

Table of Contents
ToggleCrypto investing has evolved from casual speculation to a critical component of wealth preservation. While retail investors often focus on price movements and short-term gains, family offices and institutional investors prioritize security, risk management, and long-term protection of digital assets.
The reality is stark: most retail investors lack the operational frameworks that family offices employ to secure multi-million-dollar portfolios. This guide will show how you can upgrade your crypto security mindset, moving from retail habits to family office-level protection, without needing to be an institution yourself.
Security failures can erase gains instantly. Unlike traditional finance, cryptocurrency lacks centralized protections—a single compromised private key can result in total loss. Security is no longer optional; it’s the foundation of sustainable crypto investing.
| Feature | Retail Investors | Family Offices / Institutions |
|---|---|---|
| Asset Segregation | Rare | Standard across wallets and accounts |
| Multi-Sig Authorization | Minimal | Required for large transactions |
| Auditing & Monitoring | Sporadic | Regular, automated |
| Custody Solutions | Mostly personal wallets | Third-party or hybrid custody |
| Governance Policies | None | Formal recovery and risk policies |
By following framework-oriented standards, you can:
In 2026, security standards have evolved from simple passwords to multi-layered protocols that protect digital assets against both human error and advanced quantum threats. These frameworks provide a verifiable roadmap for safeguarding private keys across retail and institutional environments.
Crypto security standards are operational frameworks that define how digital assets should be managed, stored, and monitored. They combine technical controls, governance, and risk management, ensuring that assets are protected from theft, loss, and operational mistakes.
Private keys are the heart of crypto ownership. Security standards dictate:
Multi-sig wallets require multiple approvals for a single transaction. They reduce single-point-of-failure risks and are standard for family office operations.
Time-locks prevent immediate execution of large transactions, allowing review and intervention if anomalies are detected.
Even though cryptocurrency is global, high-value portfolios often follow best-practice compliance frameworks, including:
The family office model prioritizes Digital Survivability through governance and redundancy, moving beyond single-point failures to multi-signature and MPC architectures. This approach ensures that high-net-worth assets remain secure, accessible, and transferable across generations.
| Aspect | Retail Mindset | Family Office Mindset |
|---|---|---|
| Asset Handling | Simple wallets | Tiered, segregated accounts |
| Transaction Approval | Single-sig | Multi-sig & time-lock |
| Monitoring | Manual | Automated dashboards & alerts |
| Recovery Planning | Minimal | Formal disaster & succession plans |
| Feature | Retail Investor | Family Office Standard |
|---|---|---|
| Wallet Type | Single hot wallet | Multi-sig + cold storage |
| Custody | Self-managed | Hybrid / institutional custodian |
| Transaction Approval | Single signature | Multi-level approval + time-lock |
| Risk Monitoring | Manual | Automated alerts & periodic audits |
| Recovery Plan | Rare | Documented & tested |

Store the majority of your digital assets in offline environments to eliminate exposure to online threats. Cold storage remains the foundation of long-term crypto security, especially for high-value portfolios.
Note: Includes advanced backup practices such as metal seed phrase storage in multiple secure locations, now considered a 2026 standard.
Require multiple approvals before executing high-value transactions. This removes single points of failure and introduces institutional-grade transaction control.
Note: Advanced setups may incorporate Multi-Party Computation (MPC) as a next-generation alternative to traditional multi-signature wallets.
Separate your crypto holdings into distinct layers—operational funds, long-term storage, and high-security vaults. This minimizes risk exposure and improves control.
Note: Institutional setups often combine segmentation with distributed key management techniques like MPC for enhanced security.
Secure all access points with robust authentication mechanisms to prevent unauthorized entry into wallets and platforms.
Note: This includes Two-Factor Authentication (2FA), Multi-Factor Authentication (MFA), and strong password management practices—the first line of defense for retail and institutional users alike.
Ensure that private keys and recovery phrases are securely backed up and protected against loss, theft, or damage.
Note: Best practices include offline backups, geographically distributed storage, and metal-based seed phrase protection for long-term durability.
Leverage professional custody services for large holdings to reduce operational risk and enhance asset protection.
Note: Family offices typically use regulated and insured institutional-grade custody providers for secure vaulting and compliance.
Establish clear rules for transaction approvals, access control, and emergency recovery. Governance ensures continuity and reduces human error.
Note: This includes formal recovery plans, role-based access control, and secure credential management (password hygiene + access policies).

Implementing these standards requires a stack of hardware-isolated cold storage, metal seed backups, and institutional-grade MPC (Multi-Party Computation) platforms. Combining these tools creates a “Digital Fortress” that balances deep security with the liquidity needed for modern wealth management.
| Wallet / Custodian | Type | Security Features | Best For |
|---|---|---|---|
| Ledger / Trezor | Hardware | Air-gapped, multi-sig compatible | Cold storage |
| Fireblocks | Institutional | Multi-sig, monitoring, insurance | Hybrid custody |
| BitGo | Institutional | Multi-sig, insurance | Large holdings |
| MetaMask + Gnosis | Software | Multi-sig, hot wallet management | Operational funds |

Continuous surveillance and periodic third-party audits are the final defense layers, ensuring that your security “Fortress” evolves alongside emerging 2026 threats. Regularly updating firmware and rotating access keys prevents stagnant vulnerabilities from being exploited by automated AI-driven attacks.
| Threat | Retail Exposure | Family Office Mitigation |
|---|---|---|
| Phishing | High | Email verification & training |
| SIM Swap | Moderate | Multi-factor & hardware authentication |
| Wallet Compromise | High | Multi-sig & cold storage |
| Smart Contract Bug | Moderate | Audited contracts only |
| Insider Risk | Rare | Role-based access & approvals |
Crypto security isn’t just about wallets anymore — it’s a layered system that evolves from retail habits to institutional-grade protection frameworks.
Most people still don’t see this part →
Crypto Security Standards: From Retail to Family Office-Level Protection
What is crypto security and why does it matter?
Crypto security refers to the systems, tools, and practices used to protect digital assets from theft, loss, or unauthorized access.
Unlike traditional finance, transactions are irreversible.
The obvious narrative is wrong →
Financial Sovereignty (2026)
How do private keys and seed phrases work?
Private keys give direct control over your crypto, while seed phrases act as the master backup.
Whoever holds them controls the assets.
This is the part most skip →
Crypto Self Custody Security Toolkit 2026
Why should you never store your seed phrase online?
Online storage exposes your keys to hacking and malware.
True security begins offline.
It’s subtle, but it matters →
Asset Security 2026
What is a hardware wallet and when should I use one?
A hardware wallet stores your keys offline, making it ideal for long-term holding.
This is where it starts getting interesting →
Crypto in Pakistan (2026 Guide)
How does 2-Factor Authentication (2FA) improve security?
2FA adds a second layer beyond passwords, reducing unauthorized access risks.
Look closer →
Top Blockchain Mistakes
Why should SMS-based 2FA be avoided?
SMS authentication can be compromised via SIM swapping.
Use authenticator apps instead.
Don’t ignore this →
Zero-Trust Interoperability
How should I protect my email linked to a crypto account?
Secure your email with strong passwords and 2FA.
Email compromise often leads to asset loss.
Right here →
Digital Asset Taxation
How do I choose a secure crypto exchange?
Look for strong security records, transparency, and compliance.
This doesn’t match the headlines →
Crypto Market Update
What is Proof of Reserves (PoR) and why is it important?
PoR verifies that exchanges hold sufficient assets.
Been tracking this quietly →
Institutional Crypto Settlement 2026
What security features should a trading platform have?
Cold storage, withdrawal controls, and monitoring systems are essential.
Small detail, big shift →
Enterprise Crypto Stack
What is institutional crypto custody and how does it work?
Institutional custody uses regulated infrastructure and layered approvals.
Not everyone’s ready for this yet →
Family Office (2026)
Why do family offices need stronger security frameworks?
Large portfolios require governance and operational controls.
Everyone’s late to this angle →
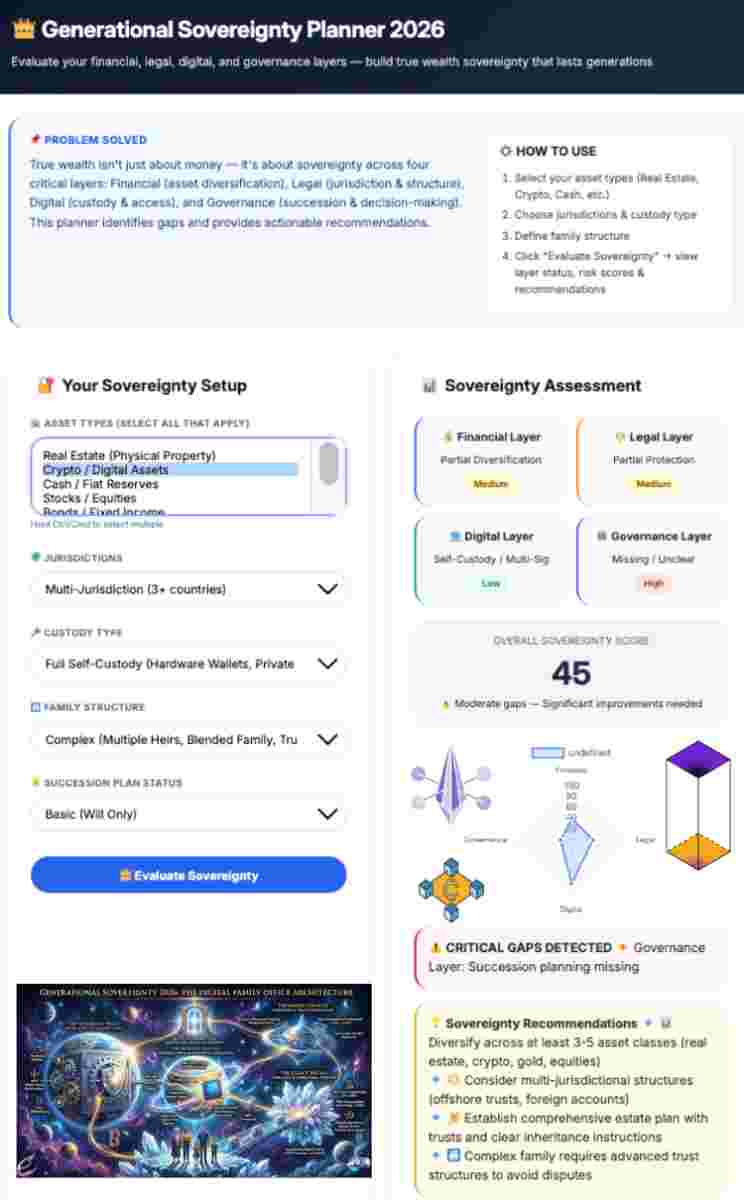
Generational Sovereignty
Which frameworks like ISO/NIST apply to family offices?
Frameworks like ISO 27001 and NIST help standardize risk management.
This is early, not obvious →
Digital Family Office Architecture
What is multi-signature wallet technology?
Multi-signature wallets require multiple approvals for transactions.
Bitcoin isn’t doing what you think →
Bitcoin Deep Dive
What role do smart contract audits play in security?
Audits detect vulnerabilities before deployment.
Weird signal forming here →
Tokenomics Explained
How do you build a key management policy with rotation & backups?
Define key lifecycle, storage, rotation, and recovery strategies.
Before this flips →
Web3 Governance Framework
How do family offices secure cryptocurrency?
Through multi-layer custody, multi-signature approvals, and governance frameworks.
Window’s still open (barely) →
Institutional Asset Security
What makes crypto security different for high-net-worth investors?
Scale demands institutional-grade infrastructure and controls.
This is early, not obvious →
Global Asset Decoupling
Are multi-signature wallets necessary for serious portfolios?
Yes, they eliminate single points of failure.
It won’t stay this quiet →
RWA Tokenization
Can crypto ever be fully safe from hacks?
No system is completely secure, but layered defenses reduce risk.
Look closer →
Zero-Trust Interoperability
What are the most common mistakes retail investors make?
Single-wallet reliance, weak backups, and lack of monitoring.
This part →
Top Blockchain Mistakes
Elevating your security to family office standards is no longer a luxury, but a necessity for surviving the 2026 threat landscape. By adopting institutional-grade hygiene and redundant backup protocols, you ensure your digital legacy remains unshakeable.
For official guidance on digital asset risks, compliance, and investor protection, refer to global regulatory frameworks and public advisories.
this doesn’t match the headlines → U.S. SEC Cybersecurity & Digital Asset Guidance

Welcome to OwnProCrypto (Own & Pro Crypto) — a next-generation Bitcoin and blockchain education platform where the science of finance meets the power of AI-driven automation.
Our mission is simple: to equip you with the knowledge, frameworks, and tools needed to make smarter financial and business decisions in the Web3 economy.
Beyond analysis, OwnProCrypto focuses on transparency, verifiable data, and practical frameworks that investors and builders can actually use. Our goal is not hype — but clear thinking, disciplined analysis, and long-term value creation in the decentralized economy.
Our Background
As part of the Web3 Ecosystem Architecture pillar, this guide focuses on Sovereign Ownership Architecture in Web3. Explore related pillars: