
In 2026, the biggest risk in crypto isn’t volatility — it’s infrastructure failure.
Table of Contents
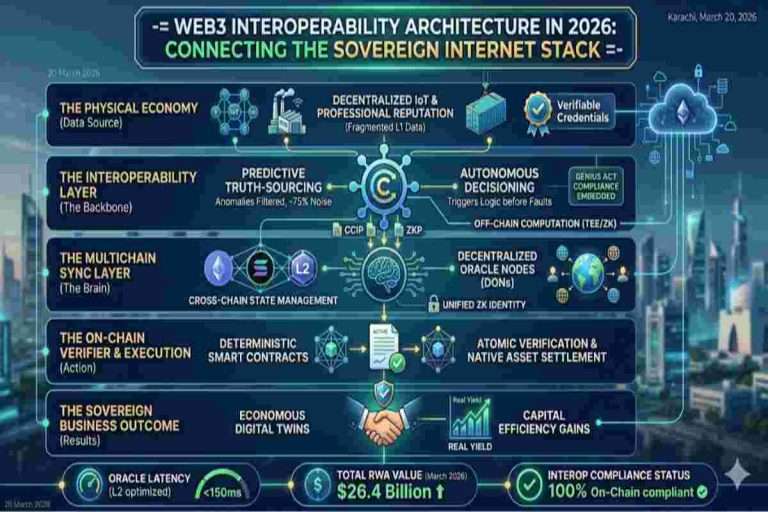
ToggleThe baseline reality of decentralized infrastructure is that legacy cross-chain architectures have turned blockchain bridges into prime structural targets for sophisticated exploits. As multi-chain capital deployment scales, relying on perimeter-based security and centralized multisig assumptions is no longer a viable security posture. To defend institutional assets from catastrophic liquidity drains, the industry must transition toward absolute Zero-Trust Interoperability.
This comprehensive strategic blueprint unpacks how engineering-grade cryptographic validation, real-time message isolation, and immutable security frameworks eliminate structural counterparty risk. By implementing verified zero-knowledge execution loops, developers and asset managers can permanently immunize their ecosystems against cross-chain vulnerabilities while preserving maximum capital efficiency.
Billions of dollars have been lost to crypto bridge hacks, exposing a fundamental flaw in how blockchains communicate. Bridges were meant to solve cross-chain interoperability, but their reliance on fragile cross-chain messaging protocols made them the weakest link.
The reality is simple:
Bridges don’t fail because of bugs — they fail because of design.
A new model is emerging:
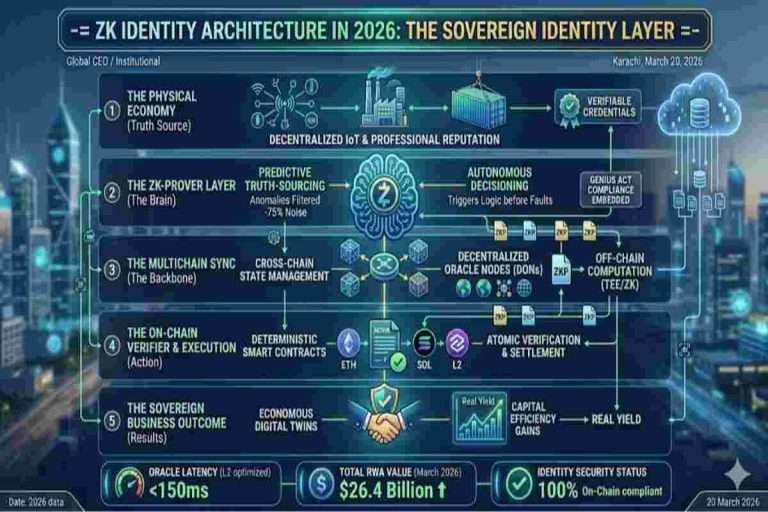
Powered by zero-knowledge proofs (ZKPs) and shared security crypto systems, this approach eliminates the need to trust intermediaries entirely.
This is not an upgrade.
This is a replacement of the bridge model itself.
Securing cross-chain paths is the final frontier of the Web3 Interoperability 2026 framework, ensuring your assets move without risk.
The blockchain ecosystem was never designed to be unified.
Each chain:
This creates:
To solve this, we introduced: Crypto bridges
Most cross-chain bridges rely on:
This creates a dangerous structure:
A single honeypot holding billions of dollars
Even “decentralized” bridges rely on trusted validators.
Bridges create synthetic assets that depend on:
More logic = more attack surface
Before moving assets across chains, it’s crucial to understand how much trust you’re placing in bridge infrastructure. Most users don’t realize the hidden risks involved.
“How much risk am I actually taking?” is the question every blockchain user should ask before bridging funds.
Not all crypto bridges are created equal. Some rely on highly trusted validator sets, while others lock massive liquidity pools—prime targets for hackers. Understanding these differences is key to protecting your assets.
To make this simple, use the Bridge Risk Analyzer (2026) below. It provides a quick, practical assessment of your exposure based on how modern cross-chain interoperability systems are structured.
The analyzer evaluates bridge risk across four core factors:
Each factor is weighted to produce a clear output:
Low Risk / Medium Risk / High Risk
| Feature | Crypto Bridges | Zero-Trust Interoperability |
|---|---|---|
| Trust Model | External validators | Cryptographic verification |
| Security Risk | High (honeypots) | Minimal |
| Asset Handling | Wrapped tokens | Native state verification |
| Attack Surface | Large | Reduced |
| Reliability | Fragile | Deterministic |
Instead of moving assets…
We verify state across chains
This is the foundation of:
Zero-trust interoperability means:
No chain needs to trust another chain, validator, or bridge.
Everything is verified using:
A zero-knowledge proof (ZKP) allows:
Instead of:
You:
No custody
No middleman
No exploit point

(For a deeper breakdown, see our detailed analysis on Interoperability Autonomous Crypto Systems)
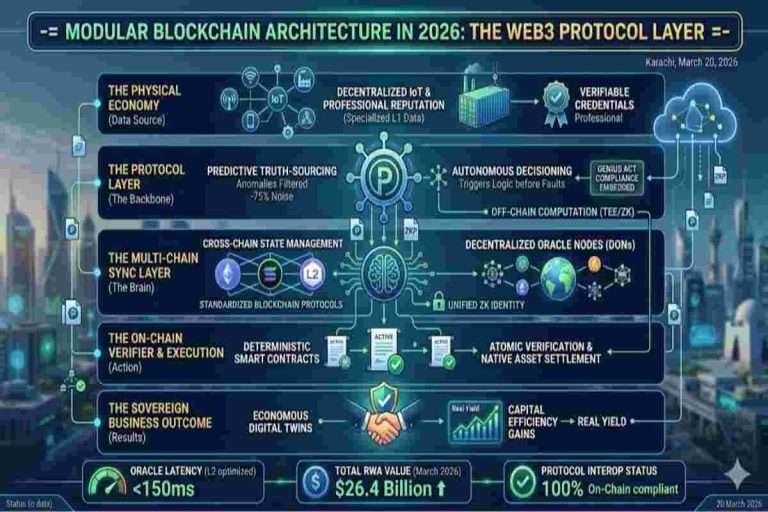
(For a deeper breakdown, see our detailed analysis on Modular Blockchain Architecture in 2026)
The transition is already happening.
Where ZKPs Are Already Being Used:
ZKPs are becoming core infrastructure, not experimental tech.
| Use Case | Old Model | New Model |
|---|---|---|
| Asset Transfer | Bridge assets | Verify state |
| Identity | Share data | Prove attributes (ZK) |
| Compliance | Reveal documents | Proof-based validation |
| Liquidity | Fragmented | Unified |
While the technical hurdles of moving away from trusted bridges are real, the Web3 ecosystem has developed highly optimized solutions to overcome these structural limitations.
The heavy computational overhead required to generate zero-knowledge proofs (ZKPs) has historically caused high transaction latency and cost barriers. To solve this, protocols are leveraging specialized hardware acceleration—specifically Application-Specific Integrated Circuits (ASICs) and Field-Programmable Gate Arrays (FPGAs)—optimized purely for cryptographic operations. Additionally, decentralized “Prover Markets” allow independent infrastructure providers to compete to generate proofs at the lowest cost, driving down execution fees and accelerating finality times for cross-chain transactions.
Building cryptographic cross-chain pipelines traditionally required rare, specialized knowledge in advanced mathematics and low-level rust environments. Modern interoperability layers are resolving this bottleneck by shipping production-ready Software Development Kits (SDKs). These developer tools completely abstract away the complex mathematical proof generation. Engineers can now secure their applications with plug-and-play zero-trust logic using familiar smart contract patterns, removing the need to build verification engines from scratch.
The fragmentation of disparate blockchain networks has made it difficult to establish a single source of truth for cross-chain messages. The industry is actively solving this by building unified semantic standards and open-source messaging interfaces (such as ERC-7683 for cross-chain intents). By establishing a shared, open layer for data packets, diverse ecosystems can securely pass and read zero-trust cryptographic proofs without relying on custom, ad-hoc bridge wrappers.
To push early-stage zero-trust tooling into enterprise-grade readiness, development teams are employing rigorous formal verification tools that mathematically prove the correctness of smart contract code before deployment. Combined with advanced off-chain simulation environments and massive bug bounty programs, the infrastructure layer is rapidly transitioning from experimental sandboxes to robust, battle-tested execution layers capable of securing institutional treasury volume.
By 2026–2027:
As the decentralized economy scales, the transition from legacy perimeter-based security architectures to absolute Zero-Trust Interoperability is no longer a luxury—it is an existential imperative for protecting institutional capital. The continuous wave of cross-chain exploits has definitively proven that human-dependent validation systems and multi-sig bridges are fundamentally incompatible with high-value digital asset management.
By systematically applying zero-trust primitives, enforcing cryptographic validation at every single message layer, and leveraging optimized zero-knowledge verification frameworks, the industry is effectively eliminating structural counterparty risk. Adopting Zero-Trust Interoperability: Preventing Crypto Bridge Hacks (2026) is the defining step toward establishing a secure, resilient, and truly sovereign internet of value where capital moves flawlessly without compromising its core defensive posture.
Zero-trust interoperability marks the end of an era.
Instead of trusting:
We now trust:
Powered by:
This shift doesn’t just improve security…
It redefines how blockchains connect.
Explore additional insights on Artificial Intelligence Crypto, MEV extraction, and AI-driven markets: https://ethereum.org/en/developers/docs/mev/
Q1: Are zero-knowledge proofs legal?
Yes. They enhance regulatory compliance rather than bypass it.
Q2: Do ZKPs enable anonymity?
They enable selective disclosure, not blanket anonymity. You control what information is shared.
Q3: Are ZKPs only for blockchain?
No. ZKPs apply to identity management, data privacy, and compliance systems beyond blockchain.
Q4: Do zero-knowledge proofs replace regulation?
No. They strengthen enforcement and transparency, complementing existing regulations.
Q5: Will ZKPs become mainstream?
Yes, especially where privacy and compliance intersect, making secure digital interactions easier.
Q6: If I use ZK-proofs, can the government still track me?
Yes, under controlled conditions. In 2026, ZK technology follows “Controlled Disclosure”: you can grant a “Viewing Key” to regulators or tax authorities, while the public sees nothing. It preserves privacy for honest users but is not a loophole for illegal activity.
Case Study: Early privacy coins like Monero were delisted because they offered no compliance tools. Modern ZK solutions like Polygon ID succeed by enabling selective disclosure.
Q7: Are ZK-proofs too technical for beginners?
Not anymore. In 2026, ZK-proofs operate automatically behind the scenes. When you connect your wallet, the math runs instantly, similar to using a fingerprint to unlock your phone.
Case Study: In 2023, generating a ZK-proof required a high-end PC and 30 seconds. Today, recursive ZK-proofs compute in milliseconds on standard smartphones.
Q8: What is zero-trust interoperability?
It is a system where blockchains verify each other directly using cryptographic proofs, without intermediaries or centralized trust.
Q9: Is cross-chain interoperability safe in 2026?
Yes. New models leveraging trustless verification and zero-knowledge proofs significantly reduce risk compared to earlier bridges.
Q10: Why are crypto bridge hacks common?
Bridges hold large pooled funds and rely on trust-based mechanisms, making them prime targets for attacks.
Q11: What replaces crypto bridges?
ZK proofs, shared security frameworks, and native cross-chain interoperability protocols provide safer alternatives.
Q12: Can ZKPs be used for compliance reporting?
Yes. They allow organizations to prove regulatory compliance without exposing sensitive data publicly.
Q13: Do ZKPs slow down transactions?
No. Modern recursive ZK-proofs compute quickly, even on smartphones, enabling near-instant verification.
Q14: Are ZKPs secure against future threats?
Yes. Recursive and post-quantum ZK systems are designed to resist emerging computational attacks.
Q15: How widely adopted are ZKPs today?
By 2026, ZKPs are integrated into multiple blockchain networks, enterprise identity systems, and privacy-preserving applications.
Welcome to OwnProCrypto (Own & Pro Crypto) — a next-generation Bitcoin and blockchain education platform where the science of finance meets the power of AI-driven automation.
Our mission is simple: to equip you with the knowledge, frameworks, and tools needed to make smarter financial and business decisions in the Web3 economy.
Beyond analysis, OwnProCrypto focuses on transparency, verifiable data, and practical frameworks that investors and builders can actually use. Our goal is not hype — but clear thinking, disciplined analysis, and long-term value creation in the decentralized economy.
Our Background: Salim (Sam) is the founder and lead researcher behind OwnProCrypto, a Web3 intelligence platform focused on crypto security, digital ownership, stablecoin systems, interoperability, and institutional blockchain infrastructure.
Crypto Tools & Analysis:
Crypto Fundamental Analysis Tool | Protocol Evaluation System | DeFi Risk Analysis Tools | Crypto Portfolio Dashboard | Token Risk vs Reward Tool
Guides:
Crypto Fundamental Analysis | Blockchain Project Evaluation | Tokenomics Analysis | DeFi Protocol Analysis | Capital Efficiency
© 2026 OwnProCrypto — Built for smarter crypto decisions