
Table of Contents
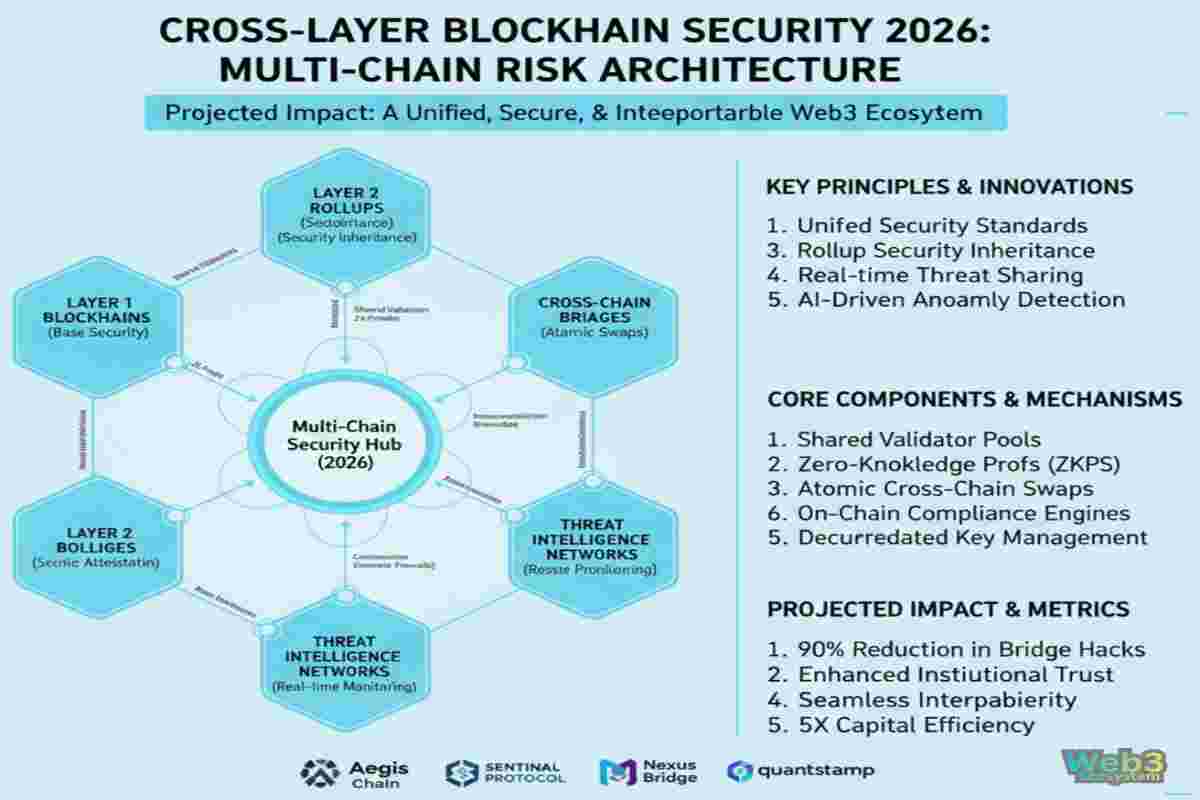
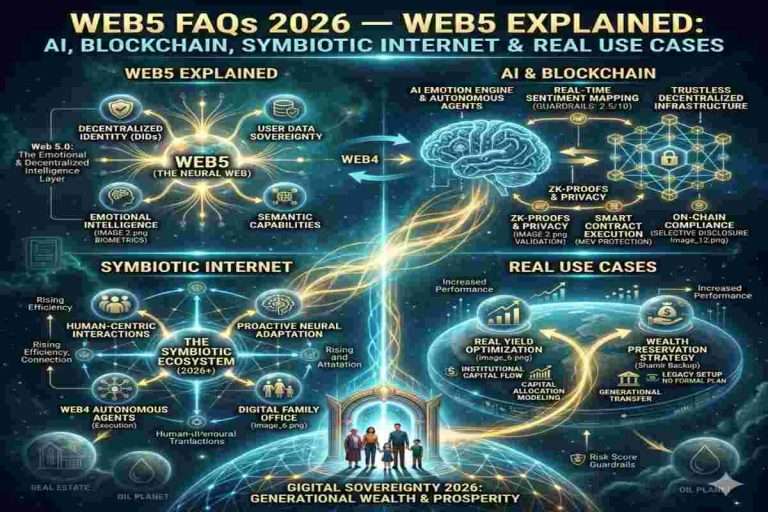
ToggleIn 2026, the Web3 ecosystem is no longer confined to a single blockchain. It has evolved into a complex, multi-chain environment where assets, data, and logic move across Layer 1 networks, Layer 2 rollups, bridges, and decentralized applications. As this interoperability expands, cross-chain blockchain security has become a critical priority for protecting both institutional and retail capital.
Value no longer remains siloed. Smart contracts, governance systems, and liquidity now operate across interconnected chains. This composability unlocks innovation—but also introduces new attack surfaces, especially in blockchain bridge security and rollup security models, where vulnerabilities can scale rapidly across networks.
Security in this landscape is no longer about isolated defenses. A single weakness in one layer can trigger cascading failures across the entire ecosystem.
Security is no longer just about preventing exploits—it’s about mitigating systemic risk across interconnected chains.
To address these challenges, modern Web3 infrastructure relies on integrated approaches, including cross-chain security frameworks, secure bridge architectures, and advanced rollup validation mechanisms. These systems aim to deliver:
As blockchain adoption accelerates, the future of security lies in unified, multi-layered architectures that can safeguard assets across an increasingly interconnected Web3 economy.
Cross‑Chain Blockchain Security refers to the collective mechanisms that secure not just individual blockchains, but the interactions and dependencies between them. It covers:
Security is now a systemic property, not a feature added to a single contract or chain.
Cross-Chain Security is no longer optional — it is strategic. As blockchain ecosystems scale and composability increases, attack surfaces expand exponentially. Today’s protocols depend on:
Every layer interacts with another. A vulnerability in one layer can cascade across networks, turning a single exploit into systemic failure.
Unlike early blockchain years — when security was about defending a single contract or wallet — 2026 demands end‑to‑end security that spans layers, networks, and protocols.
This Article belongs to the Asset Intelligence layer.
Modern blockchain threats have evolved:
| Attack Vector | Impact | Example |
|---|---|---|
| Smart Contract Exploit | Loss of funds or logic control | DAO hack (2016) |
| Bridge Exploit | Cross‑chain liquidity theft | Wormhole (2022) |
| Oracle Manipulation | Incorrect execution triggers | Price oracle attacks |
| Sequencer / Rollup Failures | Censorship, replay, rollback | L2 congestion exploits |
| Cross‑Chain Message Replay | Interoperability inconsistency | Message replay exploits |
Traditional security focuses on securing contracts. Cross‑Layer security focuses on securing trust dependencies across ecosystems.
In 2026, securing decentralized systems requires a layered perspective. Each layer introduces unique security challenges:
| Layer | Function | Security Focus |
|---|---|---|
| L0 / Network Layer | Nodes, P2P, consensus | Node integrity, Sybil attack prevention, validator slashing |
| L1 / Base Layer | Core blockchain (Ethereum, Solana, etc.) | Consensus security, transaction finality, cryptographic guarantees |
| L2 / Rollups & Scaling | Off-chain computation, batch settlement | Sequencer integrity, fraud proofs, state validation |
| L3 / Application / Protocol Layer | Smart contracts, DAOs, dApps | Business logic correctness, upgradeability, access controls |
| Cross-Layer | Multi-chain interactions | Bridges, oracles, cross-chain messaging, interoperability risk |
Strategic Insight: Treating these layers as separate security silos is no longer sufficient. Risk compounds across layers; a vulnerability at L2 can cascade into L1 or cross-chain liquidity pools.
At the foundation of blockchain security are consensus algorithms and cryptography. These ensure that transactions are immutable and that malicious actors cannot rewrite history.
Key primitives include:
Hybrid Insight: Executives care about trust and compliance; engineers care about atomicity and fail-safe designs. Consensus mechanisms serve both: economic security and auditability.
Trust is no longer binary in multi-chain ecosystems. 2026’s best practices emphasize shared responsibility and layered accountability:
Strategic Insight: Cross-layer participation reduces single-point-of-failure risk while enhancing institutional confidence in Web3 adoption.
[Cross-Layer Security Nerve Center]
│
┌───────┴────────┐
L0 Network — Nodes & Consensus
L1 Base Layer — Core Blockchain Security
L2 Rollups — Sequencer & Fraud Proofs
L3 Application — Smart Contracts / DAOs
Cross-Layer — Bridges, Oracles, Interoperability
Explanation: Each layer feeds into a central Cross-Layer Security Nerve Center that monitors, audits, and enforces policies across all chains and protocols in real time.

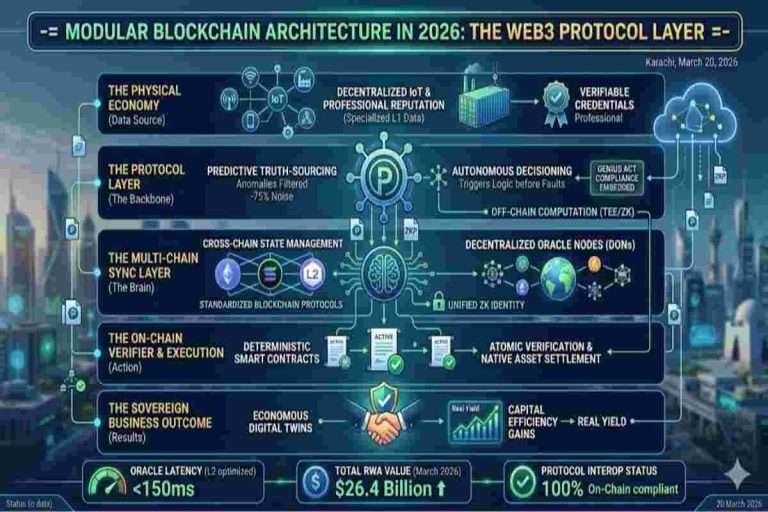
A Cross-Chain Multi-Chain Security Framework (CL-MCSF) is the architecture that ensures atomic security across multiple blockchain layers and protocols. Unlike isolated security models, CL-MCSF treats Layer 1, Layer 2, rollups, bridges, and oracles as a unified domain, allowing institutions to protect capital, governance, and messaging simultaneously. The Cross-Chain Multi-Chain Security Framework serves as the “nerve center” of modern decentralized networks.
In 2026, this framework leverages shared validator sets, real-time threat intelligence, and coordinated monitoring to protect the entire ecosystem simultaneously. By treating multiple layers as a single security domain, it prevents “weak-link” exploits, ensuring that Real Yield generated in one protocol is not compromised by vulnerabilities in another. This centralized coordination of decentralized layers is key to maintaining maximum Capital Efficiency while supporting secure RWA Tokenization.
Key Benefits:
In a composable Web3 world, security is not optional—it is the neural network that protects every flow of value.
Competitor Gap Analysis:
Opportunity: Leverage hybrid pooled validators with AI-driven risk analytics to secure cross-chain bridges, rollups, and oracle feeds simultaneously.
Implementation Concept:
| Component | Function | Security Benefit |
|---|---|---|
| Relay Chains | Connect multiple chains | Shared validation, reduces isolated chain risk |
| Pooled Validators | Validators across protocols | Stronger economic security, failover redundancy |
| Threat Intelligence | Cross-chain monitoring | Early detection of anomalies and exploits |
Security frameworks must be measurable and auditable. 2026 introduces key metrics:
Hybrid Insight: These metrics satisfy both executive oversight and engineering accountability.
2026 Best Practices for CL-MCSF:
Competitor Weakness: Many current frameworks focus only on bridges or rollups. True cross-layer frameworks combine validators, oracles, and transaction sequencing for systemic protection.
[Cross-Chain Security Nerve Center]
│
┌───────┼────────┐
L0 Network — Node & Consensus Validation
L1 Base Layer — Transaction Finality
L2 Rollups — Sequencer & Fraud Proofs
Bridges — Interoperability & Atomic Swaps
Oracles — Real-Time Data Validation
Multi-Chain Monitoring & Threat Analytics
Explanation: The framework continuously monitors all layers, validates cross-chain state changes, and enforces atomic execution while maintaining capital efficiency.
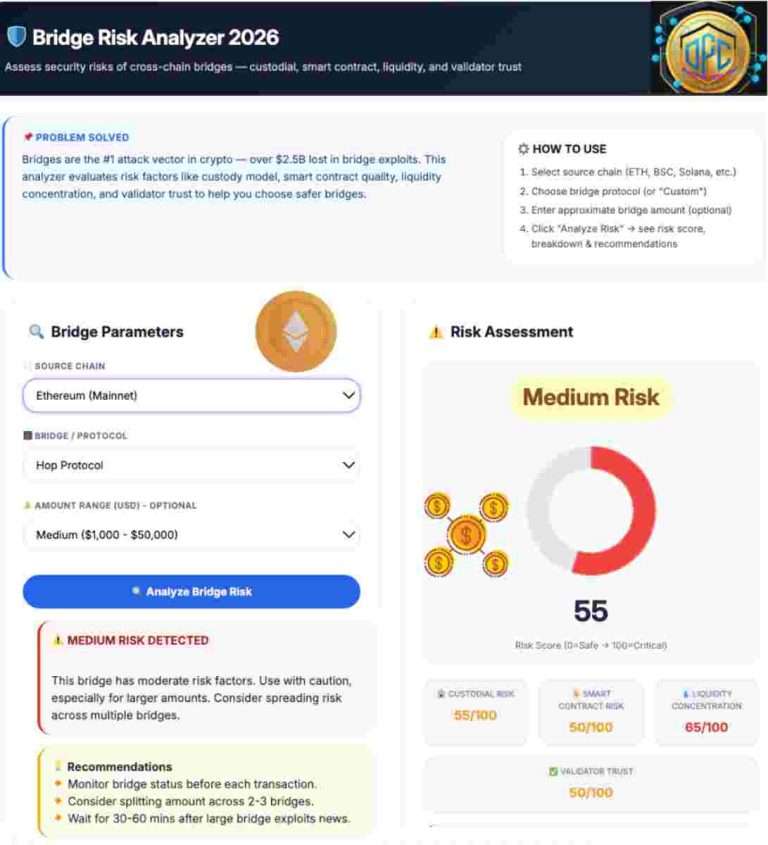
Modern Cross-Layer Bridge Protection Protocols replace outdated, centralized bridges with trustless, decentralized verification systems. By utilizing zero-knowledge proofs (ZKPs), these protocols validate cross-chain state transitions instantly without intermediaries. This approach drastically reduces the attack surface, ensuring that assets moving across layers remain immutable and secure, which is critical for the stability of global DeFi and RWA Tokenization markets.
Cross-chain bridges enable value transfer, messaging, and liquidity between Layer 1 and Layer 2 networks, rollups, and other decentralized protocols. In 2026, bridges are no longer “optional connectors”; they are critical security nodes.
Key Advantages of Modern Bridges:
Quote:
“A bridge is only as strong as its weakest validator — systemic risk lies in ignoring cross-layer security.”
Competitor Gap Analysis:
Opportunity: Implement cross-layer bridge protection protocols that combine multi-sig validators, ZKP verification, and atomic swap orchestration to mitigate risk.
Common Vulnerabilities:
Next-Gen Architecture Components:
| Layer | Function | Security Outcome |
|---|---|---|
| Validator Network | Decentralized, multi-sig | Reduces single point of failure |
| Atomic Swap Engine | Cross-chain transaction orchestration | Ensures all-or-nothing execution |
| Zero-Knowledge Layer | State validation without revealing sensitive data | Reduces attack surface & protects privacy |
| Real-Time Analytics | Continuous monitoring across L1/L2 | Early threat detection & anomaly alerts |
Threat Mitigation Techniques:
Zero-Knowledge Proofs (ZKPs) have become standard for bridge security in 2026. They allow verification of transaction correctness without exposing sensitive states.
Implementation Highlights:
Light client verification complements ZKPs by allowing chains to verify state roots from other chains without storing full node data, enhancing scalability and security simultaneously.
[Cross-Chain Bridge Security Hub]
│
┌─────────┼─────────┐
Validator Network — Multi-sig / Pooled
Atomic Swap Engine — Orchestrated execution
Zero-Knowledge Proof Layer — Instant verification
Real-Time Analytics — Anomaly & Threat Detection
Explanation:
The bridge hub continuously verifies cross-chain states, enforces atomic execution, and mitigates risks with real-time monitoring — acting as the backbone for systemic multi-chain security.

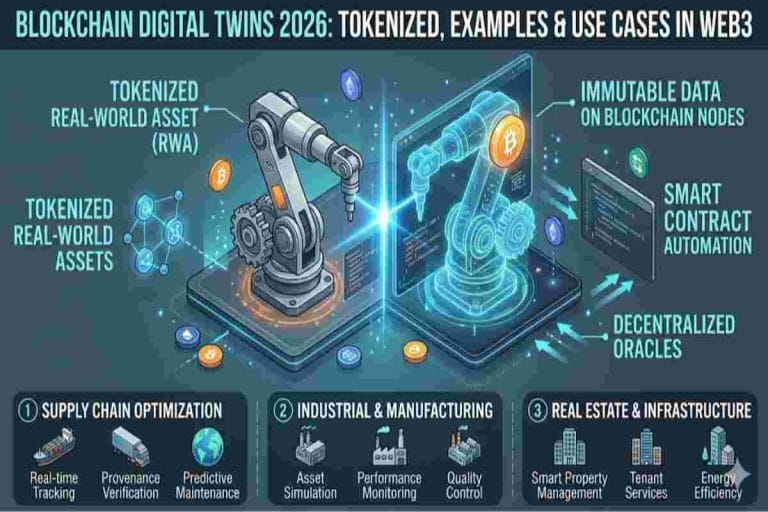
Cross-Chain Rollup Security Mechanisms implement “security inheritance”, allowing secondary layers to leverage the robust economic security of the base Layer 1. Transaction data is posted directly to a high-security Layer 1, ensuring that even if a Layer 2 sequencer fails, user funds remain protected by the base layer’s consensus. This guarantees absolute trust, integrity, and continuity, enabling enterprises and DeFi protocols to scale safely without compromising security.
Rollups in 2026 are no longer isolated Layer 2 scaling solutions; they are integral cross-chain participants in multi-chain ecosystems. As transactions move off the mainnet for efficiency, securing the sequencer, state roots, and fraud proofs becomes critical.
Key Threats:
Quote:
“A compromised sequencer isn’t just a Layer 2 problem—it can cascade through the multi-chain ecosystem.”
Competitor Gap Analysis:
Opportunity: Adopt cross-chain rollup security mechanisms that integrate atomic verification, cross-chain dispute resolution, and sequencer decentralization.
Multi-Layer Proof Mechanisms:
| Component | Function | Security Benefit |
|---|---|---|
| Fraud Proofs | Detect invalid state updates | Prevent malicious state commits |
| ZK Proofs | Verify correctness of L2 computations | Instant, trustless verification |
| Cross-Chain Atomicity | Synchronize with L1 & other L2s | Avoid asynchronous finality issues |
| Sequencer Decentralization | Multiple actors validate batches | Reduces censorship or collusion risk |
By cross-validating proofs across chains, protocols maintain integrity, ensure atomic settlement, and secure liquidity movement.
Best Practices in 2026:
Diagram : Cross-Chain Rollup Security Architecture
[Layer 1 Security Base]
│
▼
[Rollup L2 Sequencers] -- Rotating Validator Sets
│
[Fraud Proof & ZK Proof Verification]
│
[Cross-Chain Atomic Settlement]
│
[On-Chain Audit & Monitoring]
Explanation:
This architecture ensures that state updates, transaction batches, and dispute resolutions are verified across all layers before final settlement, preventing cascading failures in multi-chain systems.
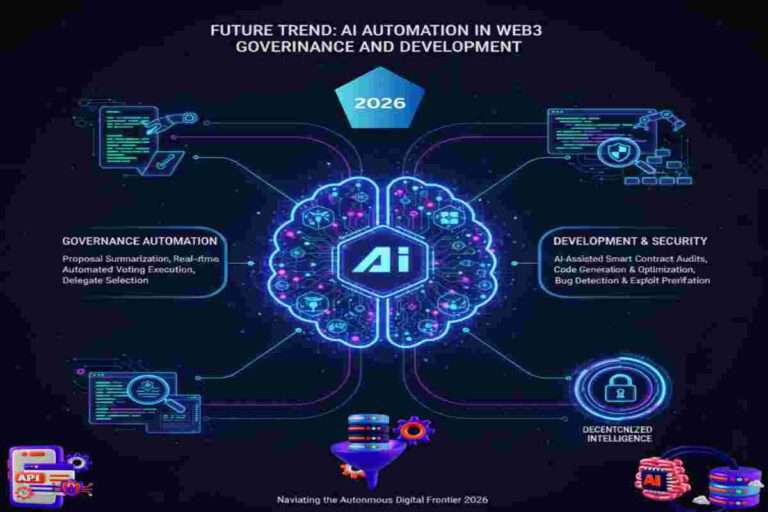
In 2026, interoperability is no longer optional — it is the backbone of multi-chain ecosystems. Cross-Chain interoperability risk arises when transactions, messaging, or data flow asynchronously between chains, creating vulnerabilities like double-spending, delayed finality, or smart contract misalignment. Cross-Chain Interoperability Risk Management addresses the challenges of asynchronous finality across multi-chain systems. By combining AI-powered oracles and atomic swap logic, these frameworks continuously monitor all connected blockchains in real time. Transactions that present risks due to state discrepancies are paused automatically, ensuring atomicity—either transactions complete fully or not at all. This proactive system minimizes the chances of partial failures and protects users from cascading errors in complex multi-chain operations.
Key Risks:
Quote:
“In a multi-chain world, a single asynchronous transaction can ripple across the entire ecosystem.”
Competitor Gap Analysis:
Opportunity: Introduce cross-chain monitoring frameworks that integrate AI-driven anomaly detection with live multi-chain auditing.
Tools & Practices:
| Tool Type | Function | Benefit |
|---|---|---|
| Static Analysis | Pre-deployment checks | Detect logic bugs & vulnerabilities |
| Continuous Monitoring | Watch live transaction flows | Prevent cascading failures |
| Cross-Chain Oracles | Verify multi-chain states | Ensure atomic settlement |
| Automated Alerts | AI/ML anomaly detection | Early threat identification |
Implementation Approach:
Diagram: Cross-Chain Interoperability Risk Monitoring Flow
[Multi-Chain Transaction]
│
[Real-Time SIEM Logging]
│
[Behavioral Analytics + AI Detection]
│
[Anomaly Alert & Pause Mechanism]
│
[Automated Rollback or Manual Intervention]
Explanation:
This framework ensures that cross-chain transactions either execute atomically or are paused, preventing partial failures and protecting both capital and reputation.
Outcome: Cross-chain risk management ensures resilience, transparency, and auditability, even during complex failures, keeping institutional assets and DeFi protocols safe.
In 2026, oracles are the lifeline of cross-chain operations. Data reliability across multiple chains determines whether transactions execute safely, smart contracts enforce conditions correctly, and tokenized assets remain secure.
Key Points:
Competitor Analysis:
| Competitor | Strength | Weakness / Gap |
|---|---|---|
| Chainlink | High reliability, proven L1 feeds | Limited native L2 multi-chain validation |
| Band Protocol | Decentralized, scalable | Limited cross-chain rollup integration |
| DIA | Transparent, open-source | Smaller network of validators, slower response times |
Opportunity: Build cross-chain oracle aggregation protocols that provide atomic validation across chains, bridging the gap left by current competitors.
Defense-in-Depth Strategy:
Layered Security Approach Beyond Bridges
[User / dApp]
│
[Smart Contract Hardening]
│
[MPC Key Management]
│
[Cross-Chain Policy Enforcement]
│
[Decentralized Oracle Validation]
│
[Atomic Transaction Execution]
Outcome: Each layer adds a fail-safe, ensuring systemic resilience even if a single component is compromised.
Why Quantum Resistance Matters:
By 2026, post-quantum cryptography is critical to safeguard long-term assets. Quantum computers could break ECDSA or RSA keys, threatening multi-chain security frameworks.
Strategies Implemented:
Benefits:
Quantum-Resistant Protocol Options Table
| Protocol Type | Security Basis | Use Case |
|---|---|---|
| Lattice-Based | Hard lattice problems | Cross-chain signatures, MPC |
| Hash-Based | One-way hashing | Smart contract authorization |
| Hybrid | Lattice + Classical | Gradual adoption in multi-chain protocols |

In 2026, cross-chain blockchain security cannot succeed without regulatory alignment. Multi-chain systems operate across jurisdictions, and protocols must consider securities law, anti-money laundering (AML), and ESG reporting requirements.
Key Points:
Competitor Gap: Many existing bridges and rollups lack embedded regulatory compliance, relying on off-chain reporting, which slows audits and increases legal exposure.
Cross-chain connectivity introduces new risk vectors that require formal standards and mitigation protocols:
Table: Key Interoperability Standards in 2026
| Standard | Purpose | Adoption Example |
|---|---|---|
| Atomic Cross-Chain Protocols | Prevent partial transaction failure | Polkadot XCMP, Cosmos IBC |
| Shared Validator Frameworks | Unified consensus across layers | Polkadot, Avalanche |
| On-Chain Audit Logs | Transparent reporting for regulators | Layered DeFi Bridges |
Trust is foundational for multi-chain ecosystems. Protocols must combine technical rigor with public accountability:
Example: Leading L2 rollups now publish continuous verification reports and integrate decentralized audit oracles, allowing institutional investors to track multi-chain asset security in real-time.
Even with advanced Cross-chain Security frameworks, real-world incidents reveal systemic weaknesses. Studying past exploits highlights gaps in multi-chain deployments:
Insight: Multi-layered architecture requires holistic monitoring, not just layer-specific security.
| Protocol | Strength | Lessons Learned |
|---|---|---|
| Polkadot XCMP | Shared security across parachains | Relay chain + pooled validators reduce isolated risk |
| Cosmos IBC | Zone-based communication | Incentivized validator cooperation is critical |
| LayerZero | Ultra-low latency bridging | Atomicity + oracle verification prevents partial transfer exploits |
Hybrid Insight: Successful bridges combine multi-layer validator security, cross-chain atomicity, and real-time oracle verification — closing gaps left by previous generation designs.
Protocols that successfully mitigated damage shared common strategies:
Example: A bridge protocol in 2025 prevented $120M in potential loss by using atomic transaction rollback combined with on-chain anomaly detection.
From these incidents, institutions can extract actionable lessons:
Diagram : Multi-Layer Security Incident Flow
[Transaction Initiated on L2]
↓
[Oracle & Atomic Check]
↓
[Anomaly Detected?] → Yes → [Circuit Breaker Triggered] → [Validator Consensus]
↓ No
[Transaction Settled]
↓
[On-Chain Audit Log Updated]
Key Takeaways:
By 2026 and beyond, the multi-chain Web3 ecosystem is set to evolve with systemic, proactive security mechanisms:
Impact: These innovations will reduce attack surface area, increase trust in interoperable DeFi applications, and strengthen institutional adoption.
Cross-Chain Blockchain Security will rely on scalable, decentralized trust models that replace legacy central points of control:
Diagram : Scalable Multi-Chain Interoperability Model
[Layer 1 Blockchain]
↓
[Shared Validator Pool & Consensus]
↓
[Layer 2 / Rollup Networks]
↓
[Atomic Transaction Engine]
↓
[Decentralized Oracles]
↓
[Cross-Chain Governance Layer]
Takeaway: This approach ensures capital efficiency, operational transparency, and real-time risk mitigation, even in highly composable Web3 ecosystems.
The ultimate goal of Cross-Chain Security is to enable a truly decentralized, multi-chain economy:
Quote Hook:
“The future of blockchain security is systemic, composable, and anticipatory — not reactive.”
Key Outlook: Enterprises and protocols adopting cross-chain frameworks now will set the standard for trust, efficiency, and security in the Web3 ecosystem of 2030 and beyond.
Cross-Chain Blockchain Security in 2026 represents a paradigm shift from isolated defense to systemic, multi-chain protection. By implementing Cross-Chain Multi-Chain Security Frameworks, Bridge Protection Protocols, Rollup Security Mechanisms, and Interoperability Risk Management, enterprises and DeFi protocols can safeguard capital, maintain on-chain compliance, and prevent cascading failures across connected networks.
The future of blockchain security is holistic, composable, and proactive—extending beyond smart contract exploits to protect economic incentives, messaging flows, and cross-chain liquidity simultaneously. Institutions that adopt cross-chain security today gain capital efficiency, auditable transparency, and operational trust, laying the foundation for secure, scalable, and interoperable Web3 Security Frameworks.
By 2030, multi-layer, cross-chain defenses will become the standard, ensuring that digital assets, real-world tokenization, and decentralized finance can thrive without systemic risk. In a composable world, security is no longer optional—it is the backbone of trust and growth.
learn more about DeFi https://consensys.net/knowledge-base/defi/
Q: What is Cross-Chain Blockchain Security?
A: Cross-Chain Blockchain Security is a holistic approach that protects assets, messaging, smart contract logic, bridges, rollups, and oracles across multiple blockchain layers, rather than securing single, isolated networks. It focuses on preventing systemic failures in multi-chain ecosystems.
Q: Why is cross-chain security critical for Web3 in 2026?
A: Interoperable blockchains enable capital to flow across multiple layers, increasing utility but also expanding attack surfaces. Strong cross-chain security prevents vulnerabilities from bridges, rollups, and messaging layers, safeguarding both institutional and retail assets.
Q: What are the main risks in cross-chain interoperability?
A: Key risks include asynchronous finality, smart contract flaws in bridges, unreliable oracle data, relayer failures, replay attacks, double-spend windows, and compromised validator keys—all of which can result in partial transactions or asset loss.
Q: How do modern bridges improve security?
A: Modern bridges use decentralized validators, zero-knowledge proofs (ZKPs), atomic swaps, and real-time monitoring to minimize central points of failure, validate cross-chain state transitions, and ensure atomic transaction execution.
Q: What does atomicity mean in cross-chain transactions?
A: Atomicity ensures a transaction either fully completes on all involved chains or fully reverts, preventing partial execution that could lead to inconsistent balances or asset loss.
Q: How do fraud proofs and ZK proofs enhance rollup security?
A: Fraud proofs allow networks to challenge incorrect states (critical in optimistic rollups), while ZK proofs provide cryptographically validated state transitions instantly without revealing underlying data. Both maintain integrity across layers.
Q: Can smart contract audits reduce cross-chain risks?
A: Yes. Audits and formal verification identify vulnerabilities in interoperability and bridging logic. Combined with continuous monitoring, they help prevent exploits before and after deployment.
Q: What is the difference between liquidity fragmentation and interoperability risk?
A: Liquidity fragmentation refers to capital being split across chains, reducing efficiency. Interoperability risk involves vulnerabilities when protocols communicate across chains, such as timing gaps or misaligned messages.
Q: Why are cross-chain bridges often targeted by hackers?
A: Bridges hold large pooled assets, making them high-value targets. Vulnerabilities in smart contracts, centralized validators, or monitoring gaps have historically led to billions in losses.
Q: How does cross-chain security support institutional adoption?
A: It provides systemic risk management, atomic cross-chain guarantees, real-time auditability, and compliance transparency, all essential for institutional confidence and secure integration with enterprise workflows.

Welcome to OwnProCrypto (Own & Pro Crypto) — a next-generation Bitcoin and blockchain education platform where the science of finance meets the power of AI-driven automation.
Our mission is simple: to equip you with the knowledge, frameworks, and tools needed to make smarter financial and business decisions in the Web3 economy.
Beyond analysis, OwnProCrypto focuses on transparency, verifiable data, and practical frameworks that investors and builders can actually use. Our goal is not hype — but clear thinking, disciplined analysis, and long-term value creation in the decentralized economy.
Our Background
As part of the Web3 Ecosystem Architecture pillar, this guide focuses on Sovereign Ownership Architecture in Web3. Explore related pillars: