
Problem → Shift → Solution → Framework → Outcome → Risks → Signals → Legacy
Table of Contents
ToggleSecuring Your Identity and Wealth for the Multi-Generational Digital Era.
In 2026, sovereignty is no longer just about “owning crypto”—it is about Continuity. As our lives migrate fully on-chain, the risk of a “Digital Black Hole” (losing access to your identity or assets upon death or system failure) has become a systemic threat. This pillar outlines the framework for building a Sovereign Legacy that integrates legal protections with immutable smart contract inheritance.
The 2026 Legacy Pillars:
Legacy & Sovereignty in 2026 address a growing structural problem: individuals are building careers, assets, and reputations inside platforms they do not control—systems where access can be restricted, credentials are siloed, and decades of value can disappear overnight. As the digital economy matures, a fundamental shift is underway—from platform-dependent ownership to self-sovereign control, where identity, income, and assets move beyond institutional boundaries and onto persistent digital rails. In response, Legacy & Sovereignty emerge not as abstract ideals but as practical solutions—enabling individuals to secure their digital presence, protect long-term value, and maintain continuity across technological and life transitions. This is operationalized through a sovereign architecture framework that integrates on-chain identity, programmable assets, portable reputation, and resilient access systems into a unified structure designed for durability and transferability. The outcome is a new model of digital permanence—where what you build is not only owned, but continues to function, compound, and retain value beyond platforms, jurisdictions, and even your lifetime.
Inheritance without sovereignty is simply delayed loss.
Legacy is no longer defined by what you leave behind. It is defined by what continues to operate in your absence.
Sovereign career architecture reframes how value is built and preserved. Income streams, credentials, and decision rights are no longer tied to a single employer, platform, or jurisdiction. Instead, they are designed to persist—structured as portable, verifiable, and programmable systems.
In this model:
The shift is structural: from employment to infrastructure, from dependency to ownership.
Across both crypto-native and traditional environments, one pattern is consistent—failure rarely comes from lack of skill. It comes from reliance on systems that were never designed for long-term control.
Platform lock-in, opaque credentialing, restricted access, and weak succession planning quietly erode value over time. What appears stable can disappear overnight.
By contrast, those who design for Legacy & Sovereignty build systems that compound. Their identity, assets, and work persist across platforms and market cycles rather than resetting with each disruption.
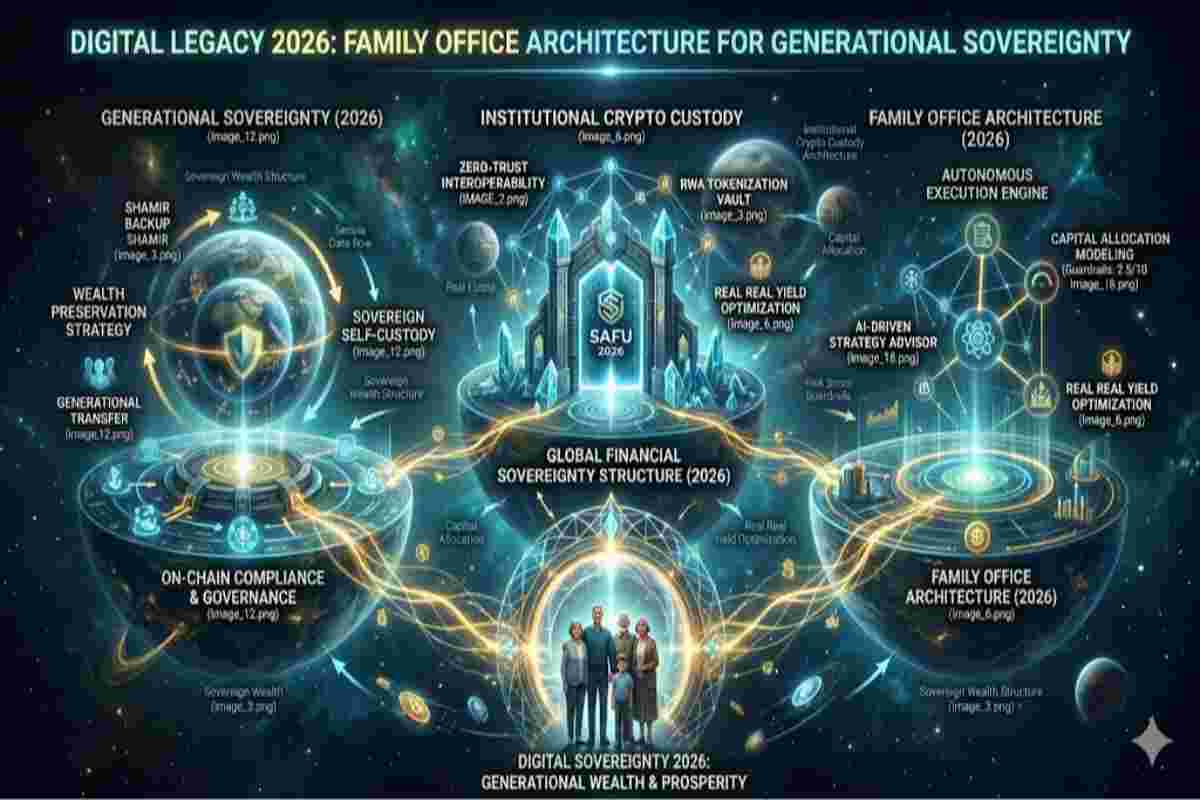
While digital legacy is about the individual, the Sovereign Family Office (SFO) is the architecture for generational continuity. In 2026, elite families are transitioning from traditional paper-based trusts to Sovereign Tech Stacks.
Key Architecture Pillars:
True sovereignty is the ability to maintain control over identity, income, access, and decision-making—regardless of platform, jurisdiction, or technological change.
It transforms fragmented accounts, wallets, and credentials into a unified system:
This is not abstraction—it is architecture.
This guide outlines how to design a sovereign digital foundation—one that aligns career architecture with asset control, protects your on-chain identity, and ensures continuity beyond your direct involvement.
You will learn how to:
Because in the Web3 era, the difference between exposure and endurance is not talent.
Watch: Launching Your Digital Headquarters Build a Web3 Website in 5 Minutes
A digital legacy includes everything you leave behind online: social media accounts, emails and cloud storage, photos, videos, personal documents, digital businesses and domains, cryptocurrencies, NFTs, and even AI-generated profiles and long-term data trails. Unlike physical assets, digital assets do not automatically transfer after death. Without intentional planning, accounts can be locked, deleted, or exploited by platforms or third parties. Modern digital legacy planning ensures your digital life is documented, protected, and transferred according to your wishes. Your digital legacy is no longer optional — it is a core component of personal legacy and sovereignty planning in 2026. ↓ Jump to 2026 Legacy: Expert FAQs & Troubleshooting.
Digital sovereignty means you own and control your digital identity, data, and assets rather than platforms, employers, or governments. While self-custody focuses on holding private keys, sovereignty extends further — it governs how identity, reputation, access, and data persist over time. In the context of legacy planning, digital sovereignty ensures your data is not misused after death, your online identity is not hijacked or erased, and your digital assets remain accessible to trusted parties. Without sovereignty, your digital legacy depends on platform policies rather than personal intent.
Before careers, income, or reputation can persist, control must exist. Sovereignty is the precondition that allows any digital career, asset, or identity to survive platform failure, jurisdictional change, or institutional collapse. Without sovereignty, careers remain dependent on employers, platforms, or intermediaries. With sovereignty, individuals retain optionality — the ability to move, adapt, and reconfigure their economic life without losing identity or access. In Web3-era systems, sovereignty comes first; careers are built on top of it, not the other way around.
Legacy and sovereignty together form a framework where your digital life remains protected, autonomous, and aligned with your values beyond physical existence. In 2026, as careers, income, identity, and reputation increasingly live on-chain or online, failing to secure sovereignty exposes individuals to irreversible loss of control.
Modern digital careers no longer resemble traditional employment. They function as economic systems composed of reputation, access rights, income streams, and governance participation. Protocols, DAOs, and on-chain markets replace companies as the primary coordinators of work and value exchange. In these systems, careers do not reset when platforms change or employers disappear. Instead, identity and contribution history persist across networks, allowing long-term continuity that was impossible in traditional job-based models. ↓ Jump to 2026 Legacy: Expert FAQs & Troubleshooting.
When someone passes away without a digital plan, families often lose access to photos and memories, crypto assets become permanently unrecoverable, businesses and domains expire, and personal data remains exposed. Securing your digital life beyond death protects emotional memories, financial digital assets, personal identity, reputation, and posthumous privacy rights. Legacy and sovereignty are not driven by fear — they are about continuity, dignity, and long-term control.
Stablecoins provide a non-volatile medium for Capital Efficiency, allowing for automated, cross-border payroll and pension smart contracts that remain operational regardless of local banking stability. By utilizing regulated tokens like USDC under the GENIUS Act, professionals ensure their earning power and global liquidity remain always-on.

By 2026, stablecoin-powered cross-border payments have significantly disrupted the legacy correspondent banking system. Instead of relying on slow SWIFT messaging, intermediary banks, and multi-day T+2 or T+3 settlement cycles, businesses can now transfer value globally in near real time using blockchain-based stablecoins. Transactions settle within seconds or minutes, dramatically reducing counterparty risk, operational friction, and hidden intermediary fees.
Dollar-backed digital assets such as USD Coin and Tether enable 24/7 liquidity movement across borders without dependency on traditional banking hours, regional clearing systems, or holiday schedules. For multinational corporations, exporters, remote workers, and global DAOs, stablecoins provide programmable treasury management, instant FX settlement, and transparent on-chain auditability.
This shift represents more than payment acceleration — it marks the modernization of global financial rails. By bypassing correspondent banking layers and enabling peer-to-peer value transfer on decentralized networks, stablecoin infrastructure establishes continuous, programmable capital flows. Within a sovereign digital economy, cross-border payments are no longer constrained by geography or institutional gatekeepers, but powered by always-on blockchain liquidity.
The rise of stablecoin B2B payments is driven by the need for instant settlement, automated reconciliation, and cash-flow efficiency. Leveraging smart contracts such as “Pay-on-Receipt,” enterprises can automatically release payments the moment a digital bill of lading or invoice is verified on-chain. This eliminates manual wire tracking, reduces administrative overhead, and closes the traditional cash-flow gap between suppliers and buyers. By embedding programmable logic directly into the payment process, businesses achieve operational efficiency while maintaining transparency, auditability, and full control over treasury flows.
Selecting between USDT and USDC is a critical decision for modern treasury operations. USDT (Tether) dominates in global liquidity and emerging market corridors, providing fast, widely accepted settlement channels. USDC (Circle), by contrast, emphasizes regulatory compliance, transparency, and fully reserved, auditable balances preferred by Western institutional auditors. The optimal choice depends on the enterprise’s priorities: whether maximizing reach and liquidity or adhering to strict jurisdictional and compliance requirements. A sophisticated cross-border strategy often leverages both, balancing efficiency, trust, and risk mitigation. ↓ Jump to 2026 Legacy: Expert FAQs & Troubleshooting.
Modern blockchain payment infrastructure forms the backbone of programmable, cross-border financial flows. Unlike legacy correspondent banking rails built on decades-old mainframe technology, blockchain-native systems are API-first, composable, and fully programmable. This allows businesses to integrate advanced logic—such as automated tax withholding, revenue sharing, escrow, or treasury allocation—directly into transactions. By combining smart contracts, tokenized assets, and interoperable networks, blockchain payment infrastructure enables seamless B2B payments, faster liquidity cycles, and fully auditable digital workflows, redefining the efficiency of global commerce.
In 2026, sovereign career architecture is redefining the traditional employment model. Instead of relying on a single employer, professionals design their careers as interoperable systems of income streams, tokenized intellectual property, on-chain reputation, and decentralized ownership. This model empowers individuals to operate as independent economic entities within the broader Web3 and digital asset ecosystem.
Sovereign career design integrates decentralized identity (DID), wallet-based credentials, DAO participation, creator monetization, equity tokens, advisory allocations, and revenue-sharing smart contracts. Skills, contributions, and governance participation are recorded on-chain, forming a portable professional ledger that moves seamlessly across protocols, platforms, and jurisdictions. Rather than renting labor to centralized corporations, individuals build compounding digital assets—content, code, research, community equity, and tokenized IP—that generate long-term value.
This architecture ensures professional capital remains permissionless, censorship-resistant, and globally accessible. In a sovereign digital economy, career mobility is no longer constrained by geography, gatekeepers, or institutional hierarchy. Instead, it is governed by reputation, verifiable contribution, and programmable ownership—transforming work itself into a decentralized, self-sovereign asset class.
The rise of borderless Web3 careers has decoupled professional opportunity from geographic, institutional, and jurisdictional constraints. Through decentralized coordination layers, remote collaboration tools, and DAO-based governance systems, professionals can contribute to global blockchain protocols from anywhere in the world. Compensation is often distributed in liquid digital assets, stablecoins, or governance tokens, bypassing the friction, delays, and gatekeeping of legacy banking infrastructure. This shift enables a truly global talent marketplace where skill, contribution, and verifiable output matter more than physical location or corporate affiliation.
An on-chain work identity serves as a verifiable, immutable record of professional contributions, skills, and reputation. Unlike a traditional résumé or LinkedIn profile that relies on self-reported achievements, blockchain-based identity systems use verifiable credentials, wallet histories, and soulbound tokens to cryptographically prove participation, governance voting, code commits, and community impact. This creates a “trustless resume” that allows individuals to access high-value opportunities based on demonstrated performance rather than institutional pedigree. In a sovereign career model, reputation becomes a portable digital asset.
A robust Web3 career framework prioritizes optionality as the ultimate form of professional security. Rather than optimizing for job titles or corporate hierarchy, individuals focus on accumulating digital assets, token allocations, governance rights, intellectual property, and networked reputation. Income streams may include protocol contributions, advisory roles, token incentives, revenue-sharing agreements, and creator monetization. This framework acts as a strategic roadmap for maintaining long-term relevance and financial sovereignty in an era defined by AI automation, decentralized coordination, and rapidly evolving digital markets.
A future-ready digital legacy is vulnerable without structure. Platform shutdowns, forgotten credentials, policy changes, and centralized control represent the biggest risks to digital legacy systems. Without independent documentation, encryption, and sovereignty tools, digital lives remain fragile and failure-prone.
Social media, email, subscriptions, SaaS tools, and financial platforms must be documented and governed with clear intent.
Includes cloud files, domains, websites, cryptocurrencies, NFTs, IoT data, smart devices, and AI-generated content.
A future-ready digital legacy also includes personal messages, ethical wills, recorded stories, and AI memory preservation tools. This transforms digital legacy planning from technical administration into human continuity. ↓ Jump to 2026 Legacy: Expert FAQs & Troubleshooting.

Traditional estate planning focuses on legal transfer after death. Sovereign digital legacy planning focuses on control during life and beyond. Legal systems rely on platform cooperation and static documents, while sovereign systems emphasize autonomous access, living frameworks, and lifetime protection. The strongest strategy combines legal compliance with sovereignty-first digital infrastructure.
Designing legacy and sovereignty begins with proactive structure, not wealth or status.
Create a secure list of digital accounts, assets, access instructions, and recovery keys stored using encrypted methods.
A digital executor manages account closure or memorialization, asset transfers, and privacy enforcement. One of the most common mistakes in digital legacy planning is failing to designate clear authority, leading to lost access and disputes.
Digital legacy plans should integrate with wills, trusts, power of attorney, and digital estate documents to ensure compliance without sacrificing sovereignty.
Elite sovereignty is defined by total “Self-Custodial Autonomy,” where an individual manages their own private keys, RWA-backed credit lines, and encrypted communication layers. It is the luxury of operating entirely outside of legacy institutional bottlenecks while maintaining 100% On-Chain Compliance and global mobility.↓ Jump to 2026 Legacy: Expert FAQs & Troubleshooting.
Legacy is not purely technical — it is emotional and ethical. Digital afterlife planning raises questions around memory preservation, control of posthumous AI profiles, privacy boundaries, and emotional impact on loved ones. As autonomous digital identities emerge, sovereignty becomes the ethical guardrail that ensures consent, dignity, and psychological well-being are preserved.
In a globally mobile digital life, jurisdictional differences create complexity. Platform restrictions, forgotten credentials, privacy risks, and lack of awareness remain common challenges. These are mitigated through encrypted vaults, decentralized identity systems, portable credentials, and proactive planning that is not tied to geography or institutions.
Without sovereignty, governments, platforms, or intermediaries can freeze accounts, revoke access, or erase professional history. Sovereign digital systems reduce seizure risk by separating identity, assets, and reputation from centralized control.
Yes — even without financial assets, your photos, messages, accounts, identity, and data form a digital legacy. Digital ownership enables intergenerational continuity of knowledge, reputation, and value when governed properly.
By embracing Legacy and Sovereignty, you protect long-term income streams, preserve identity, and ensure your digital presence reflects your values beyond your lifetime. Digital legacy planning is no longer optional. Digital sovereignty is no longer theoretical. The future belongs to those who secure their digital life — beyond themselves.
The Institutional Transitioner (The “Ex-Banker”)
The Digital Dynasty Builder (The “High-Net-Worth Sovereign”)
In 2026, the greatest threat to your digital sovereignty is not a hack, but digital purgatory—a state where your assets exist but are unreachable by your loved ones. Without a proactive audit, your online life is essentially a “black hole”: information can go in, but it can never come out.
Use the following risk assessment to determine if your digital legacy is currently a “ticking time bomb.”
To move from “At-Risk” to “Sovereign,” builders and users are now adopting the 3-2-1 Legacy Rule:
| Pillar Segment | The Legacy Employee (2026) | The Sovereign Professional (2026) |
| Identity | Company-issued ID / Resume | Sovereign Wallet / ENS / DID |
| Income | Single source (Salary) | Multi-Protocol (Retainers + Yield) |
| Mobility | Tethered to office/city | Decoupled / Global Mobility |
| Security | Health insurance / Pension | Self-Custody / Smart Contract Will |
| Legacy | Ends at retirement | Persistent On-Chain Estate |
A smart contract will is a self-executing code protocol that automates the transfer of digital assets and access rights upon a verified “dead man’s switch” or external oracle trigger. Unlike traditional paper wills, it eliminates probate delays, ensuring assets like BTC or RWA tokens are instantly and trustlessly distributed to designated wallets.
A career that outlives you is not science fiction — it is a system where reputation, contributions, intellectual property, and income streams persist beyond individual participation. In Web3-native environments, on-chain records, DAOs, and programmable rights make continuity possible without reliance on employers.
Technology is redefining legacy planning by creating systems that resist failure rather than depend on trust. Blockchain enables immutable asset transfer, decentralized storage protects access and privacy, and cryptographic verification ensures continuity without intermediaries. Failure-resistant systems are essential to preserving sovereignty across time, platforms, and jurisdictions.
Security in digital life is no longer defined solely by income or employment stability. It is defined by optionality — the ability to exit failing systems, enter new ones, and preserve identity and capital throughout the transition. Sovereign infrastructure, portable reputation, and on-chain assets create this optionality. When systems fail, optionality is what allows individuals to survive without restarting from zero. In legacy planning, optionality is the mechanism that ensures continuity across decades, technologies, and geopolitical shifts.
On-chain succession utilizes multi-signature wallets and time-locked contracts to manage the transition of authority. If an owner remains inactive for a predetermined period, the contract automatically promotes secondary keys or beneficiaries to “Admin” status, maintaining the Secure Pillar of an estate without requiring centralized intermediaries. ↓ Jump to 2026 Legacy: Expert FAQs & Troubleshooting.
Yes, through the use of Soulbound Tokens (SBTs) and decentralized identifiers (DIDs), professional reputation and gated access can be legally tied to a family office or corporate entity. This allows an individual’s “Legacy Pillar”—including institutional credentials and governance rights—to remain functional and transferable to successors..
By 2030, expect AI-powered digital avatars, stronger post-mortem privacy rights, autonomous identity frameworks, and blockchain-based inheritance systems to become standard. Legacy and sovereignty will evolve from optional planning into a baseline digital responsibility.
AI-driven digital legacy solutions allow individuals to preserve identity, values, skills, and knowledge — not just assets. In career systems, AI agents may manage workflows, maintain professional presence, and extend productive output beyond the individual, while remaining governed by consent and sovereignty principles.
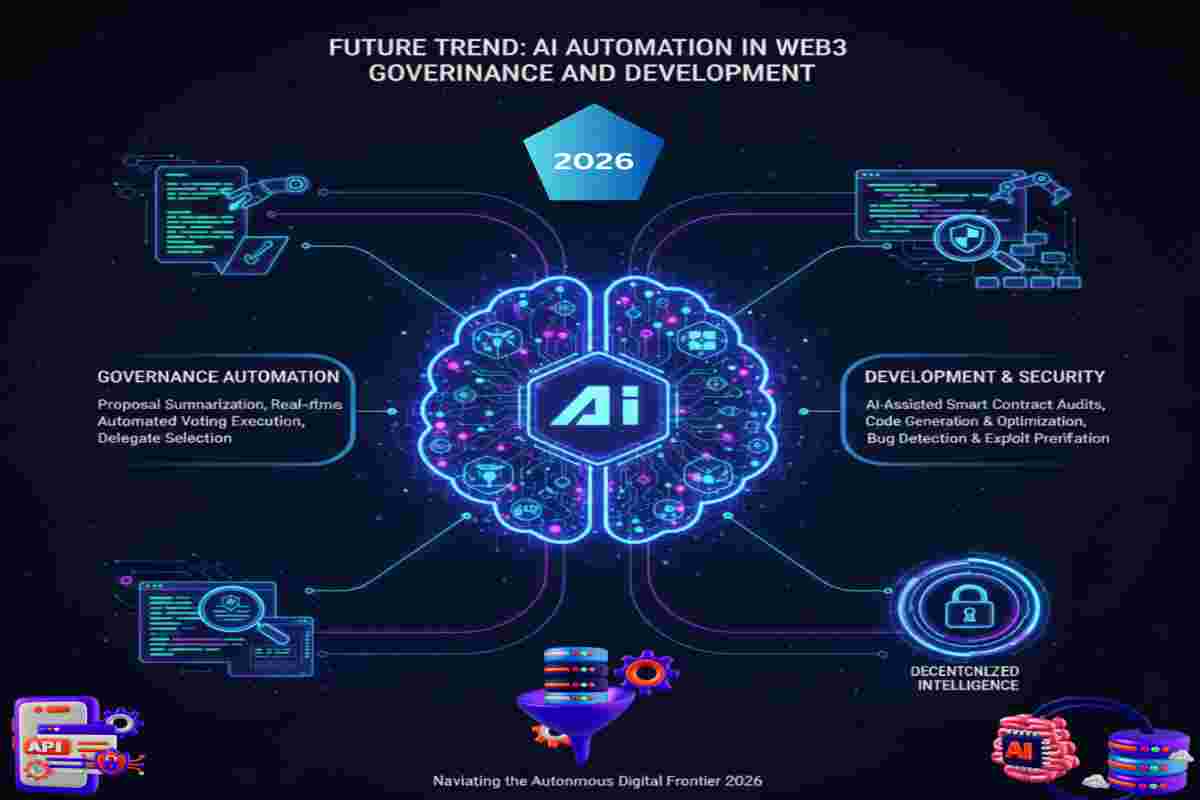
Human actors define strategy, governance rules, and risk parameters, while automated agents enforce those policies consistently across time, scale, and networks. In practice, AI-driven automation monitors on-chain activity, validates governance conditions, flags security anomalies, and executes pre-approved workflows such as transaction limits, treasury operations, or compliance checks. This design strengthens operational resilience, reduces human error, and ensures continuity without compromising self-custody or sovereign control. By separating decision-making from execution, Web3 systems achieve scalable automation while preserving decentralization, accountability, and long-term digital sovereignty.
This table helps readers mentally place AI correctly — not as magic, but as infrastructure.
| Layer | Human Role | AI-Automation Role | Sovereignty Impact |
|---|---|---|---|
| Strategy | Define goals, risk limits, governance rules | None | Fully human |
| Policy | Encode rules into smart contracts & workflows | Validate rule consistency | Human-controlled |
| Execution | Approve systems & escalation paths | Execute tasks automatically | Delegated, reversible |
| Monitoring | Decide what matters | Watch thresholds & anomalies | Prevents silent failure |
| Recovery | Authorize intervention | Trigger alerts & pauses | Human override preserved |
As digital lives become borderless, digital sovereignty is increasingly recognized as a global standard rather than a niche ideology. By integrating decentralized finance (DeFi) and non-custodial crypto assets, individuals are moving beyond mere data privacy to true “Financial Sovereignty,” where wealth is secured by mathematics rather than intermediaries. Individuals who secure their digital and financial sovereignty today position themselves ahead of the regulatory, technological, and societal shifts that are redefining the 2026 global economy.
A future-ready digital life is designed to persist beyond individual participation. Reputation, intellectual property, governance rights, and income streams can be structured to continue operating through smart contracts, DAOs, and AI agents. These systems do not replace human agency or consciousness; they extend impact, preserve intent, and maintain continuity. Designing systems that outlive the individual transforms legacy from a static handoff into a living, sovereign framework that evolves across generations. ↓ Jump to 2026 Legacy: Expert FAQs & Troubleshooting.
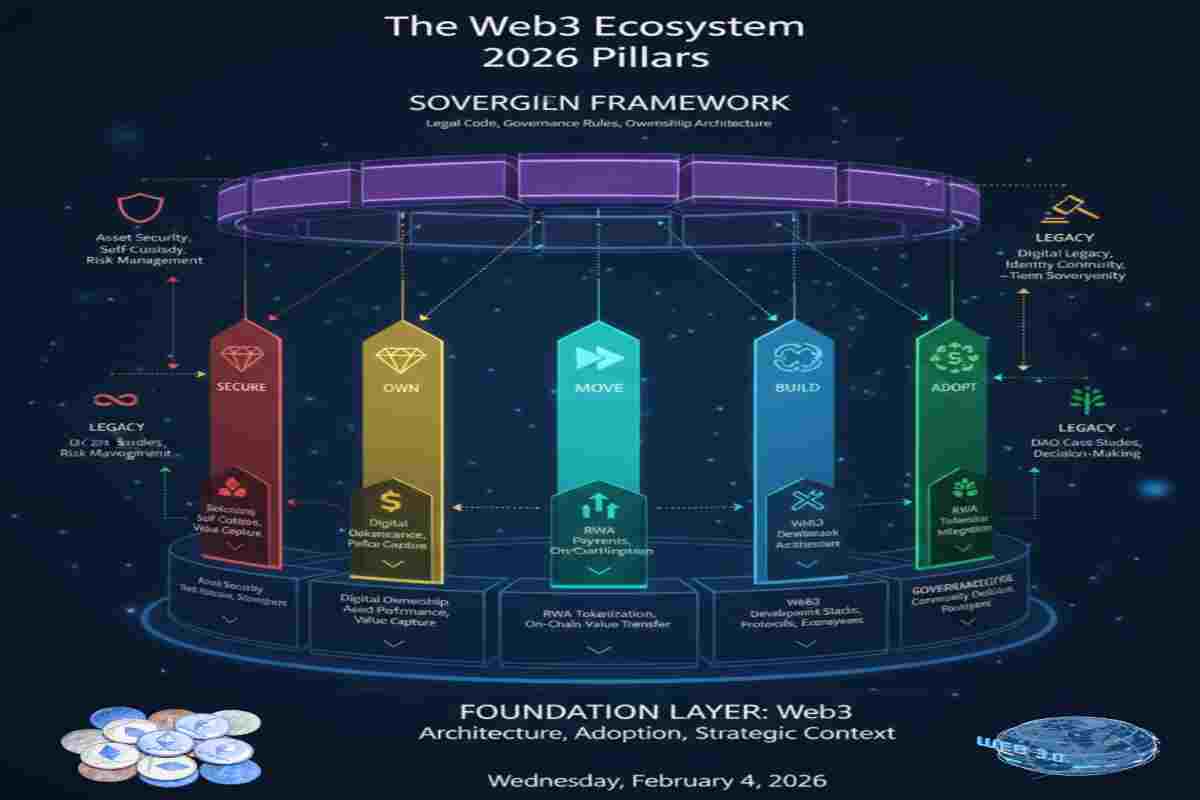
As part of the LEGACY pillar, this guide explores digital identity continuity, inheritance planning, and long-term sovereign asset preservation.
Explore related pillars:
Each pillar functions independently while forming a complete sovereign Web3 lifecycle model.
To secure your legacy and master the 2026 market shifts, you need more than just theory—you need execution. I have developed the complete Digital Sovereignty Tool & Pillar Template Set, designed specifically for institutional-grade asset management and on-chain succession planning. This toolkit includes the RWA S-Curve Projection Model, the Smart Contract Will Framework, and the Capital Efficiency Audit.
Purpose: Evaluate Legacy. For a completed Legacy Map Templates with Individual Sheet ready in Excel or Google Sheet worth $499 for free today join our Facebook Group https://www.facebook.com/groups/2430833834044955
To help you navigate the complexities of decentralized decision-making in 2026, we have organized the most critical inquiries into thematic groups. This structure ensures you can quickly find expert insights rooted in real-world successes and historical failures.
Your digital life is part of who you are — and who you will be remembered as.
By embracing Legacy & Sovereignty, you take control of your digital assets, protect your identity, and ensure your online presence reflects your values beyond your lifetime.
Digital legacy planning is no longer optional.
Digital sovereignty is no longer theoretical.
The future belongs to those who secure their digital life — beyond themselves.
Key Takeaways and Next Steps:
Next steps to act on immediately:
The future of work does not belong to companies or platforms. It belongs to those who design for sovereignty early. Legacy is no longer something you leave behind. It is something you build into your career from the start.
As we navigate the fiscal landscape of 2026, the mandate for institutional-grade stability has shifted from a “best practice” to a non-negotiable regulatory baseline. Central to this transition is the emphasis on high-quality liquid assets (HQLA) and rigorous risk management frameworks, as outlined in the U.S. Treasury TBAC Q4 2024 report. Whether managing traditional corporate treasuries or emerging digital value chains, the harmonization of global standards—such as MiCA in Europe and the Pillar 2 requirements—ensures that financial systems remain resilient against liquidity shocks. For the modern enterprise, maintaining this “compliance-first” posture is the only viable path to achieving long-term capital efficiency and safeguarding stakeholder trust in a borderless economy. .EU MiCA Summary

Welcome to OwnProCrypto (Own & Pro Crypto) — a next-generation Bitcoin and blockchain education platform where the science of finance meets the power of AI-driven automation.
Our mission is simple: to equip you with the knowledge, frameworks, and tools needed to make smarter financial and business decisions in the Web3 economy.
Beyond analysis, OwnProCrypto focuses on transparency, verifiable data, and practical frameworks that investors and builders can actually use. Our goal is not hype — but clear thinking, disciplined analysis, and long-term value creation in the decentralized economy.
Our Background
As part of the Web3 Ecosystem Architecture pillar, this guide focuses on Sovereign Ownership Architecture in Web3. Explore related pillars: