
ZK Identity Architecture in 2026 has emerged as the foundational pillar of the global Web3 identity layer. This architecture enables a truly decentralized Web3 identity system where individuals—not corporations—control their own credentials. By moving from legacy authentication to a sovereign identity layer, users can verify sensitive data through zero-knowledge proof systems and interact across digital platforms with total privacy. This modern stack connects the identity layer directly to a sovereign internet framework, utilizing verifiable credentials to establish trust without intermediaries. When compared to traditional identity models, the 2026 enterprise implementation model offers superior security, though it requires a disciplined approach to navigate the unique risks and design challenges of decentralized architecture.
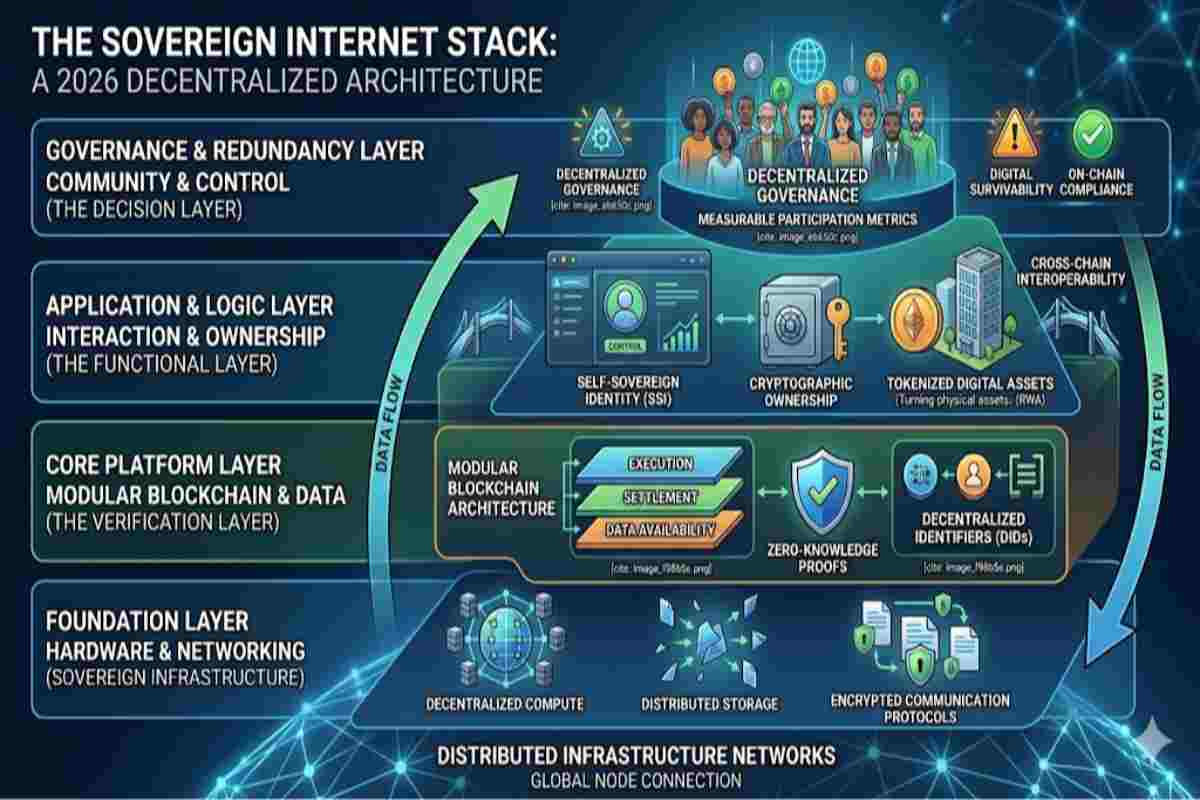
Table of Contents
ToggleThe transition from Web2 to Web3 fundamentally redefines identity. In traditional systems, identity is platform-controlled — stored in centralized databases and monetized by intermediaries. In contrast, ZK Identity Architecture introduces a model where identity becomes portable, programmable, and privacy-preserving.
This architecture enables:
As a result, identity becomes the control layer of the Sovereign Internet, determining access, permissions, and participation across all other layers.
At the core of this architecture are two technologies:
Together, they form the self sovereign identity (SSI) layer, where:
This removes the need for centralized identity providers and creates a trust-minimized identity network.

Decentralized identity Web3 architecture shifts identity from a login mechanism to a system-level primitive.
Instead of:
We now have:
This evolution transforms identity into a shared infrastructure layer, enabling seamless interaction across the Web3 ecosystem.
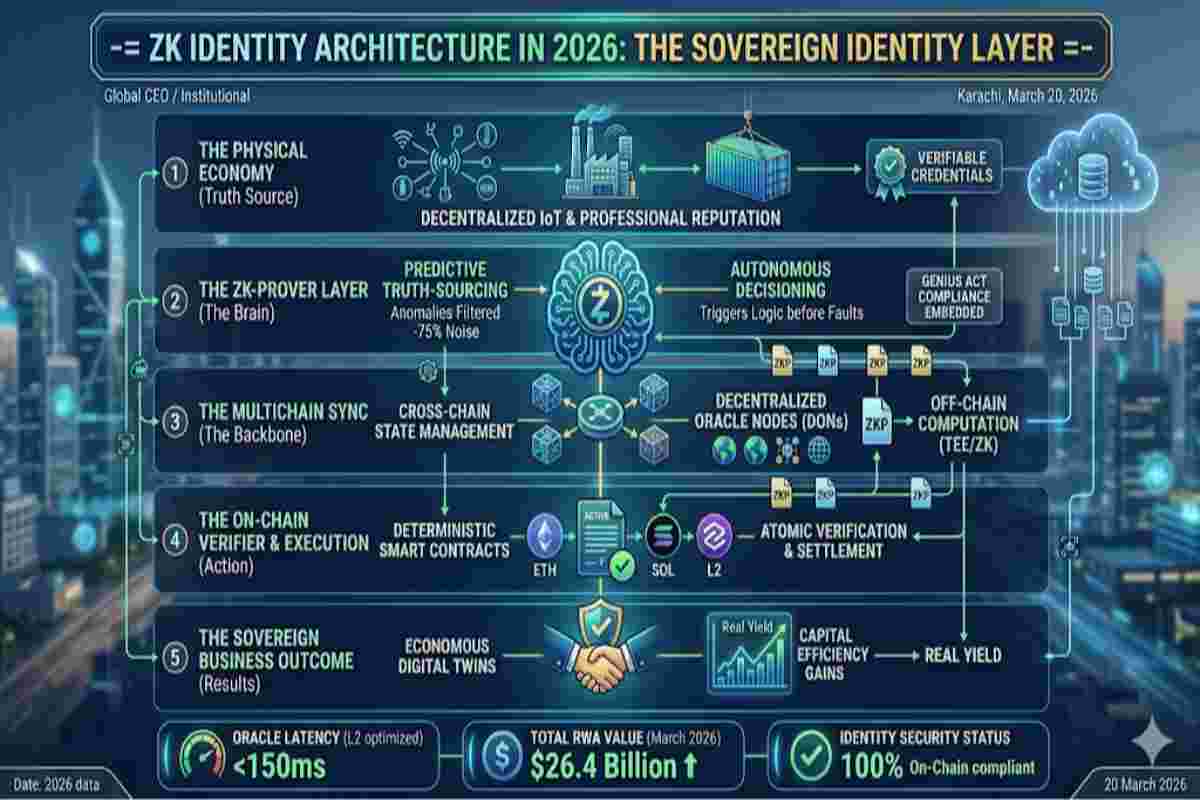
ZK Identity Architecture is built on modular components that interact to form a complete identity system.
| Component | Function | Description |
|---|---|---|
| DID Layer | Identity creation | Generates decentralized identifiers |
| Credential Layer | Data validation | Stores verifiable credentials |
| ZK Proof Layer | Privacy | Enables selective disclosure |
| Storage Layer | Data control | Uses decentralized storage systems |
| Role | Function |
|---|---|
| Issuer | Creates and signs credentials |
| Holder | Stores and controls identity data |
| Verifier | Validates credentials without accessing raw data |
The identity layer is not isolated — it integrates across the entire Web3 architecture:
This makes identity the binding layer of the Sovereign Internet Stack, connecting all systems into a coherent architecture.

Zero knowledge proof identity systems introduce a new paradigm of privacy.
Instead of sharing full data:
This ensures:
ZK proofs transform identity into a privacy-first architecture, critical for global adoption.
Verifiable credentials replace traditional identity verification processes.
instant verification
Identity becomes portable and composable, allowing users to interact across ecosystems without repeated verification.
| Feature | Traditional Identity | Web3 Identity Layer |
|---|---|---|
| Control | Platform-owned | User-owned |
| Privacy | Low | High |
| Verification | Manual | Cryptographic |
| Portability | Limited | Global |
| Security | Centralized | Distributed |

Enterprises are adopting ZK Identity Architecture to:
This creates a scalable and compliant identity system for global operations.
Despite its advantages, challenges remain:
Addressing these requires coordination between technology providers, regulators, and standards bodies like the World Wide Web Consortium.
By 2030, identity will evolve into a universal control layer:
ZK Identity Architecture will define how users interact with the internet — not as accounts, but as sovereign entities.
| Metric | 2024 | 2026 (Est.) | Growth |
|---|---|---|---|
| SSI Users | 50M | 180M+ | 3.6x |
| Verifiable Credentials | 200M | 1B+ | 5x |
| Enterprise Adoption | Early | Scaling | Rapid |

ZK Identity Architecture is a foundational layer within the broader Sovereign Internet Stack, where infrastructure, protocols, identity, and value systems converge into a unified Web3 ecosystem. To understand how all layers integrate into a complete architecture, explore the pillar The Sovereign Internet Stack: Architecture of the Web3 Ecosystem (2026 Guide).
For global standards on decentralized identity and verifiable credentials, refer to the frameworks developed by the World Wide Web Consortium, which define interoperability across identity systems.
The ZK Identity Architecture is the “Logic Gate” of your entire digital presence. Without a sovereign identity layer., the Smart Legal Contract Modules we discussed cannot verify the “Signatory Intent” required for legal standing. Furthermore, this layer acts as the primary firewall for SECURE Pillar strategy; by using [Account Abstraction and Digital Fortresses], your identity remains portable yet shielded from centralized breaches. When moving assets via the MOVE Pillar, specifically for [Insurable Stablecoin Settlements], the identity layer provides the “On-Chain Compliance” (KYC/AML) proofs without revealing your underlying private data, ensuring that your Wealth Architecture remains both private and federally compliant.
As of March 2026, the global standard for identity architecture has shifted toward the W3C Verifiable Credentials (VC) 2.0 and DID Core specifications. This shift is mandated by the eIDAS 2.0 regulation in Europe and the NIST SP 800-63-4 (Digital Identity Guidelines) in the United States, which officially integrated “Subscriber-Controlled Wallets” into the federal federation model in late 2025. These guidelines prioritize Zero-Knowledge Proofs (ZKP) as the primary defense against AI-generated deepfakes and mass data harvesting. For architects implementing these standards, the NIST Digital Identity Resource Center provides the official threat models and conformance criteria for mobile Driver’s Licenses (mDL) and ZK-identity systems: https://www.nist.gov/identity-access-management/digital-identity-guidelines.
ZK Identity Architecture in 2026 represents a fundamental shift in how identity is designed, implemented, and governed. By combining zero knowledge proofs with verifiable credentials, it transforms identity into a modular, privacy-preserving, and interoperable layer of the Web3 stack.
In the Sovereign Internet, identity is no longer a login system — it is the core infrastructure that enables trust, access, and ownership across the entire digital ecosystem.

Welcome to OwnProCrypto (Own & Pro Crypto) — a next-generation Bitcoin and blockchain education platform where the science of finance meets the power of AI-driven automation.
Our mission is simple: to equip you with the knowledge, frameworks, and tools needed to make smarter financial and business decisions in the Web3 economy.
Beyond analysis, OwnProCrypto focuses on transparency, verifiable data, and practical frameworks that investors and builders can actually use. Our goal is not hype — but clear thinking, disciplined analysis, and long-term value creation in the decentralized economy.
Our Background
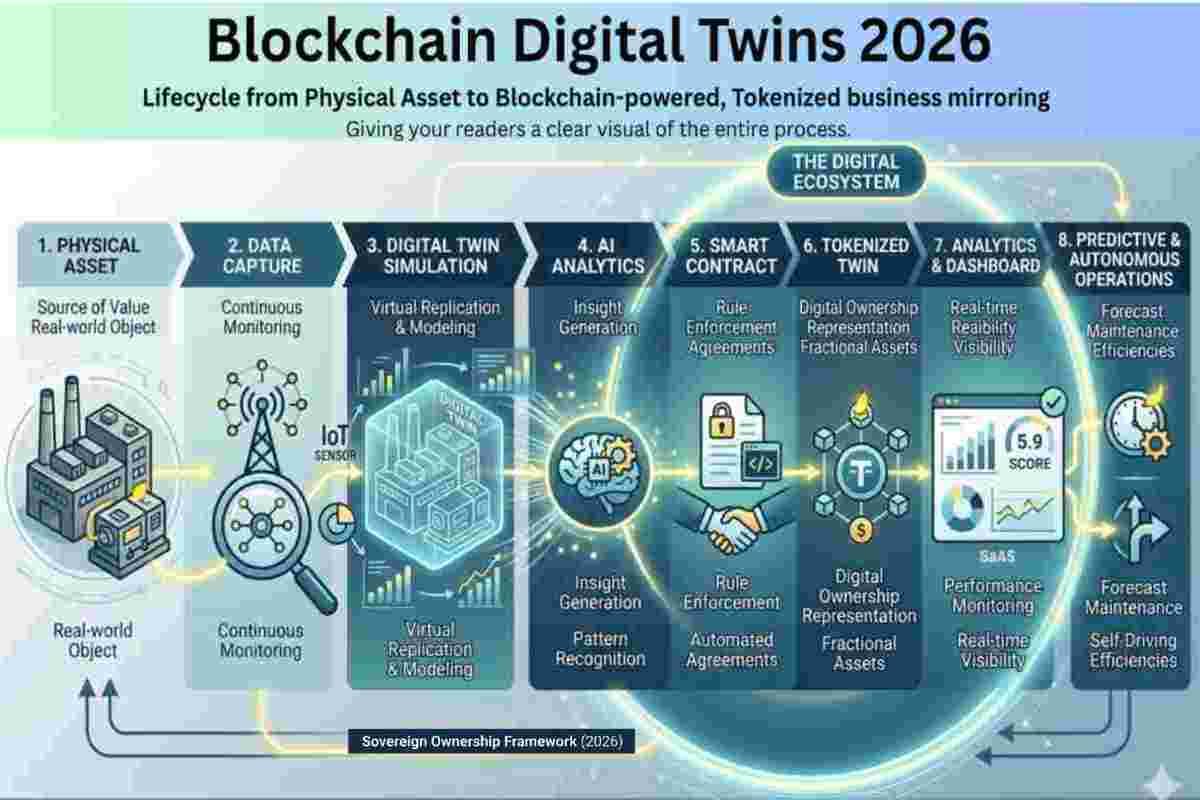
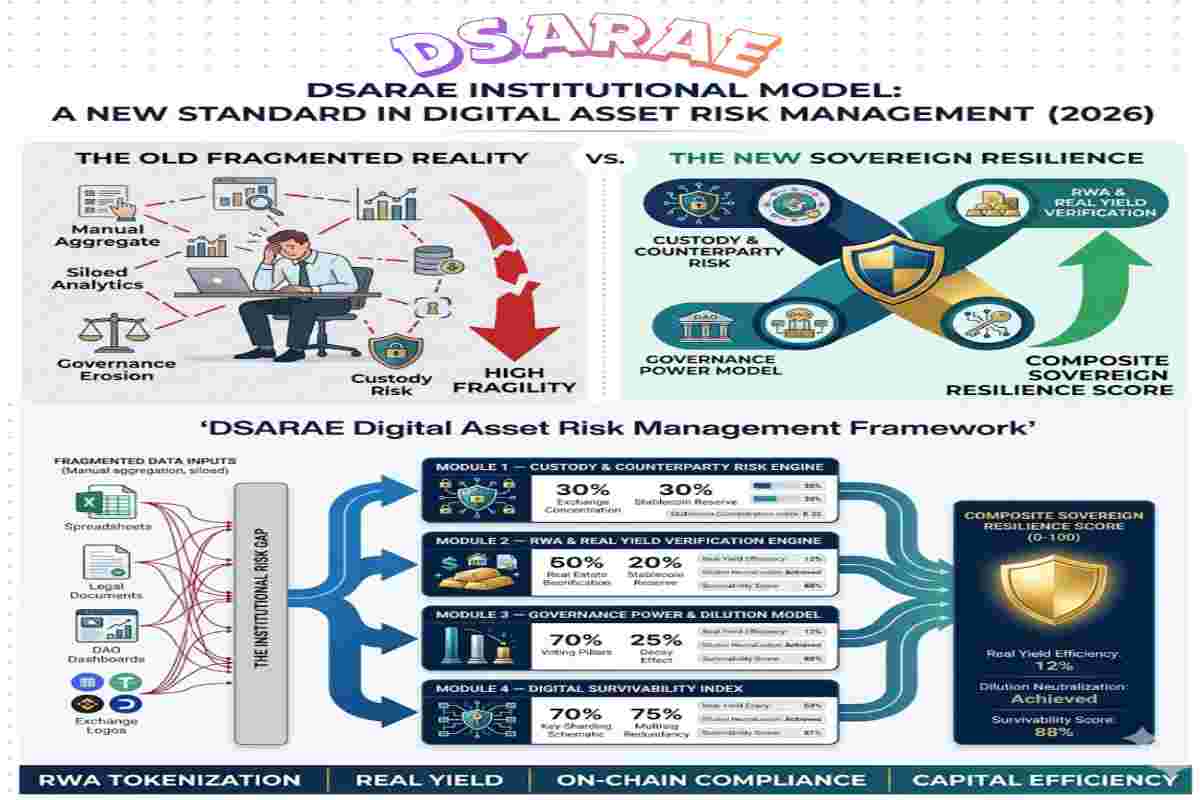
As part of the Web3 Ecosystem Architecture pillar, this guide focuses on Sovereign Ownership Architecture in Web3. Explore related pillars: