

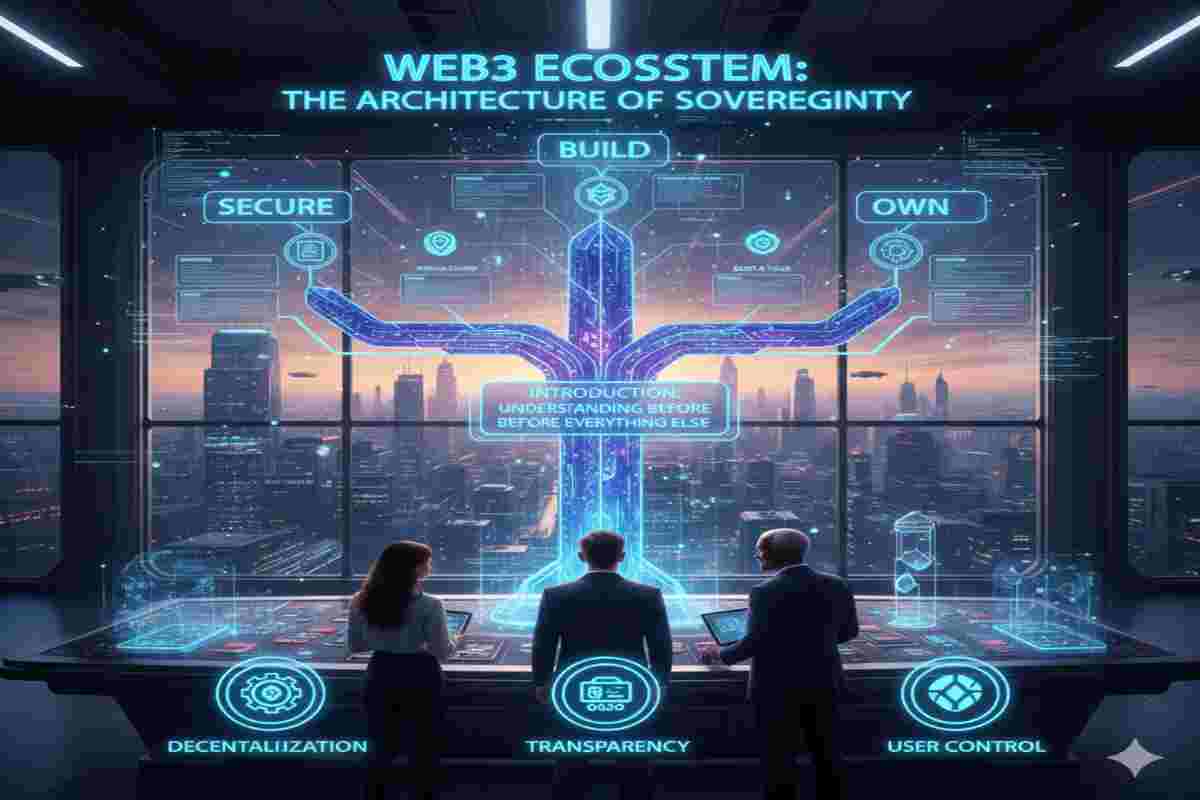
Problem → Shift → Solution → Framework → Outcome → Risks → Signals → Conclusion.
Table of Contents
ToggleFrom Fragile Private Keys to Institutional-Grade Account Abstraction.
In 2026, asset security has transitioned from “Protecting a Key” to “Governing a System.” As institutional adoption scales, the reliance on single-signature EOAs has been replaced by Account Abstraction (AA)—a framework that turns wallets into smart contract vaults. This shift eliminates the “single point of failure” inherent in seed phrases and allows for the implementation of complex, automated security policies directly on-chain.
The 2026 Security Standards:
Asset Security in 2026 addresses a critical structural problem: digital assets are scaling into multi-trillion-dollar systems, yet the security models protecting them remain fragmented, reactive, and fundamentally misaligned with a programmable, interconnected economy—where a single permission flaw or authorization failure can compromise entire treasuries in minutes. As value becomes more fluid, automated, and cross-chain, the industry is undergoing a decisive shift from static, key-based custody toward dynamic, policy-driven security—where control is not just protected, but continuously enforced. In response, Asset Security evolves into a proactive solution layer, leveraging account abstraction, smart accounts, and programmable authorization to eliminate single points of failure and reduce reliance on fragile key management. This is operationalized through a unified security framework that integrates ERC-4337 smart accounts, granular permission controls, multi-layer authorization logic, and privacy-preserving mechanisms such as zero-knowledge proofs into a cohesive system of defense. The outcome is engineered resilience at scale—where digital assets, tokenized real-world assets, and on-chain yield systems remain secure, adaptable, and verifiably controlled across chains, jurisdictions, and evolving threat landscapes.
In a programmable economy, resilience isn’t added later—it must be architected from the start.
By 2026, tokenized assets, autonomous treasuries, digital collateral rails, and automated settlement networks are expected to move multi-trillion-dollar value flows across chains and jurisdictions. Static custody models cannot withstand that velocity. The expanding attack surface—credential replay, session hijacking, authority misuse, integration exploits—has shifted risk from brute-force compromise to authorization failure.
Asset Security 2026 represents a structural transition: from key-based wallets to policy-enforced smart accounts; from passive storage to active infrastructure.
Simultaneously, economic design is evolving toward privacy-preserving tokenomics—where confidential token balances and shielded asset transfers coexist with compliance. Zero-knowledge ownership proofs enable verifiable control without identity exposure, and zk-based governance frameworks allow collective decision-making without sacrificing discretion. Privacy and authorization are converging into programmable trust layers.
In this environment, asset security is no longer defined by how well secrets are hidden. It is defined by how intelligently authority is constrained, how dynamically permissions adapt, and how seamlessly privacy integrates with control.
The future will not reward reactive protection. It will demand engineered resilience.
An evolving stack of blockchain networks, decentralized protocols, digital assets security 2026, and smart contracts, promises a more user-centric internet built on verifiable ownership and peer-to-peer exchange. But that promise comes with friction. Decentralized technology may ignore borders; the law does not.
For organizations evaluating Web3 business models in 2026, whether launching an NFT collection, building a blockchain game, operating a decentralized social platform, or participating in a DAO, regulation is active, jurisdiction-specific, and increasingly enforced. Business executives may assume decentralization itself offers legal insulation. It doesn’t. Consumer protection, financial transparency, criminal enforcement, tax compliance, cybersecurity obligations, and intellectual property rights all apply, often in unfamiliar ways. Projects that fail to account for this reality early risk regulatory action, uninsurable losses, and structural flaws that are difficult or impossible to unwind later.

In 2026, the promise of the sovereign internet is only as strong as your ability to protect your holdings. This makes Asset Security 2026 the single most important skill for any serious participant. Many investors are still haunted by the “seed phrase era,” where a lost piece of paper meant the total loss of a life’s work. The “good news” is that we have moved beyond simple storage to a world of comprehensive Asset Protection and Wealth Security.
The global financial system is undergoing a structural shift as individuals and institutions move from delegated custody toward sovereign asset protection. Traditional security models—reliant on centralized custodians, single private keys, or static hardware wallets—are increasingly misaligned with the realities of on-chain finance. As digital assets become programmable, composable, and globally transferable, security must evolve from a single point of control into a policy-driven, resilient architecture. This shift reflects institutional thinking: assets are no longer merely stored, but actively governed through rules, permissions, and real-time risk controls embedded directly on-chain.
By 2026, this transformation has accelerated under the pressure of sophisticated phishing attacks, automated drainers, and cross-chain exploits. Account abstraction and smart contract wallets have emerged as the foundation of this new security paradigm, enabling features such as transaction velocity limits, conditional approvals, and programmable recovery. Rather than trusting a single secret, sovereign asset protection distributes authority across code, cryptography, and human safeguards—mirroring how institutions manage capital at scale. The result is a security model that is not only harder to breach, but also adaptable, recoverable, and aligned with the operational demands of modern digital finance. ↑ Back to FAQs Menu
For institutions, the return on investment from modern custody architecture is measurable and strategic.
Primary value drivers in 2026 include:
| ROI Driver | Institutional Impact | Strategic Outcome |
|---|---|---|
| Security Event Avoidance | Reduction in catastrophic loss probability | Capital preservation |
| Policy Automation | Reduced manual approval overhead | Operational scalability |
| Embedded Audit Trails | Faster audit cycles | Lower compliance cost |
| Transaction Bundling Efficiency | Lower gas expenditure at scale | Improved treasury margins |
The implication is clear: asset security is no longer a tooling choice. It is an architectural commitment that determines whether institutions can scale digital asset operations without proportionally increasing risk, headcount, or regulatory exposure. ↑ Back to FAQs Menu
Digital custody in its early phase was dominated by a single concern: private key theft. That risk has not disappeared, but it is no longer the dominant failure mode.
Author Bio: Drawing from my 9 years of institutional blockchain research in Dallas and an MBA from the University of Karachi, I have analyzed thousands of on-chain failures to bring you a unique solution. The “good news” is that Account Abstraction has finally arrived. It offers a “Digital Fortress” that replaces the anxiety of private keys with the familiarity of biometric recovery and On-Chain Compliance.
Understanding the geographic risks of the old system is only the first step. To move from vulnerability to a true Sovereign Mandate, we must look at how technology now replaces human error. Before we dive into the specific tools of Asset Safeguarding, it is vital to understand why the 12-word seed phrase is now considered an obsolete security risk. This shift is what allows for the high-level Wealth Security and Capital Defense we see in the next section regarding Smart Contract Vaults.
Modern institutional breaches increasingly occur without breaking cryptography. Instead, attackers exploit valid credentials operating within overly permissive boundaries. The system does exactly what it was technically allowed to do.
This is a profound shift.
Security failures now emerge from authorization misuse rather than encryption failure. ↑ Back to FAQs Menu
Institutional threat models in 2026 prioritize systemic and contextual risks rather than isolated key exposure.
Major risk categories include:
| Threat Vector | Description | Why Legacy Custody Fails |
|---|---|---|
| AI-Enhanced Social Engineering | Deepfake approvals, contextual phishing | Human signers remain ultimate authority |
| Session Replay and Abuse | Misuse of scoped credentials | Lack of execution-layer limits |
| Smart Contract Logic Exploits | Policy misconfiguration | Off-chain governance gaps |
| Protocol Dependency Cascades | Downstream composability failures | No containment logic in wallet |
These threats operate within valid execution pathways. That is what makes them dangerous. ↑ Back to FAQs Menu
Artificial intelligence has transformed social engineering into a precision instrument. Deepfake voice approvals, real-time conversational phishing, and contextual impersonation are no longer edge cases. Attackers exploit operational urgency, especially in treasury environments where capital must move quickly.
When authorization is tied primarily to human approval, speed becomes vulnerability.
Session keys and temporary credentials improve efficiency but introduce risk when improperly scoped. If boundaries are too broad, a compromised session can move meaningful value before detection. The difference between survivable compromise and catastrophic loss often lies in the granularity of session permissions.
Security now depends heavily on correct logic implementation. A single flawed boundary condition or unchecked fallback can create unintended authorization paths. These are engineering failures, not cryptographic ones. ↑ Back to FAQs Menu
Institutional Asset Security strategy in 2026 does not assume perfect prevention. It assumes eventual compromise and designs systems to limit damage.
Key performance indicators now include:
• Mean Time to Containment
• Maximum Transfer Limit per Session
• Automated Policy Enforcement Rate
• Permission Revocation Latency
• Blast Radius Quantification
The objective is not zero breach. It is bounded breach. ↑ Back to FAQs Menu
Account Abstraction enables containment mechanisms that traditional externally owned accounts cannot support.
If anomaly thresholds are triggered:
• Signing authority can rotate without asset migration
• Account execution can pause or rate-limit
• Session permissions can downgrade automatically
• Guardian escalation flows can activate
The wallet becomes an adaptive control plane rather than a static endpoint.
In 2026, institutional asset security shifted from key protection to programmable authorization control as attack vectors evolved beyond simple compromise.
The shift toward Asset Security 2026 isn’t just a technical upgrade; it is a fundamental change in how we define ownership. In the old model, your security was a secret (your seed phrase). If the secret was stolen, the assets were gone. In the Sovereign Ownership Framework, your security is a set of rules. By moving to Account Abstraction, you are turning your wallet into a ‘Smart Account’ that can verify your identity through biometrics and enforce your own custom financial laws.

The transition from externally owned accounts to programmable smart accounts represents the most significant structural upgrade in blockchain security.
In the legacy Web3 world, we used EOAs. These were “dumb” addresses where one mistake meant total loss. In 2026, we have moved toward the Smart Contract Wallet model. These aren’t just addresses; they are programmable vaults that allow for Biometric Guardians and Spending Limits, ensuring your RWA Tokenization portfolio remains untouchable even if a single device is lost.
The 2026 Security Framework includes:
Asset Security 2026 is now defined by Smart Contract Wallets. These aren’t just addresses; they are programmable vaults:
Technical features provide the framework, but real-world scenarios prove why a human safety net is required to prevent total loss.

Institutional asset managers have long relied on redundancy. Today’s technology brings those same “Family Office” protections to the individual retail investor.
The next generation of wallets includes on-chain compliance engines. These automatically block interactions with high-risk or blacklisted contracts, stopping phishing exploits and “drainers” long before you ever sign a transaction.
When I conducted due diligence for family offices in Dallas, we looked for redundancy. Your personal strategy should be no different. By leveraging On-Chain Compliance tools, your wallet can now automatically block “blacklisted” malicious contracts before you even interact with them.
This creates a high-performance environment for Real Yield farming. You can deploy capital with the confidence that your “Execution Layer” is protected by multiple signatures and time-locks.
Traditional externally owned accounts combine identity, authorization, and execution into a single primitive: the private key. Whoever controls the key controls the funds. There is no native way to encode context, intent validation, or layered permissions.
Account Abstraction separates these components.
Instead of broadcasting raw signatures, institutions submit structured user operations. These operations are evaluated against programmable logic before execution. Authorization becomes a function of policy rather than possession.
This is the structural security upgrade.
The system no longer asks:
Does this signature match the key?
It asks:
Does this action satisfy institutional policy?
That shift from knowledge-based validation to logic-based validation is the core innovation of Account Abstraction. ↑ Back to FAQs Menu
Under frameworks such as ERC-4337, transaction execution follows a defined validation pipeline:
This layered validation enables:
• Role-based authorization
• Spending limits
• Time delays
• Counterparty allowlists
• Session-bound permissions
• On-chain compliance screening
Institutions gain programmable control at the account layer itself. ↑ Back to FAQs Menu
Account Abstraction does not rely on a single cryptographic breakthrough. It orchestrates multiple primitives into a layered trust model.
Signing authority is distributed across multiple parties or devices. No single compromise can authorize a transaction.
Institutional benefit: elimination of single point of failure risk.
MPC enables distributed key generation and signing without reconstructing the full private key in one location.
Institutional benefit: secure off-chain key custody with reduced exposure surface.
Zero-knowledge systems enable verification of attributes or permissions without revealing underlying sensitive data.
Institutional benefit: privacy-preserving compliance checks.
Unlike externally owned accounts, AA smart accounts can upgrade their verification logic. This allows migration to new cryptographic standards without moving assets.
This becomes critical in post-quantum transition planning.
Ensure cryptographic primitives are layered and independently auditable. Account Abstraction does not eliminate risk, but it enforces policy at execution, reducing dependency on a single failure point.
Account Abstraction does not eliminate existing custody models. It orchestrates them.
| Component | Role in 2026 Architecture | Limitation Without AA |
|---|---|---|
| EOA | Lightweight operations | Binary authorization |
| Multisig | Explicit human approval | Operational friction |
| MPC | Secure key management | Off-chain only enforcement |
| AA Smart Account | Policy enforcement layer | Requires disciplined engineering |
AA becomes the execution governor that integrates these components into a cohesive system. ↑ Back to FAQs Menu
Retail custody models depend heavily on mnemonic seed phrases. These introduce:
• Single recovery dependency
• Physical storage risks
• Social engineering exposure
• Operational bottlenecks
Institutional AA deployments replace mnemonic recovery with structured guardian models.
Recovery flows may involve:
• Designated corporate entities
• Hardware security modules
• MPC quorum
• Time-locked activation logic
The result is controlled, auditable recovery rather than personal secret storage.
Institutional adoption of Account Abstraction must be measurable, auditable, and board-visible.
While AA improves systemic security, it introduces its own risk domains.
Primary risk categories include:
| Risk Type | Description | Mitigation Strategy |
|---|---|---|
| Logic Risk | Flawed rule implementation | Formal verification & audits |
| Paymaster Risk | Gas sponsorship abuse | Treasury caps & monitoring |
| Bundler Dependency | Service reliability risk | Redundant infrastructure |
| Upgrade Risk | Governance capture | Multi-layer approval controls |
Engineering discipline becomes mandatory. Programmability increases power and responsibility simultaneously. ↑ Back to FAQs Menu
AA accounts interact with:
• Yield protocols
• Liquidity pools
• Bridges
• Oracles
• Cross-chain relayers
Each integration adds inherited risk.
Institutions respond through composability stress simulations:
• Downstream contract failure
• Oracle manipulation scenarios
• Liquidity shock modeling
• Gas spike conditions
The objective is predictable behavior under adverse conditions. ↑ Back to FAQs Menu
Institutional security in 2026 is defined not just by prevention, but by automated response logic embedded at the execution layer.
• Session anomaly detected such as unusual IP behavior or unexpected contract interaction
• Immediate rate limiting reduces transaction velocity and value thresholds
• Transaction enters a Pending Review state enforced at the smart account level
• Security operations team alerted via off-chain monitoring hooks
• Immutable forensic log updated with anomaly metadata and response actions
This architecture transforms wallets from passive key containers into active policy enforcement systems.
• Guardian hierarchy activated under predefined recovery conditions
• Off-chain identity verification conducted through secure out-of-band channels
• MPC threshold signing authorized once quorum requirements are met
• Keys rotated or reassigned to a newly validated signer configuration
Recovery is not an afterthought. It is engineered into the account logic itself.
Leading institutions simulate:
• Partial signer compromise
• Session key abuse
• Bundler outage
• Mempool congestion
• Upgrade execution failure
Evaluation criteria include:
• Maximum transferable value before containment
• Recovery activation latency
• Policy override integrity
• Transaction backlog resilience
The advantage of AA is reversibility of logic. While transactions remain immutable, the account’s future behavior can adapt. ↑ Back to FAQs Menu
The greatest barrier to Capital Efficiency has always been the risk of human error. In 2026, we have moved beyond the “Externally Owned Account” (EOA) model—the traditional wallet that forced you to act as your own bank without any safety nets.
The “good news” for the Web3 Ecosystem 2026 is that the era of losing everything because of a misplaced seed phrase is officially over. For years, the biggest pain point in the Decentralized Digital Economy was the “single point of failure” inherent in traditional wallets. Today, we offer a unique solution: a Sovereign Ownership Framework built on programmable “Smart Accounts.” By integrating Account Abstraction, we are moving beyond simple storage to a world of comprehensive Asset Security the Protection and Wealth Security. This post—Asset Security 2026: Setting Up Your Digital Fortress with Account Abstraction—will show you how to implement Institutional Security and Asset Safeguarding at a personal level. Whether you are looking for Capital Defense, Property Protection, or a total Resource Security overhaul, this guide is your blueprint for the Next-Generation Web Ecosystem ↑ Back to FAQs Menu
ROI Drivers for Account Abstraction
Institutional adoption of Account Abstraction must be measurable, auditable, board-visible, performance indicators to justify security architecture upgrades and demonstrate operational resilience.
| Metric | Traditional Custody | AA-Enabled Custody | Benefit |
|---|---|---|---|
| Security Event Cost | Reactive, post-loss | Preventive, policy-driven | High |
| Approval Efficiency | Manual, multi-level | Automated, on-chain | Medium-High |
| Audit Readiness | Periodic reports | Real-time logs | High |
Modern institutional custody relies on programmable vault logic that enforces policy at the execution layer rather than at the perimeter.
Dynamic policy engines restrict transaction size, frequency, and counterparties in real time, reducing exposure without halting operations.
Distributed guardian systems replace single-key recovery with quorum-based institutional restoration mechanisms.
Social recovery eliminates the greatest single point of failure in Web3: the forgotten seed phrase. By structuring a recovery network with multiple trusted backstops, users gain a safety net that previously existed only in custodial bank systems. ↑ Back to FAQs Menu
Resilient custody architecture eliminates unilateral control paths and designs recovery with layered redundancy.
Social Recovery and Guardian Networks create a human safety net that eliminates the most dangerous single point of failure in Web3—the lost or compromised seed phrase. By distributing recovery authority across multiple trusted guardians, users achieve secure self-custody with resilience previously found only in custodial banking systems.
This model strengthens digital asset security, account abstraction, and sovereign ownership without sacrificing user control or autonomy.
Modern smart accounts integrate hardware-backed authentication and passkey standards to reduce human key management risk.
By integrating FaceID and fingerprint standards, account abstraction enables you to authenticate securely without memorizing secrets. This reduces friction and ensures that only you can authorize high-value movements of your Real Yield assets
The evolution from EOAs to smart contract wallets transforms security from passive key management into active, programmable protection. These vaults can restrict actions based on risk scores, daily spend caps, and contextual credentials—automating security policies that used to require third-party bankers.
While these programmable features offer a unique layer of Asset Integrity and Institutional Security, theory is only half the battle. To see how these Protected Assets actually behave during a crisis, you can review our side-by-side analysis of a $1.2M breach versus a successful recovery. This comparison highlights why Investment Protection in 2026 depends entirely on your ability to automate Asset Risk Management before a hacker strikes.
Technical features provide the framework, but real-world scenarios prove why a human safety net is required to prevent total loss ↑ Back to FAQs Menu
Smart accounts can embed automated anomaly detection and enforce compliance checks before transaction execution.
n the landscape of Asset Security 2026, the mandate for institutional digital assets has shifted from periodic audits to continuous, real-time enforcement. Automated threat detection now leverages Agentic AI and Blockchain Analytics to move beyond simple blocklists, analyzing the “intent” of a transaction before it is broadcast to the network. These systems integrate on-chain policy engines directly into the account logic, allowing a treasury to automatically pause a payout if it detects a “pig butchering” scam pattern or a connection to a high-risk mixer. This On-Chain Compliance ensures that KYC/AML/CFT and sanctions screening are no longer external hurdles but embedded prerequisites, creating a “Clean Execution Environment” where only compliant, verified value can move through the institutional fortress. ↑ Back to FAQs Menu
Zero-knowledge systems enable selective disclosure, balancing regulatory transparency with cryptographic privacy guarantees.
In the legacy Web3 era, privacy was often seen as an “all or nothing” choice—you were either fully transparent or hiding in the shadows. Zero-Knowledge Proofs (ZKPs) have shattered this false dilemma by introducing a way to prove the validity of a transaction without revealing the underlying data. This is the cornerstone of On-Chain Compliance in 2026. For example, a ZK-enabled smart wallet can prove to a regulator that you are a “verified, non-sanctioned user” without ever disclosing your name, address, or total Secure Holdings. By separating verification from visibility, ZKPs allow you to participate in the global Web3 Network Economy with total Asset Integrity, ensuring that your sensitive financial moves remain private while your actions remain legally ↑ Back to FAQs Menu verifiable.
Layered programmable controls transform wallets from passive storage mechanisms into active defensive systems.
Asset-Security Advanced Fortress Controls in 2026 represent the move from reactive patching to impenetrable, logic-based perimeters. These controls neutralize threats by assuming that the network perimeter is already breached, shifting focus to context-aware execution hurdles. By integrating Zero Trust Architecture (ZTA) directly into the account layer, every transaction is treated as a potential exploit until it clears a gauntlet of “Fortress” checks: hardware-backed biometric verification, real-time AI behavioral analysis, and protocol-level micro-segmentation. This effectively neutralizes the most sophisticated 2026 threats—such as AI-synthesized social engineering and session hijacking—by ensuring that even a “valid” signature cannot move assets if it deviates from the institution’s immutable security baseline.
Zero Trust assumes no implicit trust. Every request must be validated independently.
AA enforces this model natively:
• Each transaction is validated in isolation
• Identity is contextual, not permanent
• Permissions are scoped and revocable
• Execution requires policy compliance
This mirrors enterprise IAM philosophy, but enforcement occurs at the blockchain execution layer. ↑ Back to FAQs Menu

Session keys are foundational to institutional AA deployments.
They allow narrowly scoped operational authority such as:
• Trade execution within defined slippage range
• Liquidity rebalancing within capped limits
• Interaction with pre-approved smart contracts
Key characteristics:
| Attribute | Security Benefit |
|---|---|
| Time-bound validity | Automatic expiration |
| Value limits | Contained financial exposure |
| Contract allowlist | Reduced composability risk |
| Instant revocation | Rapid breach containment |
This architecture enables operational velocity without surrendering control. ↑ Back to FAQs Menu
AA accounts produce structured, immutable logs including:
• Authorization path
• Signer set
• Session metadata
• Policy version
• Execution context
This provides:
• Deterministic audit trails
• Legal defensibility
• Post-incident clarity
• Board-level transparency
The account becomes a cryptographic evidence system. ↑ Back to FAQs Menu
Security in 2026 is achieved through layered orchestration.
| Layer | Function |
|---|---|
| MPC | Distributed key material management |
| HSM | Tamper-resistant signing |
| Smart Account | On-chain policy enforcement |
| Monitoring Stack | Behavioral anomaly detection |
Failure in one layer does not automatically cascade across the system.
This separation of concerns defines resilient custody. ↑ Back to FAQs Menu
Institutional recovery models avoid reliance on mnemonic phrases.
Guardian frameworks may include:
• Executive quorum
• Independent custody partner
• Automated time-locked vault
• Regulatory oversight node
Recovery activation requires defined thresholds and structured validation.
This ensures business continuity without introducing new single points of failure.
Recovery architecture must include multi-layer guardian logic and automated triggers. Institutional resilience depends as much on recovery engineering as on prevention.
Disaster recovery planning includes:
• Dead-man switches
• Secondary recovery vaults
• Geographic signer distribution
• Automated inactivity triggers
Key lifecycle stages:
AA enables lifecycle transitions without asset migration, reducing operational risk during upgrades.
Modern institutional key management has moved beyond the “single point of failure” inherent in traditional cold storage. By utilizing a hybrid of MPC (Multi-Party Computation) and programmable smart contracts, organizations can now distribute signing authority across geographical and hardware boundaries, ensuring that no single executive or device can compromise the entire treasury.

In 2026, regulators no longer ask whether digital asset security and asset controls exist. They ask whether those controls are enforceable, consistent, and auditable.
Account Abstraction changes the compliance model by embedding governance into transaction validation itself.
Instead of relying solely on:
• Internal approval workflows
• After-the-fact reporting
• Periodic reconciliation
AA systems can enforce:
• Sanctions screening pre-execution
• Counterparty allowlists
• Jurisdictional policy rules
• Value thresholds by risk tier
• Automated escalation logic
Compliance becomes a prerequisite for execution rather than a documentation layer applied afterward.
This structural shift reduces regulatory friction while improving operational clarity. ↑ Back to FAQs Menu
Institutional deployments increasingly map AA architectures to established frameworks such as:
• NIST SP 800-53
• ISO 27001
• SOC 2
• MiCA governance requirements
The mapping is straightforward because AA enforces:
Because permissions are encoded and machine-readable, institutions can demonstrate control deterministically rather than narratively.
In 2026, enterprise digital asset security is no longer just about preventing theft; it is about policy enforcement at the protocol level. This framework allows corporations to encode their internal bylaws directly into the blockchain, ensuring that every transaction automatically adheres to zero-trust architecture and real-time audit requirements before it is even broadcast to the network. ↑ Back to FAQs Menu
AA produces structured authorization metadata alongside execution.
Each transaction contains:
• Who approved
• Under what policy
• Which signer set
• Which session context
• Which policy version
This enables cryptographic proof of intent and compliance.
For legal teams, this reduces ambiguity.
For auditors, it reduces reconstruction cost.
For boards, it provides defensible governance evidence.
The account becomes a verifiable control plane. ↑ Back to FAQs Menu
The first ROI driver is avoided catastrophic loss.
Between 2020 and 2025, digital asset breaches exceeded billions annually across centralized and decentralized systems. By 2026, institutional risk tolerance for irreversible loss has dropped sharply.
AA reduces risk through:
• Spending limits
• Rate limits
• Context validation
• Session scoping
• Rapid key rotation
Even if compromise occurs, blast radius is controlled.
The cost of prevention becomes materially lower than the cost of breach remediation. ↑ Back to FAQs Menu
Manual multi-signature processes introduce friction:
• Delayed settlements
• Weekend liquidity bottlenecks
• High personnel overhead
• Human approval fatigue
AA automates policy enforcement.
Routine transactions proceed automatically within defined constraints.
Exceptions escalate.
This allows 24/7 treasury operations without proportional headcount growth. ↑ Back to FAQs Menu
Representative institutional metrics observed in mature deployments:
| KPI | Pre-AA | Post-AA |
|---|---|---|
| Manual approval ratio | 80 percent | Under 25 percent |
| Settlement latency | Hours | Minutes |
| Incident containment time | Days | Under 1 hour |
| Audit preparation time | Weeks | Days |
Efficiency compounds as transaction volume increases.
AA enables programmable treasury use cases including:
• Automated vendor disbursements
• On-chain payroll
• Collateral rebalancing
• Yield strategy execution
• Cross-chain liquidity routing
Each workflow is governed by encoded policy.
Funds move continuously but never freely.
This balance between automation and constraint defines institutional-grade blockchain operations. ↑ Back to FAQs Menu
Institutional AA risk modeling focuses on quantifiable variables:
• Maximum exposure per transaction
• Daily value caps
• Composability exposure ratio
• Bundler uptime dependency
• Paymaster liquidity buffer
These inputs translate into enforceable parameters.
Risk becomes measurable and programmable.
Governance moves from documentation to execution logic.
Measure Account Abstraction adoption using operational KPIs tied to board-level reporting. Visibility and quantification convert security architecture into strategic control.
AI-Agent-Risk By 2026, the primary “users” of institutional wallets are no longer humans, but Autonomous AI Agents. These agents manage on-chain liquidity, execute MEV-aware arbitrage, and rebalance tokenized treasuries at machine speed. This shifts the Asset Security 2026 requirement from human-centric multi-sig to Machine-Centric Security. Account Abstraction (AA) is the only architecture capable of securing this “Machine Economy.” By using AA, institutions can issue scoped permissions to an AI agent—allowing it to trade within specific price slippage parameters or move funds between pre-approved vaults—without ever giving the agent control over the underlying root keys.
AA-Security-Innovation If an agent’s logic is manipulated (via Prompt Injection or Model Poisoning), AA guardrails prevent the agent from executing unauthorized “drain” transactions. This model treats AI agents as distinct on-chain identities with their own lifecycle. In 2026, a rogue agent is neutralized not by hunting for a leaked password, but by the account logic itself, which recognizes a deviation from the agent’s pre-defined intent-based boundaries. This ensures that autonomous operations can scale at machine velocity without a corresponding increase in catastrophic risk.
By 2026, institutional wallets increasingly interact with autonomous AI systems managing:
• Arbitrage
• Liquidity provisioning
• Portfolio rebalancing
• Market-making
• Cross-chain routing
These agents operate at machine speed.
Traditional multi-sig architectures designed for human coordination cannot scale to machine-native finance.
AA enables scoped machine permissions.
Institutions can allow an AI agent to:
• Trade within defined slippage bounds
• Rebalance only between approved vaults
• Execute only on specific contracts
• Operate within capped daily exposure
The AI never holds root authority.
If model poisoning or prompt injection occurs, AA guardrails prevent catastrophic drain events.
This makes AA foundational for machine economy security. ↑ Back to FAQs Menu
The quantum threat model assumes adversaries may record encrypted transaction data today for future decryption.
Externally owned accounts using traditional ECDSA signatures face long-term vulnerability if quantum breakthroughs materialize.
AA smart accounts provide cryptographic agility.
Because verification logic is contract-based:
• Signature schemes can be upgraded
• New algorithms can replace old ones
• Assets remain at the same address
• Migration risk is minimized
Institutions can transition to post-quantum algorithms such as lattice-based signatures without asset relocation.
This reduces one of the most overlooked risks in blockchain security: migration exposure. ↑ Back to FAQs Menu
Legacy models rely heavily on hardware-only isolation.
Future-ready institutions orchestrate:
• MPC for distributed trust
• HSMs for physical assurance
• Smart accounts for execution governance
• Monitoring systems for behavioral detection
Layered coordination replaces single-control dependency. ↑ Back to FAQs Menu
Policy PDFs do not enforce execution.
On-chain logic does.
Institutions must transition from manual four-eyes controls to encoded rule sets that:
• Cannot be bypassed
• Cannot be retroactively altered
• Execute deterministically
This is the difference between procedural governance and programmable governance.
No system is invulnerable.
Resilience depends on:
• Rapid key rotation
• Session revocation
• Account pausing
• Policy upgrades
• Automated anomaly triggers
AA supports controlled degradation rather than catastrophic collapse. ↑ Back to FAQs Menu
Different institutions face distinct threat models, requiring tailored custody and authorization architectures.
Any institution or high-value participant operating on-chain requires a Digital Fortress architecture. This includes enterprise treasuries managing stablecoin flows, DAOs controlling governance capital, crypto-native funds deploying multi-chain strategies, custodians safeguarding client assets, and high-net-worth individuals holding significant digital exposure. As transaction complexity and attack surfaces expand in 2026, traditional wallet security is no longer sufficient. A programmable, policy-enforced security model is essential for anyone whose digital assets represent operational continuity, fiduciary responsibility, or generational wealth.
While individual successes show the potential of Account Abstraction, you likely have specific questions about how this applies to your own portfolio.
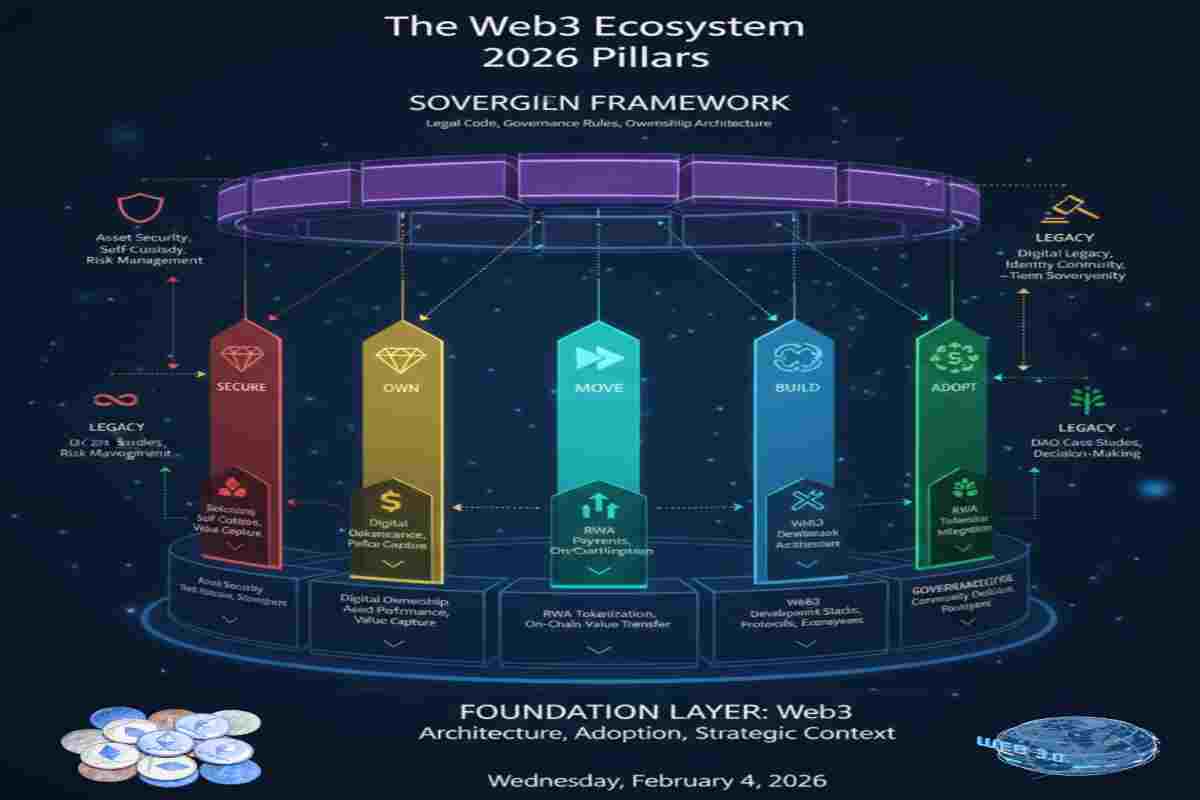
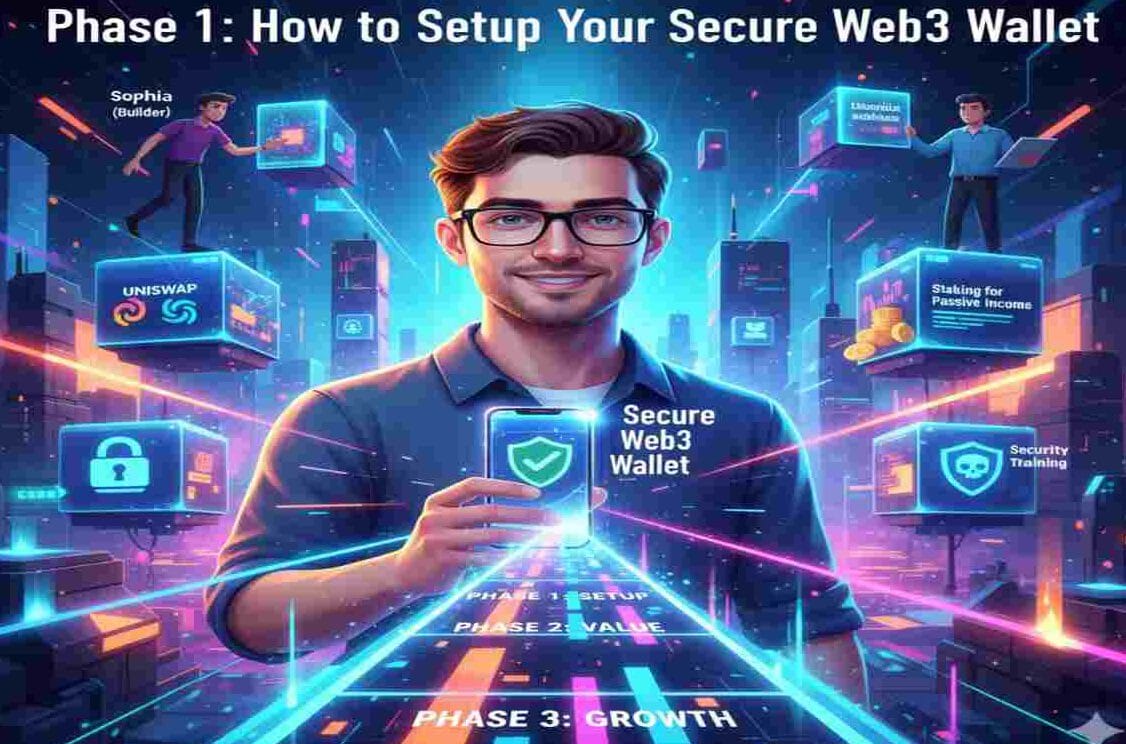
As part of the SECURE pillar, this guide focuses on digital asset protection, custody architecture, and institutional-grade risk management in Web3.
Explore related pillars:
Each pillar functions independently while forming a complete sovereign Web3 lifecycle model.
For a project titled Digital Asset Security & Sovereignty (2026)”, Excel templates are useful for mapping architecture, planning adoption, evaluating technologies, and measuring impact. Below is a practical set of Excel template types you can use for Web3 ecosystem design and strategy.
Purpose: Ensure personal and organizational digital asset security.
To access the full template set and start building your Secure Pillar today, Click Here.
To help you navigate the complexities of decentralized decision-making in 2026, we have organized the most critical inquiries into thematic groups. This structure ensures you can quickly find expert insights rooted in real-world successes and historical failures.
What is Asset Security 2026 and why does it matter?
Role of Account Abstractionin institutional custody*
Core cryptographic primitives*
Account Abstraction’s relation to MPC and multisig
Why Account Abstractionis a security innovation* fix para
Standards that govern Account Abstraction
Can Account Abstraction eliminate seed-phrase vulnerability?
When Security risks remain in Account Abstraction?
How does Account Abstraction compare to hardware wallets for enterprise?
What are Custodial threat models in Digital Asset Security?
What compliance frameworks apply to Account Abstraction custody
What is Risk modeling for institutions using Account Abstraction
What is Institutional ROI for Account Abstraction Security
What are Treasury management use cases for Account Abstraction?
What are Regulatory considerations apply to Account Abstraction?
How does Incident response work with Account Abstraction
What are Composability risks in Account Abstraction
What is Quantum resistance in Account Abstraction architecture?
What is the AI agent risk to Account Abstraction
What is Stress testing Account Abstraction Security?
What are Account Abstraction recovery policies
What is Legal accountability in Account Abstraction taxes
How does Account Abstraction support regulatory reporting
What are Session keys in enterprise access control?
What is Account Abstraction wallet incident logging?
What is Disaster recovery planning in Digital Asset Custody?
What Operational KPIs measures Account Abstraction performance?
Asset-Security Asset security in 2026 is no longer a defensive tax; it is a competitive lever. Institutions that rely on legacy custody models will find themselves unable to participate in high-frequency on-chain markets due to the friction of manual approvals and the binary nature of key-based risk.
Institutional-ROI The transition to Account Abstraction represents the “Great Hardening” of digital finance. It moves the industry away from the fragile “single point of failure” era into a period of programmable, resilient, and auditable governance.
CISO-Strategic-Plan For the CISO, the roadmap is clear:
The institutions that thrive in 2026 will be those that treat their wallet not as a vault, but as an operating system and as an execution environment governed by enforceable logic.
Asset security in 2026 is no longer defined by how well secrets are hidden. It is defined by how precisely actions are governed.
Account Abstraction represents the maturation of blockchain custody from static key management to programmable security architecture.
Institutions that adopt AA gain:
• Reduced catastrophic risk
• Faster operational throughput
• Lower audit friction
• Machine-native automation capability
• Future-ready cryptographic flexibility
CISOs are no longer securing vaults. They are securing operating systems.
That architectural decision will determine who scales securely — and who remains constrained by legacy assumptions.
Mastering Asset Security 2026 is the prerequisite for building long-term wealth on the sovereign internet. By shifting to Account Abstraction, you remove the “fear factor” and replace it with a professional, institutional-grade framework.
My transition from the derivatives markets of Karachi to the private equity world of Dallas taught me one thing: The most successful investors are those who manage risk before they manage returns.
Take the Next Step in Your Sovereign Journey Securing your “Digital Fortress” is the first critical step. Explore our next deep-dive: [The Rise of Real Yield: How to Spot Sustainable Revenue in 2026] to learn how to put your secured capital to work.
To ensure your Web3 Infrastructure aligns with the latest On-Chain Compliance and safety standards, we recommend reviewing the primary technical documentation for the standards mentioned in this guide.
Official Technical Reference: Ethereum ERC-4337 Documentation (Account Abstraction)

Welcome to OwnProCrypto (Own & Pro Crypto) — a next-generation Bitcoin and blockchain education platform where the science of finance meets the power of AI-driven automation.
Our mission is simple: to equip you with the knowledge, frameworks, and tools needed to make smarter financial and business decisions in the Web3 economy.
Beyond analysis, OwnProCrypto focuses on transparency, verifiable data, and practical frameworks that investors and builders can actually use. Our goal is not hype — but clear thinking, disciplined analysis, and long-term value creation in the decentralized economy.
Our Background
As part of the Web3 Ecosystem Architecture pillar, this guide focuses on Sovereign Ownership Architecture in Web3. Explore related pillars: