
This guide answers 40 essential crypto security questions
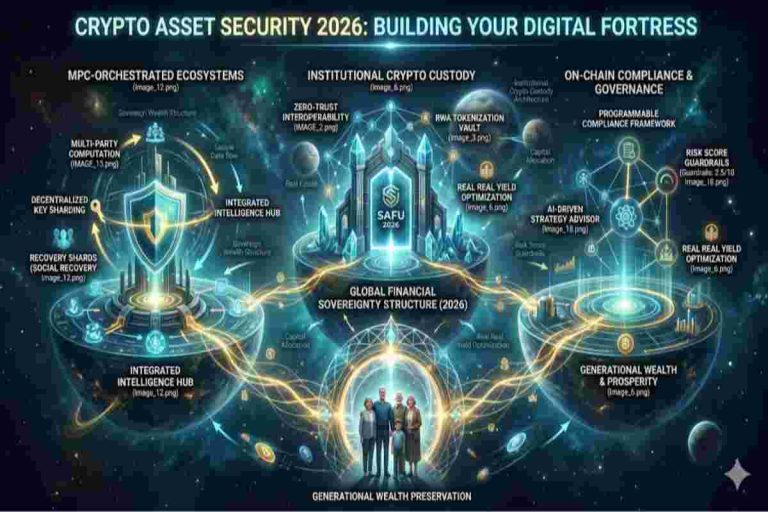
Table of Contents
ToggleCryptocurrency gives you something traditional finance never could: full control over your money. But with that control comes a serious trade-off—you are entirely responsible for your own security.
There’s no bank to reverse a transaction. No customer support to recover lost funds. If your crypto is stolen, it’s usually gone for good.
As adoption grows, so do threats. Hackers, scammers, and social engineering attacks are becoming more sophisticated, targeting both beginners and experienced investors.
This guide brings together the most important principles, strategies, and practices to help you protect your cryptocurrency from hacks, scams, and costly mistakes—whether you’re just starting or managing a large portfolio. This Article belongs to the Institutional Infrastructure Layer. Selecting the right model is a critical technical requirement for the Asset Security 2026: Setting Up Your Digital Fortress with Account Abstraction framework. Review Fireblocks for institutional security benchmarks.

At the core of crypto security is one concept: private keys.
Your private key (or seed phrase) is what gives you control over your funds. Whoever has access to it controls your crypto—no exceptions.
This is very different from banking. You don’t “log into” crypto—you prove ownership through cryptographic keys.
Never share your seed phrase. Ever.
No legitimate platform, wallet, or support agent will ask for it. If someone does, it’s a scam—guaranteed.
Most losses don’t happen reason complex hacks—they happen due to simple mistakes:
Avoiding these alone puts you ahead of most users.

Hardware wallets store your private keys offline, making them resistant to online attacks. Software wallets are faster and easier to use but rely on device security.
A smart setup uses both:
Table: Wallet Types Comparison
| Wallet Type | Connectivity | Security Level | Best Use Case |
|---|---|---|---|
| Hot Wallet | Online | Medium | Daily transactions |
| Cold Wallet | Offline | High | Long-term storage |
| Hardware Wallet | Offline Device | Very High | Large holdings / savings |

For long-term holding:
Your backup is your seed phrase. Without it, recovery is impossible.
Best practices:
Your recovery phrase must be protected from:
Using durable materials and secure storage is essential.
Table: Crypto Storage Methods & Risk Levels
| Storage Method | Risk Level | Notes |
|---|---|---|
| Exchange Storage | High | Custodial risk |
| Mobile Wallet | Medium | Device-dependent |
| Hardware Wallet | Low | Best balance of security |
| Multi-Signature Setup | Very Low | Advanced security |
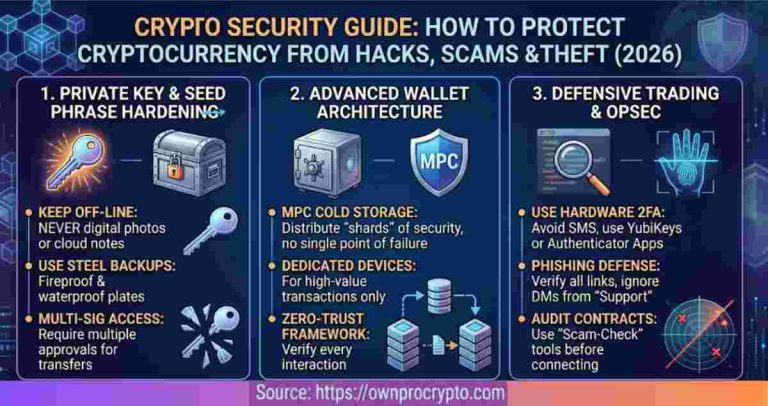
Always enable 2FA on exchanges and email accounts. Avoid SMS-based 2FA—use app-based or hardware solutions instead.
Your email password is especially critical—it can unlock everything else.
Your wallet is only as secure as your device:

Scammers manipulate trust, urgency, and fear.
If something feels rushed or “too good to be true,” it usually is.
📊 Table 3: Common Crypto Scams & Warning Signs
| Scam Type | Warning Sign |
|---|---|
| Fake Airdrop | Requires wallet connection |
| Giveaway Scam | Promises guaranteed returns |
| Fake Support | Messages you first |
| Phishing Site | Slightly altered URL |
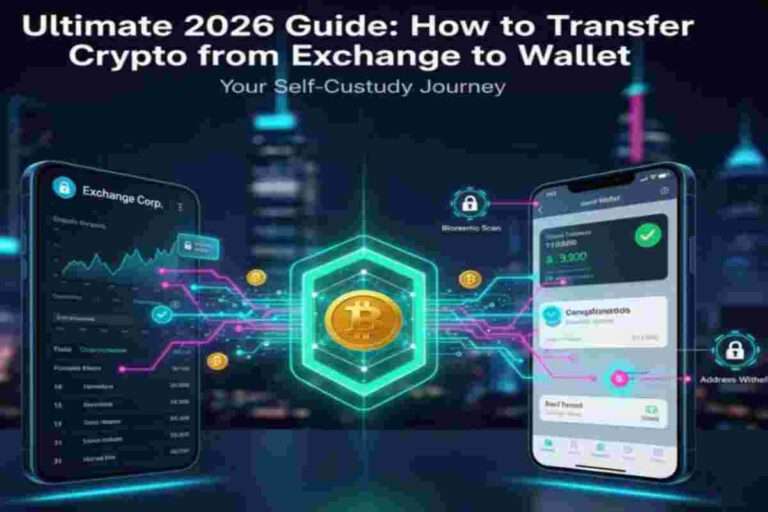
They can be secure—but they’re not risk-free. You don’t control your funds while they’re on an exchange.
Use exchanges for transactions—not storage.
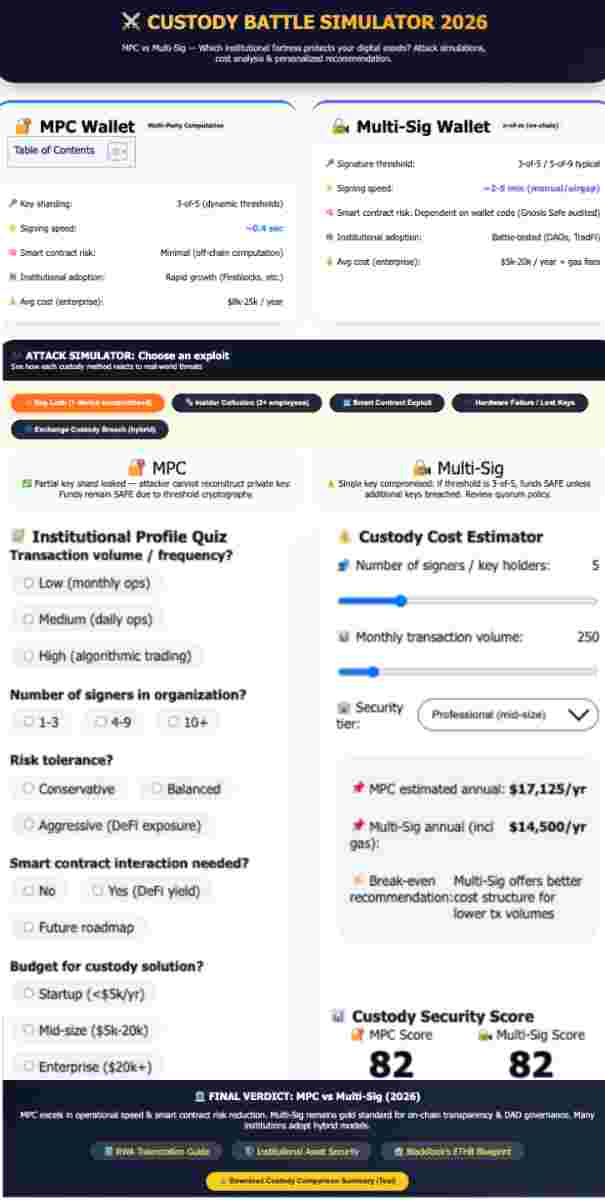
Multi-signature wallets require multiple approvals to access funds, reducing single points of failure.
In most cases, recovery is extremely difficult. Prevention is your best defense.
Security works best in layers:
As your holdings grow, your security should evolve:
Crypto rewards those who take responsibility—and punishes those who don’t.
Security isn’t a one-time setup. It’s an ongoing process of awareness, discipline, and smart decision-making.
By applying the principles in this guide, you’re not just protecting your assets—you’re building a system that can withstand both digital and human threats.
In a space where mistakes are permanent, being cautious isn’t optional—it’s essential.
Protecting your crypto comes down to controlling access to your private keys. The safest approach is to store your assets in a hardware wallet like Ledger Nano X or Trezor Model T, which keeps your keys offline and away from hackers.
You should also:
Think of it like this: your crypto is only as safe as the weakest point in your setup.
👉 Learn how to build a complete protection system:
https://ownprocrypto.com/asset-security-2026/
👉 For a deeper risk + execution framework:
https://ownprocrypto.com/crypto-trading-intelligence-risk-systems/
The safest method is cold storage. Hardware wallets isolate your keys from the internet.
Advanced users may use multi-signature setups and distributed backups. Avoid leaving funds on exchanges for long-term storage.
👉 Start with a safe beginner setup:
https://ownprocrypto.com/crypto-for-beginners/
A secure platform is defined by transparency, strong security controls, and a proven track record.
Look for proof of reserves, withdrawal protections, and regulatory positioning.
👉 See a full exchange breakdown:
https://ownprocrypto.com/binance-review-2026/
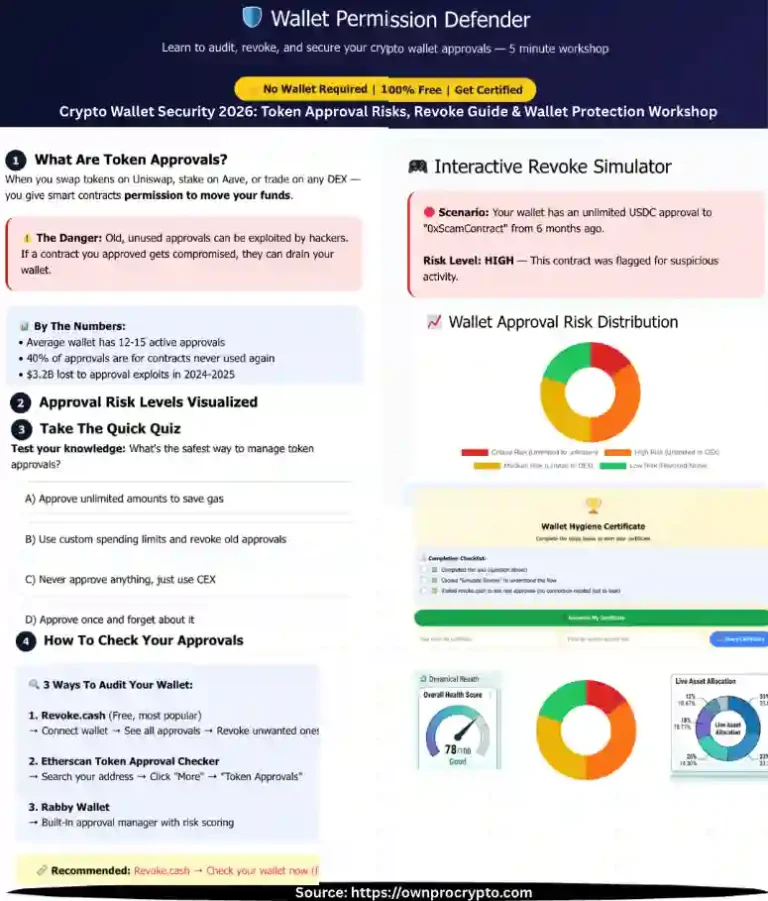
Act immediately: move remaining funds, revoke permissions, and secure all access points.
👉 Follow a structured recovery process:
https://ownprocrypto.com/web3-decision-lab/
Only for short-term use. Exchanges are tools—not storage.
👉 Learn how to transition to full control:
https://ownprocrypto.com/crypto-self-custody-security-toolkit/
Scams exploit urgency and trust. Always verify before acting.
👉 Use this to check suspicious platforms:
https://ownprocrypto.com/crypto-scam-checker/
Use both strategically:
👉 See full setup strategy:
https://ownprocrypto.com/asset-security-2026/
2FA adds a critical second layer of protection. Avoid SMS-based authentication and use app or hardware-based options.
👉 Build your full security checklist:
https://ownprocrypto.com/crypto-security-checklist/
Hackers exploit behavior—not blockchain weaknesses.
👉 Learn how to filter risky actions before execution:
https://ownprocrypto.com/crypto-trade-filtering-system/
In most cases, no. Prevention is the only reliable strategy.
👉 Understand risk management systems:
https://ownprocrypto.com/digital-asset-risk-management-framework/
Use trusted platforms and verify everything before acting.
👉 Beginner-safe buying guide:
https://ownprocrypto.com/crypto-for-beginners/
Hot wallets are connected to the internet; cold wallets are offline and far more secure.
👉 Learn how to structure both safely:
https://ownprocrypto.com/asset-security-2026/
Always verify URLs and sources before interacting.
👉 Check suspicious links here:
https://ownprocrypto.com/crypto-scam-checker/
Security, transparency, and control features are key.
👉 Compare custody architectures:
https://ownprocrypto.com/mpc-vs-multi-sig-vs-hsm-custody/
Crypto gives control—but removes safety nets.
👉 Understand financial sovereignty:
https://ownprocrypto.com/financial-sovereignty/
Use secure tools and minimize exposure.
👉 See full taxation strategy:
https://ownprocrypto.com/digital-asset-taxation/
Verify sources carefully and avoid ads or unknown publishers.
👉 Avoid common mistakes here:
https://ownprocrypto.com/top-blockchain-mistakes/
Limit exposure and use a separate wallet for travel.
👉 Build a secure setup:
https://ownprocrypto.com/crypto-self-custody-security-toolkit/
Watch for guaranteed returns, urgency, and lack of transparency.
👉 Understand token economics:
https://ownprocrypto.com/tokenomics-explained/
No—this significantly increases risk.
👉 Full security framework:
https://ownprocrypto.com/crypto-security-guide/
Use passphrases and layered access controls.
👉 Learn advanced ownership structures:
https://ownprocrypto.com/legacy-sovereignty/
Watch for unusual behavior and scan regularly.
👉 Run a full risk audit:
https://ownprocrypto.com/asset-risk-assessment/
Always test transactions before sending full amounts.
👉 Use structured decision systems:
https://ownprocrypto.com/crypto-trading-system/
Yes. You are not the true owner on exchanges.
👉 See market risk insights:
https://ownprocrypto.com/crypto-market-update/
Security is a layered system—not a single tool.
👉 Full institutional framework:
https://ownprocrypto.com/crypto-trading-intelligence-risk-systems/
No. Starting now gives you a major advantage.
👉 Begin here:
https://ownprocrypto.com/crypto-for-beginners/
Welcome to OwnProCrypto (Own & Pro Crypto) — a next-generation Bitcoin and blockchain education platform where the science of finance meets the power of AI-driven automation.
Our mission is simple: to equip you with the knowledge, frameworks, and tools needed to make smarter financial and business decisions in the Web3 economy.
Beyond analysis, OwnProCrypto focuses on transparency, verifiable data, and practical frameworks that investors and builders can actually use. Our goal is not hype — but clear thinking, disciplined analysis, and long-term value creation in the decentralized economy.
Our Background
Crypto Tools & Analysis:
Crypto Fundamental Analysis Tools | Protocol Evaluation System | DeFi Risk Analysis Tools | Crypto Portfolio Dashboard | Token Risk vs Reward Tool
Guides:
Crypto Fundamental Analysis | Blockchain Project Evaluation | Tokenomics Analysis | DeFi Protocol Analysis
© 2026 OwnProCrypto — Built for smarter crypto decisions