
A diagnostic engine that exposes hidden failure points in your crypto setup

This guide introduces a smarter approach: a complete crypto self custody security toolkit designed to help you secure, manage, and future-proof your digital assets.
In 2026, millions in crypto are lost every year, not hacks, but poor self-custody decisions.
I ran a simple self-custody audit… and it told me I would lose everything in under 48 hours.
If you’re still relying on exchanges or incomplete security setups, you’re exposed to hidden risks that most investors don’t realize until it’s too late.
I thought my setup was solid. Hardware wallet? 2FA enabled? Backup written down?
Then I ran a self-custody audit. Score: 42 / 100
The verdict? High probability of irreversible asset loss due to single-point failure and no inheritance path.
That’s when it hit me: I didn’t have a security system. I had a collection of tools pretending to be one.
So I built something different.
A system that doesn’t just store your crypto, but stress-tests your entire setup like an attacker, a regulator, and your future heirs.
This toolkit serves as a practical expansion of our Asset Security 2026 strategy for building a truly unshakeable digital fortress.
Table of Contents
ToggleCrypto self custody security means you—not an exchange—control your private keys and assets.
Instead of trusting third parties, you build your own security system using tools like:
In simple terms: If you don’t control the keys, you don’t own the crypto.

Here’s a practical framework for how to secure crypto assets in 2026:
Use self-custody wallets instead of leaving assets on platforms.
Cold storage protects against online attacks.
Avoid SMS—use hardware keys like YubiKey.
Split control across multiple devices or people.
Use multiple secure locations (not just one paper backup).
Ensure trusted individuals can access assets if needed.
Other content says:
You say:
That’s elite-level content.

The Sovereign Toolkit 2026 is a structured system that combines:
Help you transition from weak setups to a fortress-level crypto security architecture.
You answer ~15 brutally specific questions:
Then the system does something most guides don’t:
It models your failure scenarios
Not theory. Actual outcomes like:
You get a score:
Now instead of saying:
“Use a hardware wallet”
It builds you a specific architecture:
Example:
“Orange Pill Stack”
Not advice. A blueprint.
A single point of failure can wipe out your entire portfolio.
Whether it’s:
Without proper planning, recovery is often impossible.
Because it’s modular advice without system thinking.
People end up with:
That’s not security.
That’s a single point of failure with extra steps.

Despite growing awareness, most users still:
Analyzes your setup across 5 critical areas:
Output: A clear score (e.g., 90/100 = Fortress Level)
Build a personalized setup based on your needs:
Each stack includes:
You get a simplified blueprint of your system:
Crypto inheritance planning is one of the most overlooked areas in security.
Without it:
The goal is balance:
Access for heirs without compromising security today.

