional multi-sig systems.
(Solution)
MPC infrastructure reduces operational friction through programmable transaction orchestration and automated governance controls.
Institutional wallet architecture in 2026 is no longer centered only around key custody. Modern infrastructure stacks connect treasury systems, compliance engines, custodians, HSM layers, and operational governance into a unified framework.
To remain resilient, most institutional deployments of MPC infrastructure in 2026 now include:
This MPC infrastructure in 2026 allows treasury teams to scale operational security while effectively reducing human bottlenecks.
(Problem)
Legacy wallet infrastructure cannot efficiently support institutional-scale treasury operations.
(Solution)
Modern custody stacks combine MPC, policy engines, HSM security, and governance automation into a scalable operational framework.
The rise of MPC policy engine crypto custody platforms is changing institutional security models. Instead of relying solely on cryptographic authorization, institutions now enforce governance rules before transactions are approved.
Modern policy engines can enforce:
This converts custody into a programmable governance layer rather than passive asset storage.
| Feature | Traditional Multi-Sig | MPC Policy Engine |
|---|---|---|
| Static Signatures | Yes | No |
| Automated Controls | Limited | Advanced |
| Transaction Rules | Manual | Dynamic |
| Treasury Workflow Support | Basic | Enterprise-grade |
| Risk Monitoring | External tools required | Integrated |
| Governance Flexibility | Moderate | High |
(Problem)
Traditional multi-sig protects keys but does not fully manage operational treasury risk.
(Solution)
MPC policy engines automate governance, compliance enforcement, and institutional transaction controls.
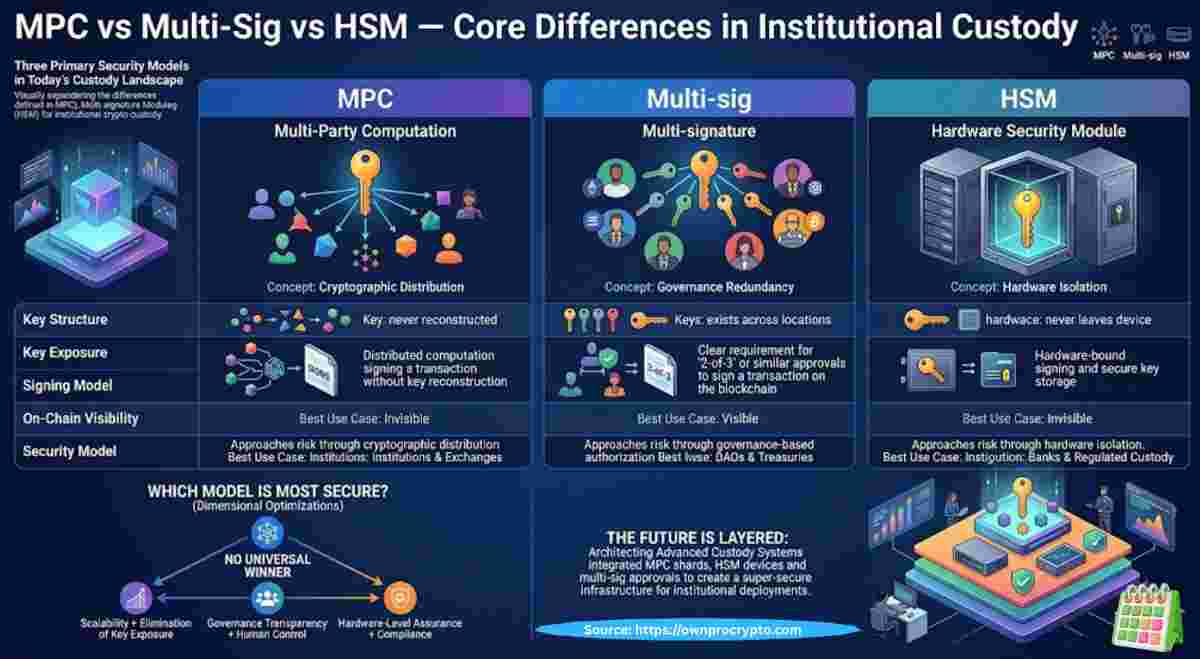
Institutions increasingly treat custody as infrastructure rather than wallet storage. Modern crypto custody infrastructure stacks integrate multiple operational systems into a single governance environment.
These stacks commonly connect:
Large treasury operations require flexible infrastructure capable of adapting to evolving market conditions, operational demands, and future cryptographic upgrades.
Multi-signature wallets solved early crypto custody risks, but institutional treasury operations in 2026 involve far more complexity. Modern firms now manage staking, OTC settlement, ETF liquidity, cross-border treasury transfers, and automated transaction workflows that traditional multi-sig systems were never designed to handle.
(Problem)
Static wallet systems limit operational flexibility for enterprise treasury teams.
(Solution)
MPC infrastructure provides modular operational architecture capable of supporting dynamic institutional workflows.
Institutional adoption accelerated as enterprise custody providers expanded MPC infrastructure capabilities. Platforms increasingly focus on governance automation, policy enforcement, treasury orchestration, and operational scalability.
Major institutional providers now support:
This transition helped move MPC from niche custody technology into enterprise treasury infrastructure.
(Problem)
Institutions require operational infrastructure beyond simple wallet custody.
(Solution)
Enterprise MPC platforms now provide integrated governance, treasury automation, and scalable custody architecture.

Not entirely. Multi-sig still remains effective for several use cases:
However, institutions managing complex treasury operations increasingly prefer MPC because operational scalability becomes more important over time.
| Use Case | Multi-Sig | MPC Infrastructure |
|---|---|---|
| DAO Governance | Strong fit | Moderate |
| Institutional Treasury | Limited | Strong |
| ETF Operations | Weak | Strong |
| Automated Workflows | Weak | Strong |
| Cold Storage | Strong | Strong |
| Enterprise Governance | Moderate | Strong |
(Problem)
Many organizations assume one custody model works for every operational environment.
(Solution)
Different custody architectures serve different governance and treasury requirements.
Institutional crypto treasury security is evolving toward programmable operational infrastructure. The market increasingly prioritizes:
This transition explains why institutions are replacing multi-sig with MPC infrastructure across modern enterprise custody environments.
(Problem)
Institutional crypto operations are becoming too complex for static wallet security models.
(Solution)
MPC infrastructure provides scalable operational architecture designed for enterprise-grade treasury environments.
Institutional crypto custody is rapidly evolving beyond static wallet protection into a sophisticated operational layer. Enterprise treasury teams now require governance automation, scalable approval systems, operational resilience, and programmable transaction infrastructure to manage the complexities of modern digital finance.
As institutional crypto operations continue growing in complexity, MPC infrastructure in 2026 is becoming the preferred architecture for modern custody environments. By prioritizing cryptographic distribution over static key management, this model provides the agility and security necessary for firms to scale their digital asset strategies with confidence.
Welcome to OwnProCrypto (Own & Pro Crypto) — a next-generation Bitcoin and blockchain education platform where the science of finance meets the power of AI-driven automation.
Our mission is simple: to equip you with the knowledge, frameworks, and tools needed to make smarter financial and business decisions in the Web3 economy.
Beyond analysis, OwnProCrypto focuses on transparency, verifiable data, and practical frameworks that investors and builders can actually use. Our goal is not hype — but clear thinking, disciplined analysis, and long-term value creation in the decentralized economy.
Our Background
Crypto Tools & Analysis:
Crypto Fundamental Analysis Tools | Protocol Evaluation System | DeFi Risk Analysis Tools | Crypto Portfolio Dashboard | Token Risk vs Reward Tool
Guides:
Crypto Fundamental Analysis | Blockchain Project Evaluation | Tokenomics Analysis | DeFi Protocol Analysis
© 2026 OwnProCrypto — Built for smarter crypto decisions