To achieve best crypto security practices, follow this checklist:
Using a hardware wallet combined with multi-signature security provides the highest level of protection for long-term holdings.
this is where it starts getting interesting →
Crypto Self Custody Security Toolkit 2026
How does multi-signature wallet security work?
It requires multiple approvals (keys) to authorize a transaction, eliminating single points of failure.
small detail, big shift →
Institutional Asset Security 2026
What happens to crypto after death?
Without a proper inheritance plan, crypto assets can be permanently lost due to inaccessible private keys.
not everyone’s ready for this yet →
Legacy & Sovereignty (2026)
Is keeping crypto on exchanges safe?
No. Exchanges introduce counterparty risk, meaning you don’t fully control your assets.
the obvious narrative is wrong →
Crypto Security Standards
What is an air-gapped wallet?
An air-gapped wallet is a device that never connects to the internet, making it highly resistant to remote attacks.
look closer →
Asset Security 2026
How do I avoid losing private keys?
Use redundant backups and advanced methods like Shamir Secret Sharing to distribute recovery risk.
this part →
Generational Sovereignty 2026
What is self-custody in crypto?
Self-custody means you control your private keys without relying on third parties, giving you full ownership and responsibility.
most people still don’t see this part →
Financial Sovereignty
Why is single-wallet storage risky?
Relying on one wallet creates a single point of failure, which can lead to total loss if compromised.
don’t ignore this →
Top Blockchain Mistakes
What is Shamir Secret Sharing in crypto security?
It splits a private key into multiple parts, requiring a minimum number of pieces to reconstruct it, improving backup security.
it’s subtle, but it matters →
Digital Family Office Architecture
How often should I check or audit my crypto security setup?
Regular audits help identify vulnerabilities, especially after major transactions or changes in storage methods.
been tracking this quietly →
Crypto Market Update
What is the biggest risk in self-custody?
Human error remains the biggest risk, including lost keys, poor backups, and phishing attacks.
this doesn’t match the headlines →
Crypto Trends 2026
Can beginners safely use self-custody wallets?
Yes, but they should start with simple setups and gradually adopt advanced security practices as their holdings grow.
window’s still open (barely) →
Crypto in Pakistan Guide
The shift toward self-custody is no longer optional—it’s essential.
The difference between losing everything and achieving financial sovereignty comes down to one thing:
Your security system.
The Crypto Self Custody Security Toolkit 2026 gives you a clear, structured way to:
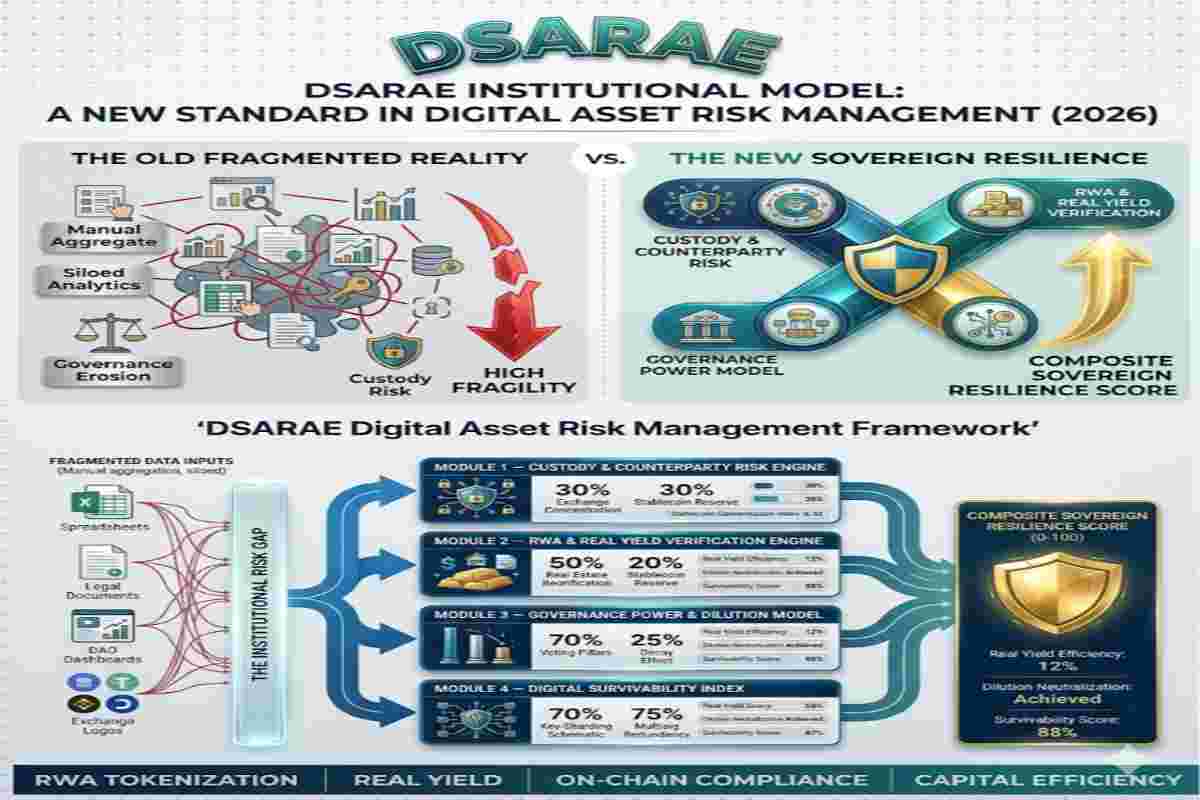
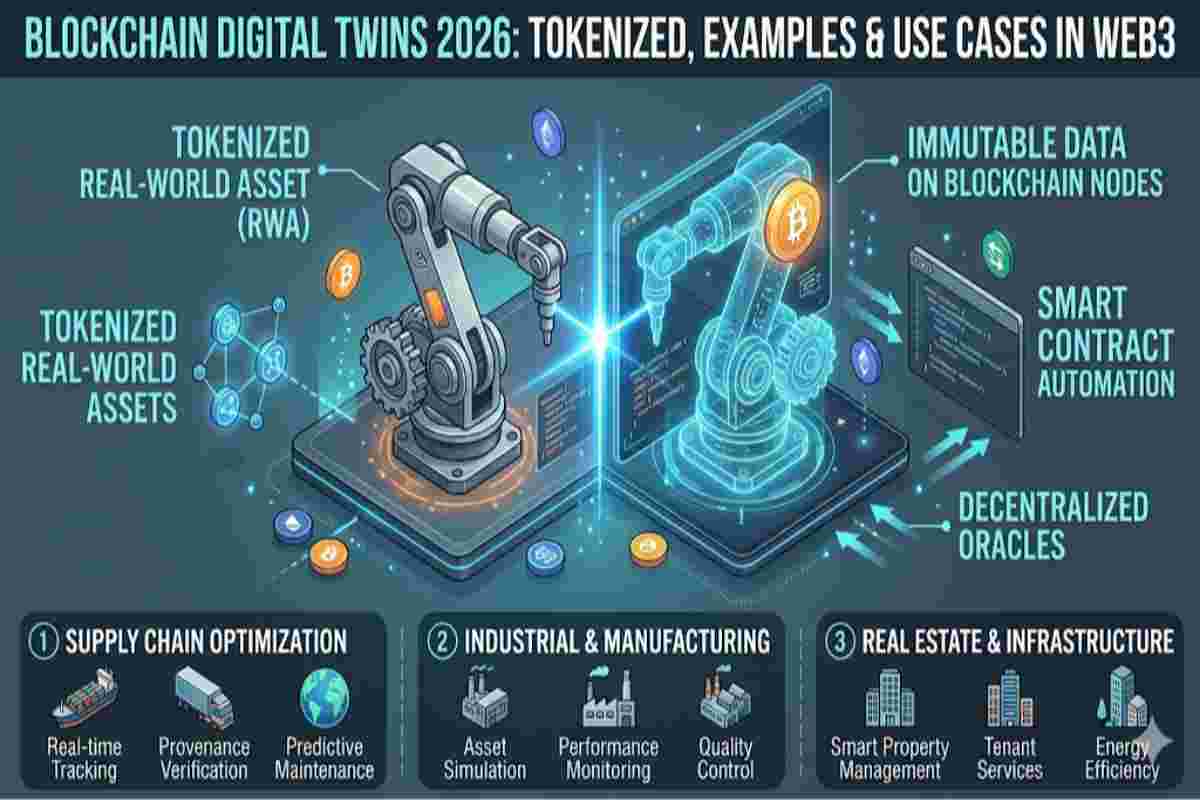
To truly master the Institutional Crypto Custody Architecture of 2026, one must look beyond market volatility and toward the structural evolution of global finance. As the Web3 Ecosystem matures, the integration of RWA Tokenization and On-Chain Compliance is becoming a standard requirement for Tier-1 asset managers. Understanding how international bodies are framing these digital sovereign assets is critical for any firm prioritizing Capital Efficiency and long-term risk management.
Global Strategy Reference:
For official guidance on digital asset risks, compliance, and investor protection, refer to global regulatory frameworks and public advisories.
this doesn’t match the headlines →
U.S. SEC Cybersecurity & Digital Asset Guidance

Welcome to OwnProCrypto (Own & Pro Crypto) — a next-generation Bitcoin and blockchain education platform where the science of finance meets the power of AI-driven automation.
Our mission is simple: to equip you with the knowledge, frameworks, and tools needed to make smarter financial and business decisions in the Web3 economy.
Beyond analysis, OwnProCrypto focuses on transparency, verifiable data, and practical frameworks that investors and builders can actually use. Our goal is not hype — but clear thinking, disciplined analysis, and long-term value creation in the decentralized economy.
Our Background
As part of the Web3 Ecosystem Architecture pillar, this guide focuses on Sovereign Ownership Architecture in Web3. Explore related pillars: